UNIFIED EXPOSURE MANAGEMENT
Turn Exposure into Action
Unify fragmented security findings, prioritize risk with AI-driven intelligence, and mobilize remediation to scale exposure reduction
TRUSTED BY ORGANIZATIONS WORLDWIDE
ANALYST RECOGNITION
A Leader in Vulnerability and Exposure Management

Gartner Exposure Assessment Platform Magic Quadrant
Nucleus Security recognized as a Challenger by Gartner.
READ MORE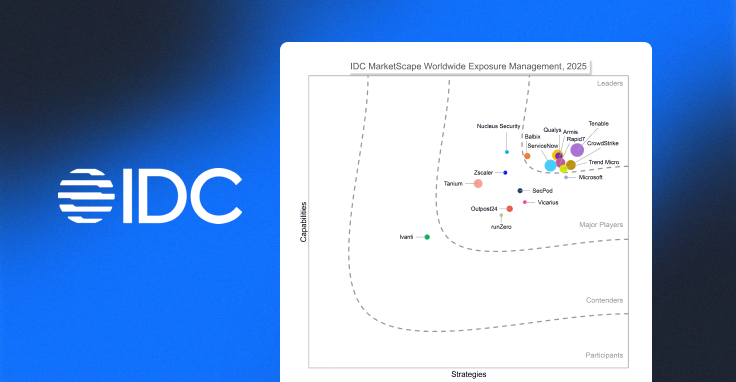
