Applied Lessons from Product Security Teams in Vulnerability Management
Webinar Summary
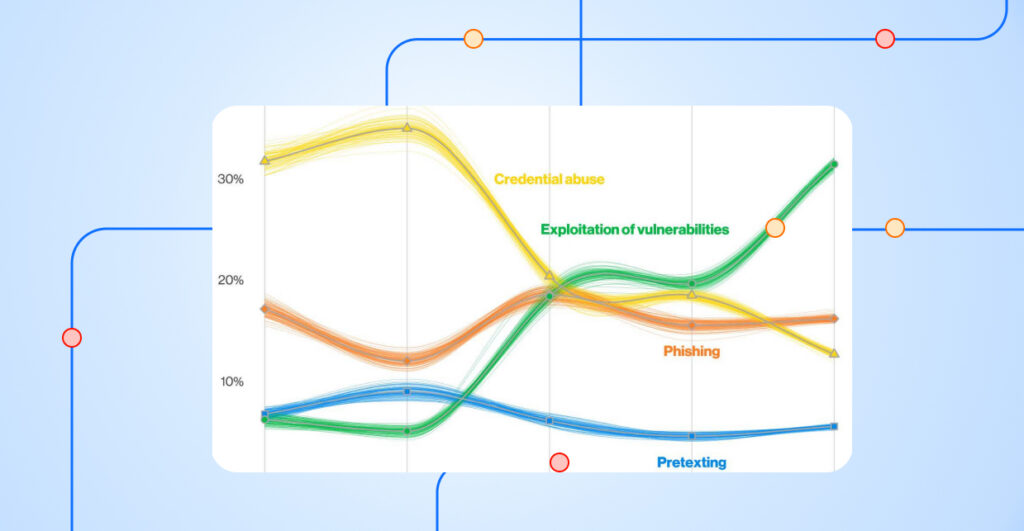
Navigating the world of cybersecurity requires an intricate understanding of the various facets of security operations. Among these, product security and vulnerability management are two critical areas that often intersect. However, the relationship, challenges, and priorities of these domains can vary significantly. This webinar seeks to shed light on this unique relationship by tapping into the insights of product security experts.
In this webinar, our panel of cybersecurity experts, including Patrick Garrity, Security Researcher at Nucleus Security, Scott Kuffer Co-Founder and COO at Nucleus Security, Matthew Clapham, Senior Director of Product Security Trust Center at Activision Blizzard, and a surprise expert guest, will dive deep into the nexus of product security and vulnerability management. Drawing from their vast experience, they’ll unravel the intricacies of this relationship and provide practical solutions to the challenges at hand.
By the end of our session, participants will:
- Recognize the distinction between product security and vulnerability management.
- Be equipped with knowledge about the challenges developers face in their pursuit of security.
- Glean valuable insights into the operational strategies of product security teams.
- Obtain actionable tactics to encourage synergy between these two vital security units.
- Understand the essence of cultivating a unified, trust-based security environment.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.