IDC MarketScape 2025: Worldwide Exposure Management
Nucleus Security named a Major Player by IDC Marketscape.
READ MORE
Frost & Sullivan 2025 Transformational Innovation Leader
Nucleus stands out for its scalability, speed, and cyber risk reduction.
READ MOREScale and Automate Your Program
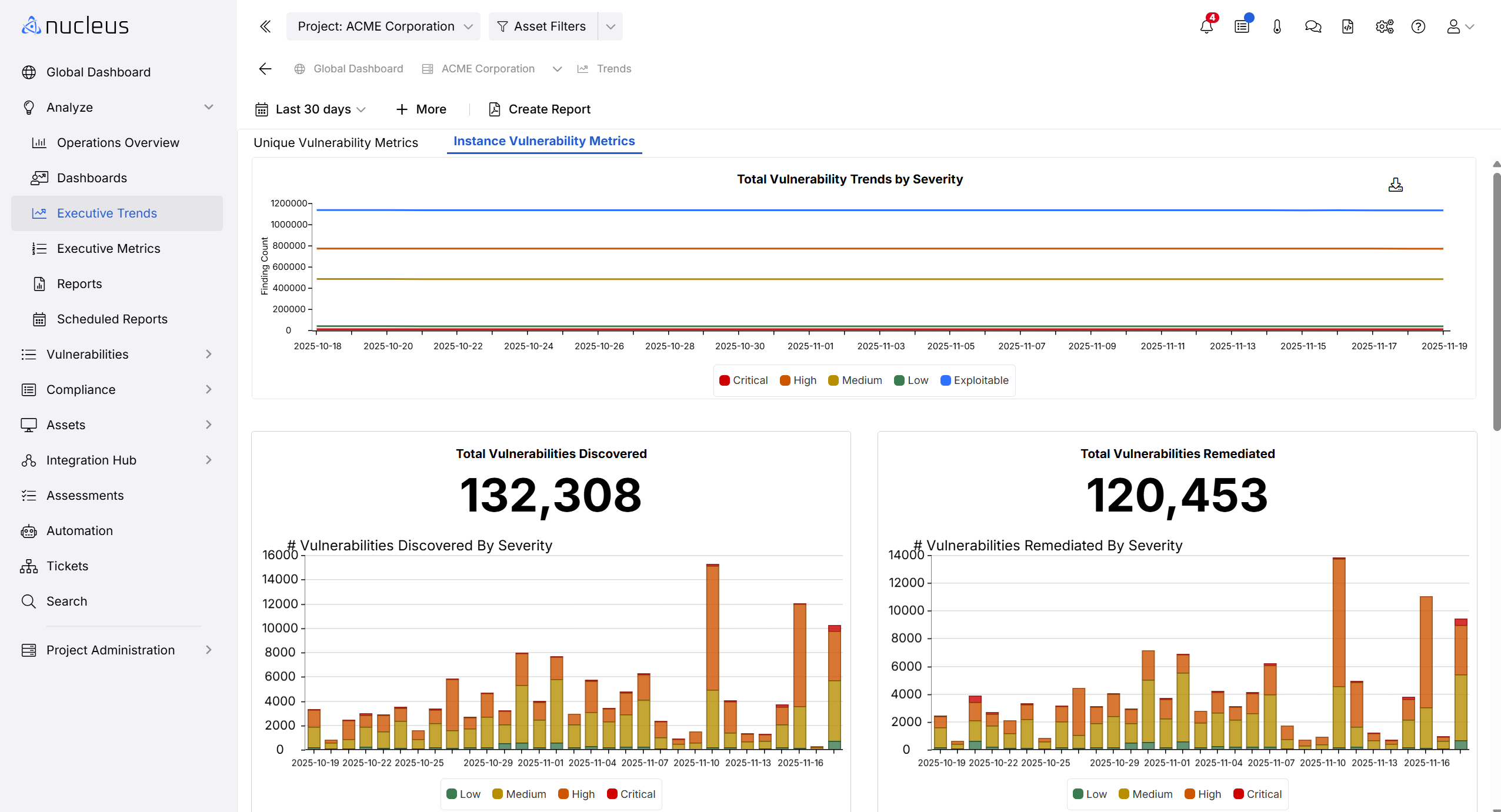
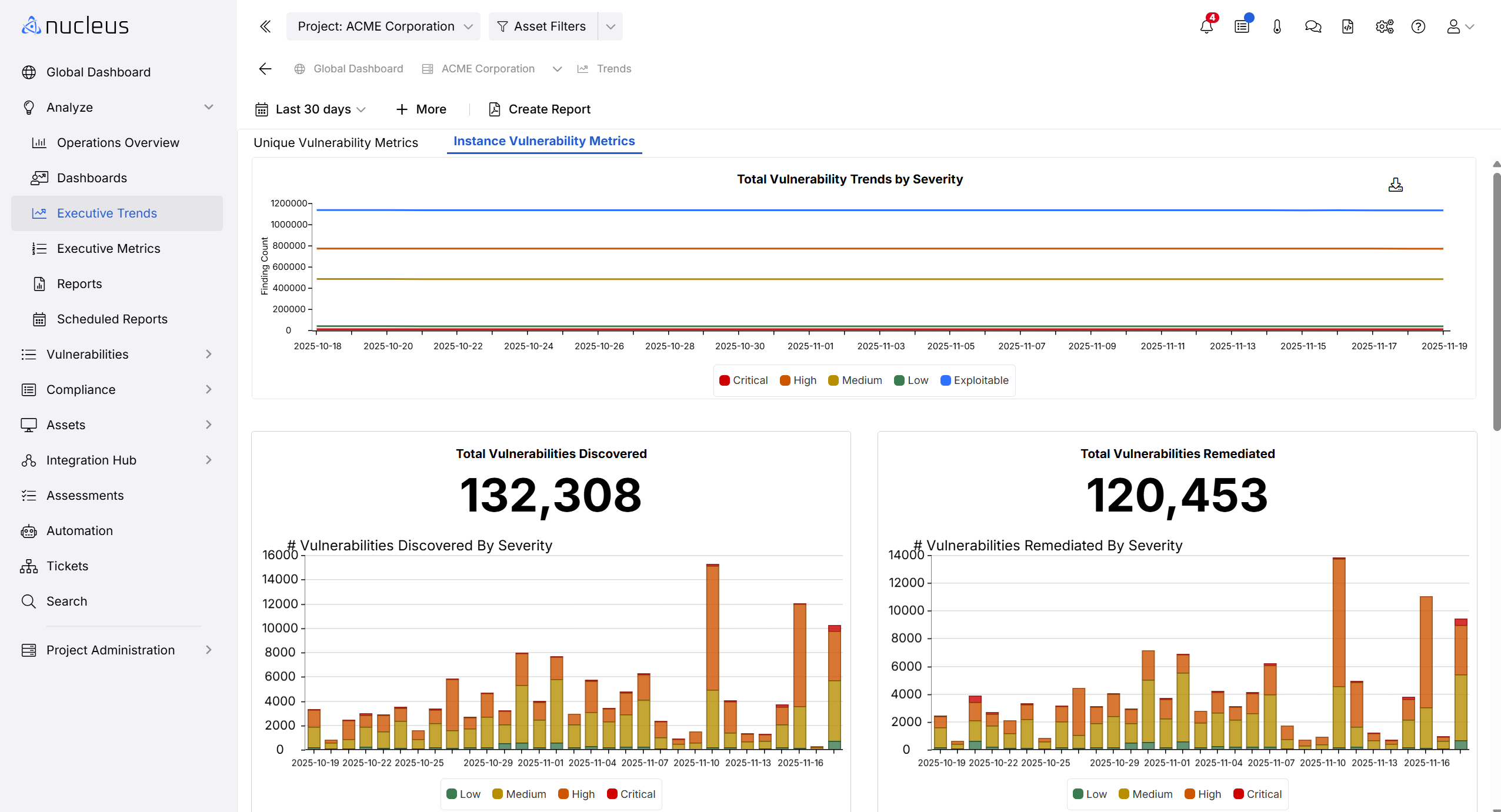
Automate your risk-based vulnerability management program to achieve stronger security outcomes.
Vulnerability & Security Findings Processed Daily
Critical Risks Prioritized for Immediate Action
Reduction in High-Priority Risks Within 3 Months
“If you want to build a program around Risk-Based Vulnerability Management, Nucleus is the engine to get you there.”
-Nick Nolen, VP and Deputy CISO
THE NUCLEUS SECURITY PLATFORM
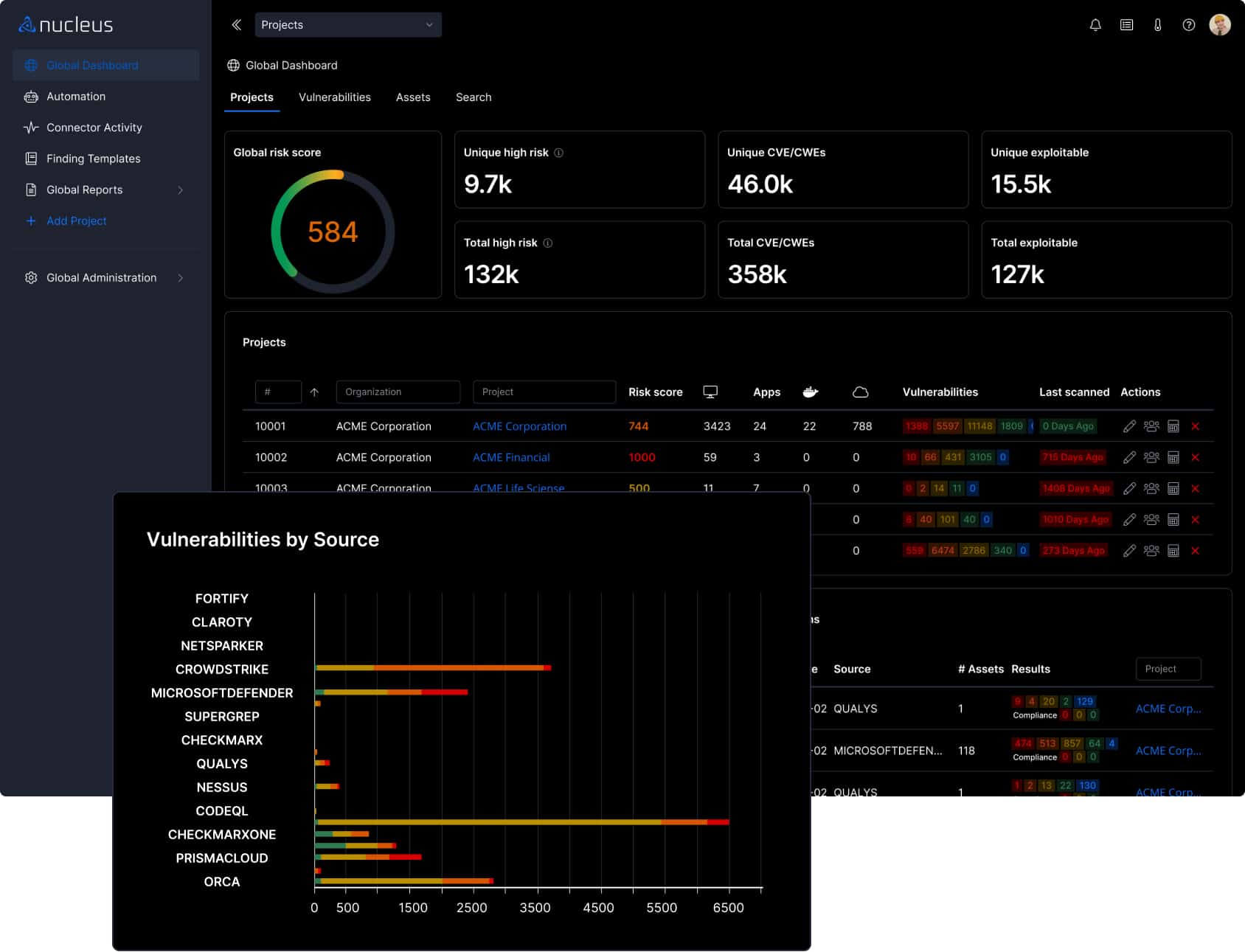
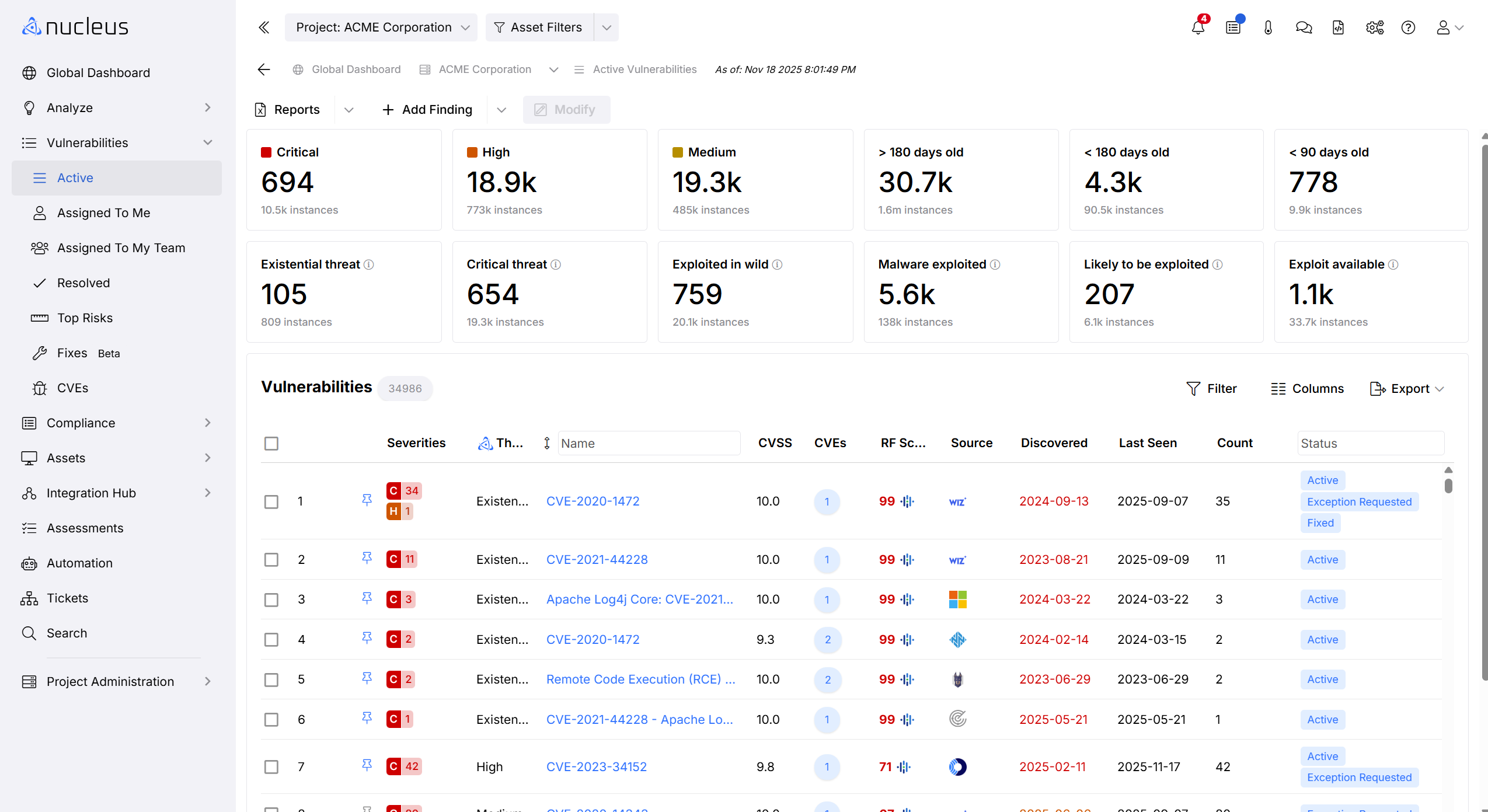
Manage All Your Vulnerabilities and Exposures in a Single Enterprise Platform
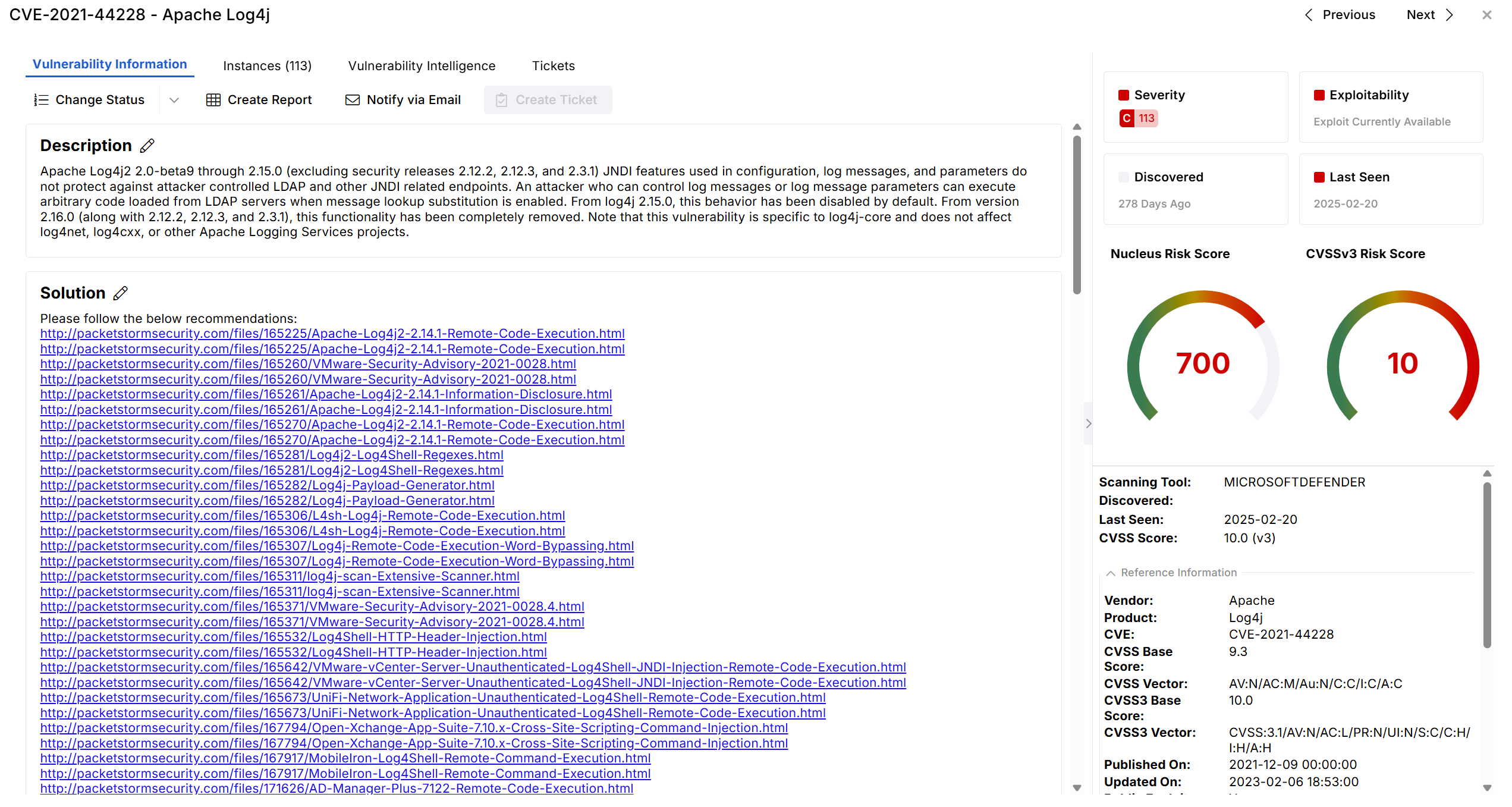
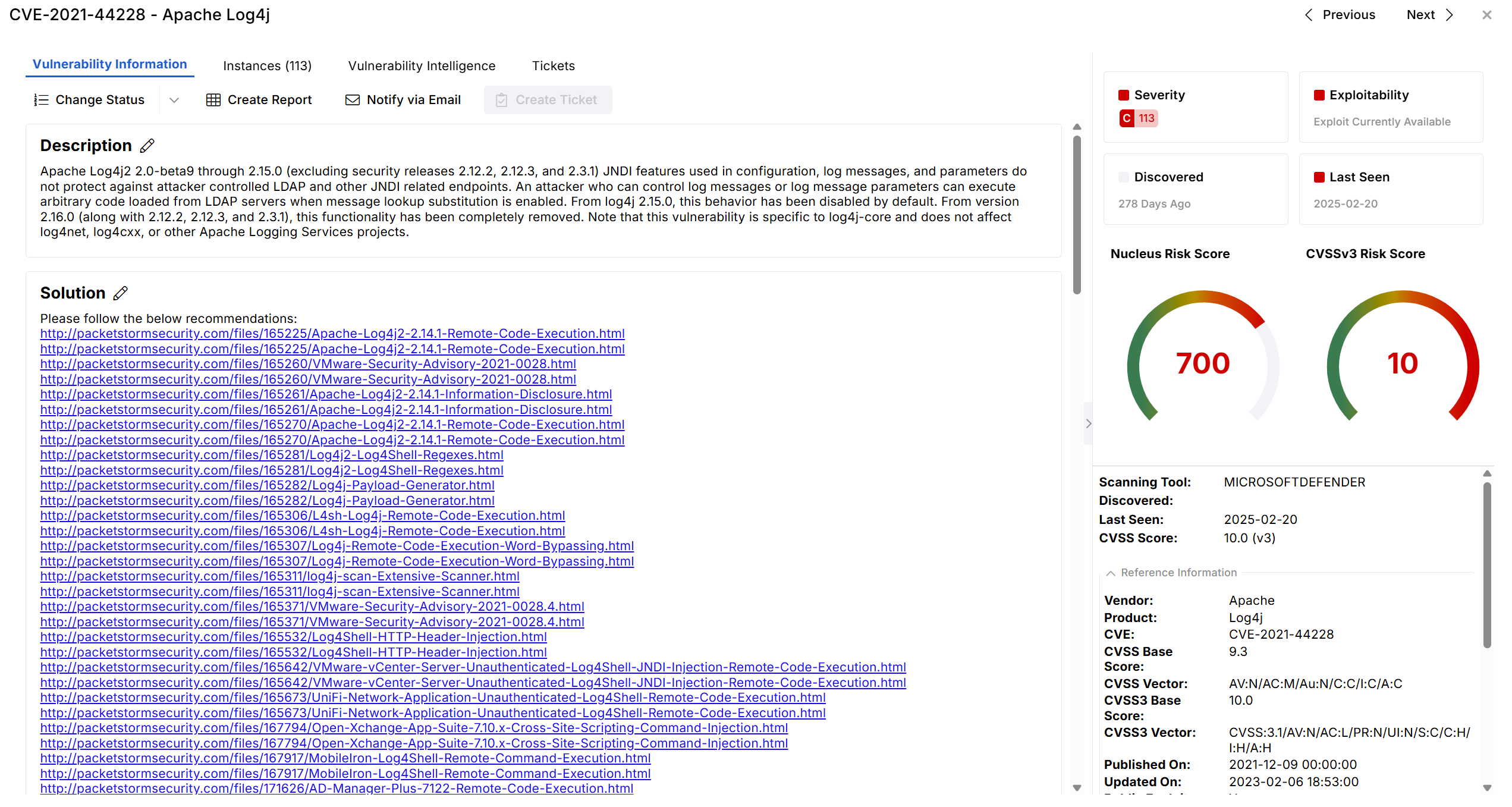
Enterprise security tools generate millions of findings every day. Nucleus is a vulnerability and exposure management platform for large enterprises, integrating vulnerability, threat, and asset data to help teams prioritize critical exposures with business context and threat intelligence.
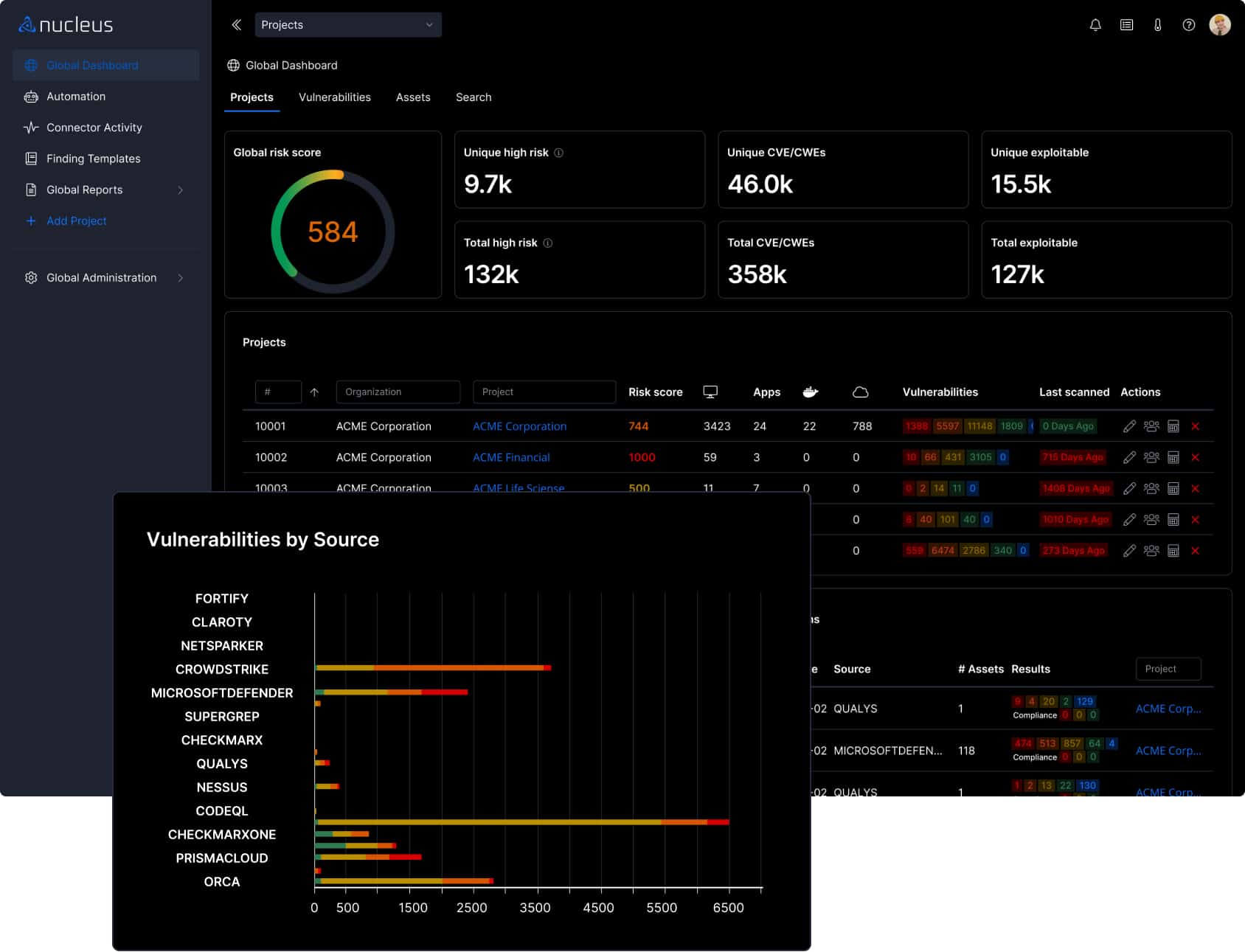
Unify Vulnerability Data
Ingest, correlate, and normalize data from all your tools into one hub to gain unified risk visibility and reporting.
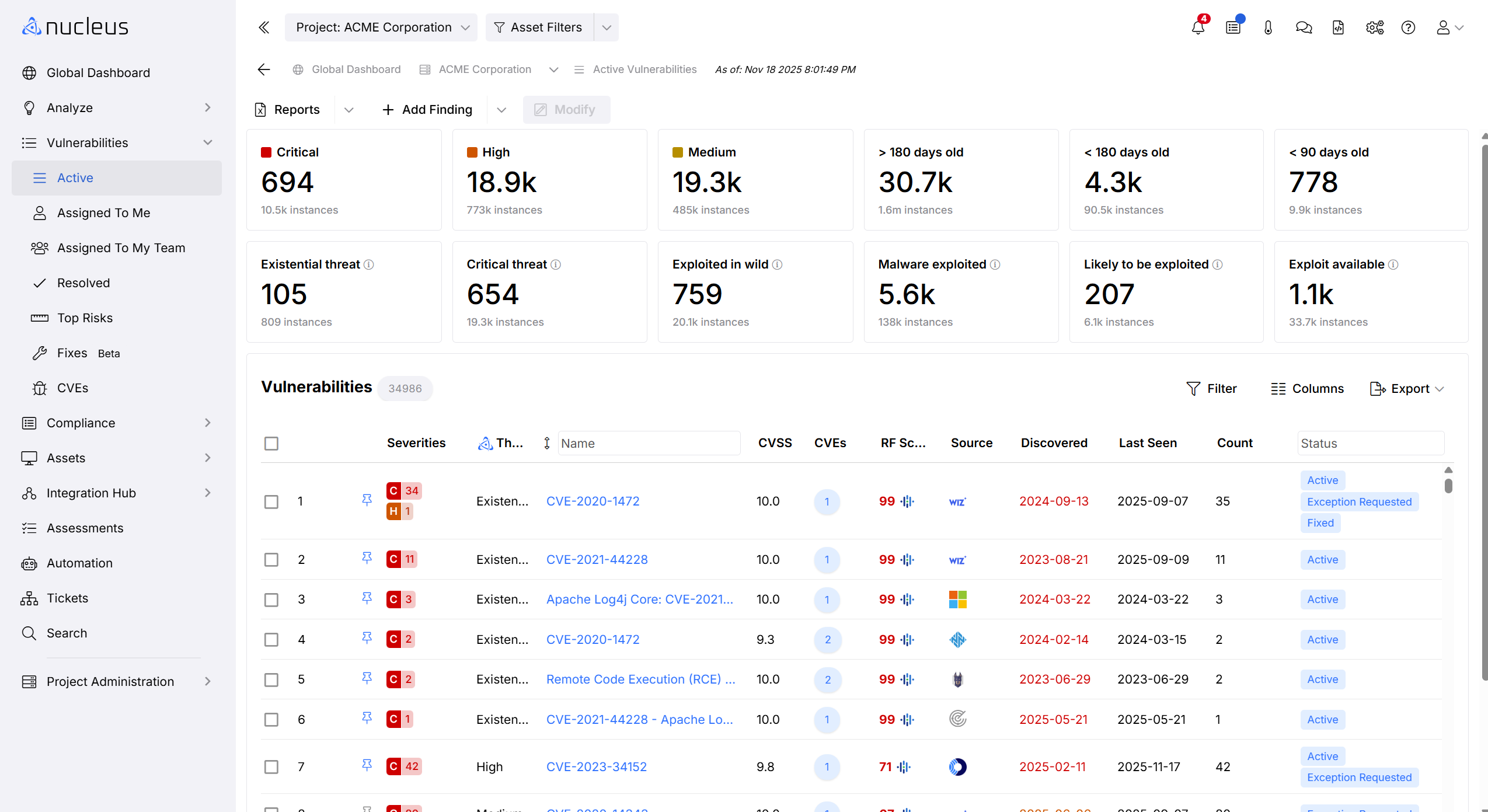
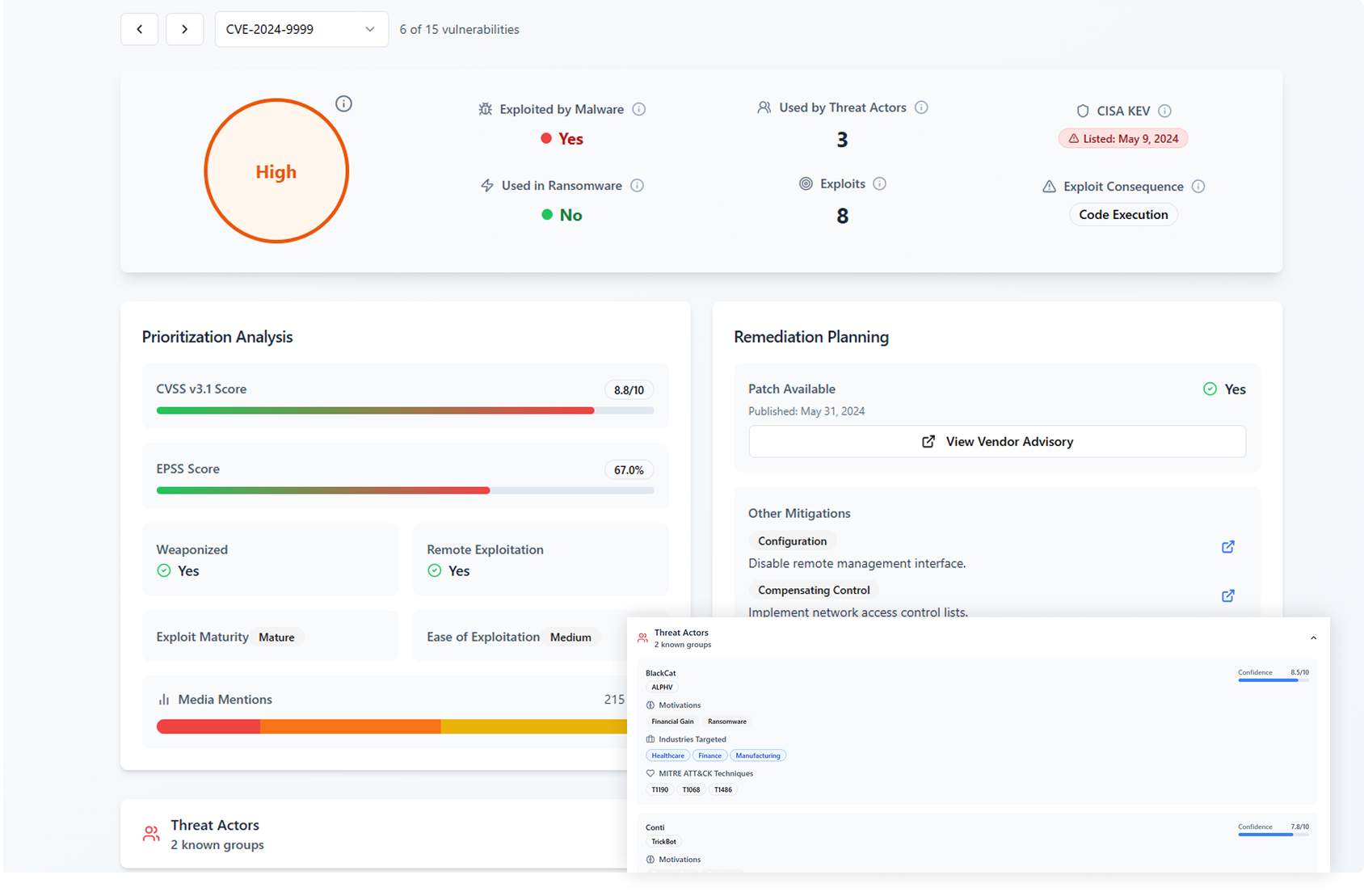
Prioritize Risk with Context
Customize risk scoring and prioritize risk with asset context and business impact to focus remediation on what matters most.
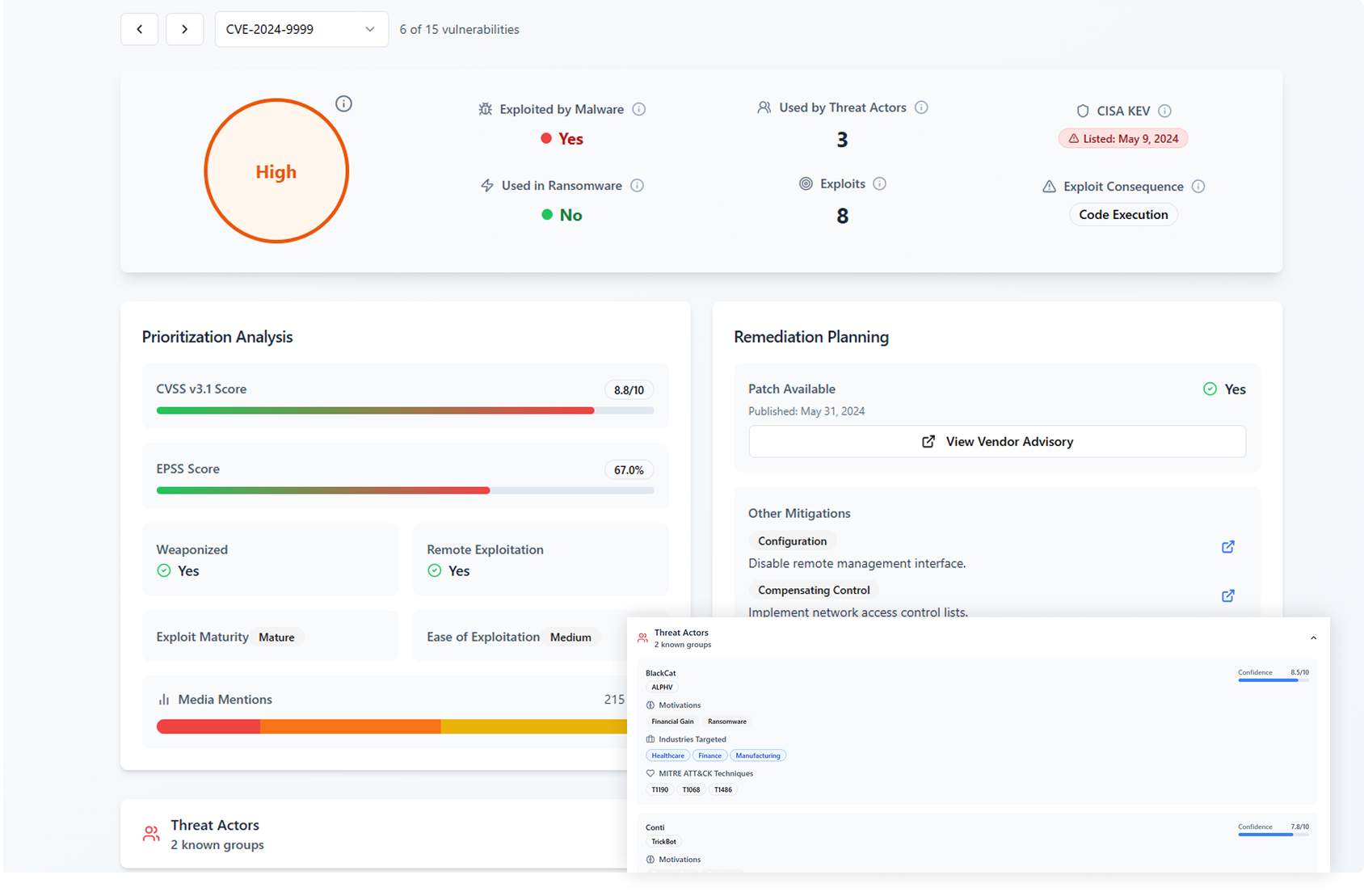
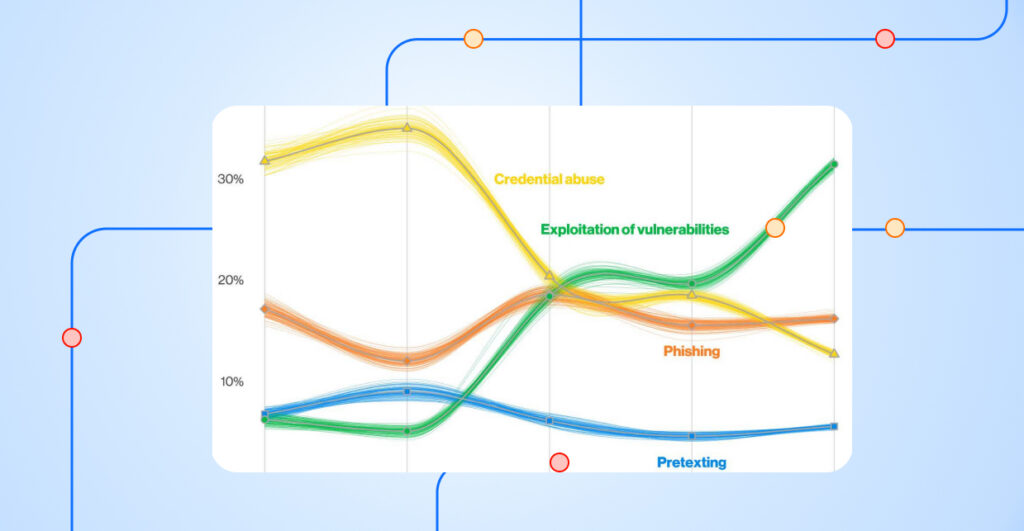
Enrich with Threat Intelligence
Correlate vulnerabilities with real-world threat data from AI-powered, expert-validated Nucleus Insights, CISA KEV, and EPSS to prioritize and predict actively exploited risks.
Remediate Faster and Smarter
Automate ownership assignment and ticketing using expedited and efficient workflows to remediate faster and smarter.
Automate Federal Compliance
Modernize your vulnerability management program to protect your critical infrastructure and stay compliant.
INTEGRATIONS
Over 200 Integrations to Connect to Any Source
Integrate data from security, asset, and threat intelligence tools across large enterprise environments with Nucleus’ 200+ built-in connectors and FlexConnect universal adapter.
SECURITY AND COMPLIANCE
Secure to the Core
Meet your stringent security and compliance requirements with Nucleus. Our platform is FedRAMP Moderate Authorized and SOC2 compliant.

ASSET MANAGEMENT
Unify and Automate Your Asset Management
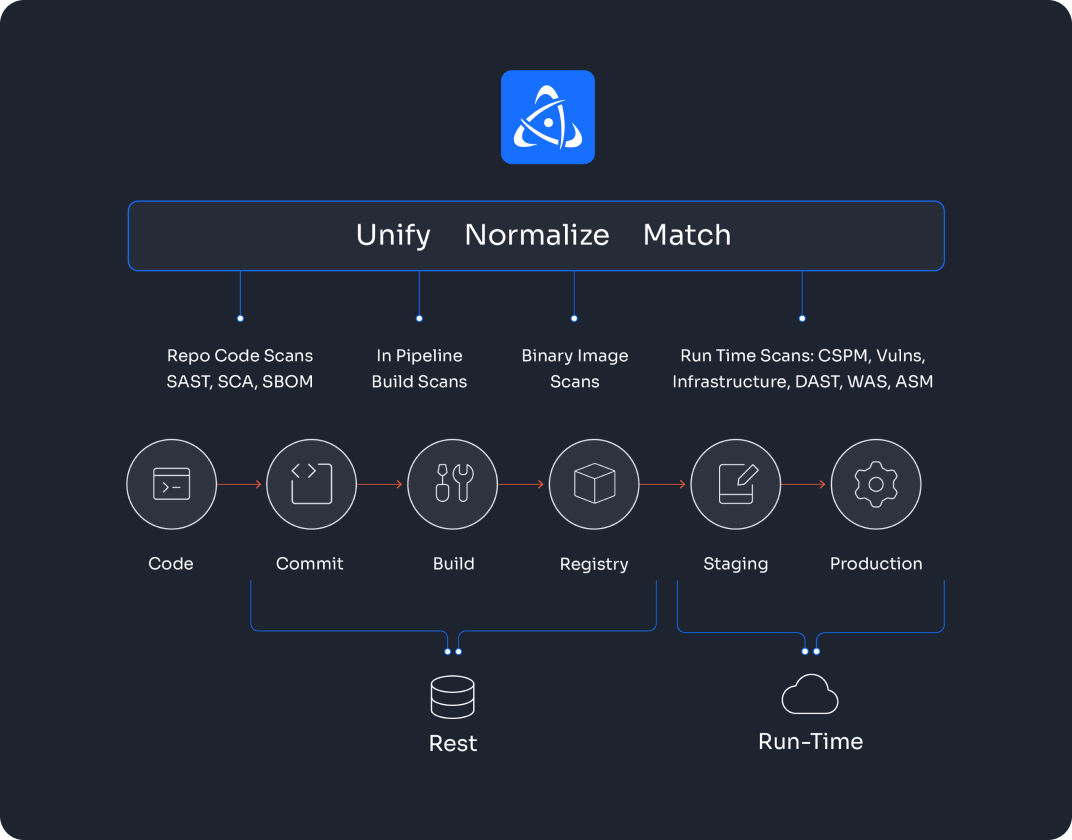
Unify and operationalize asset data to unlock business context and automate your vulnerability and exposure management. Only with the Nucleus platform, teams can automatically match assets from rest to runtime and deduplicate assets across tools and sources.
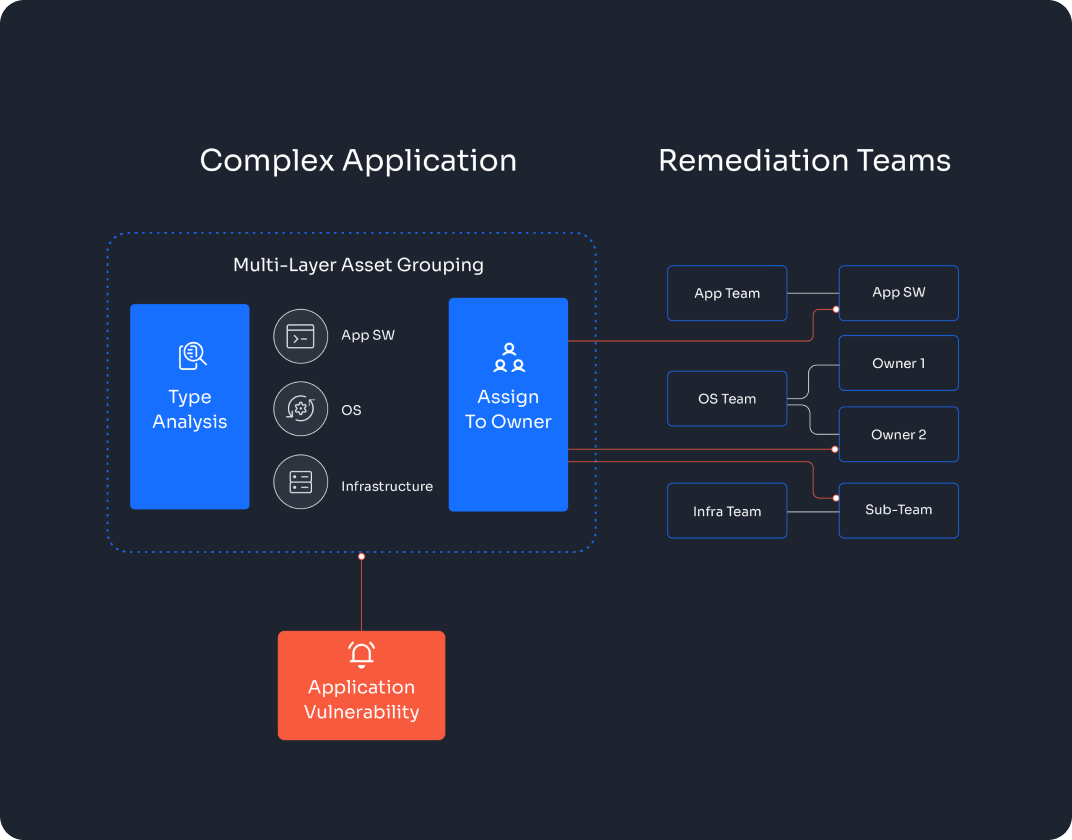
OWNERSHIP AUTOMATION
Automate Ticketing Assignment for Your Apps
DON’T TAKE OUR WORD FOR IT
Read What Our Customers Are Saying
“Before migrating to Nucleus, we weren’t really able to let our different teams actually see what we see.”





See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.