A First Look at CVSS V4.0 Next To CVSS V3.1
Updated on November 1, 2023
FIRST.org has announced the official publication of CVSS V4.0.
For those unfamiliar, the Common Vulnerability Scoring System (or CVSS, as it’s commonly referred) is an open framework for communicating the characteristics and severity of software vulnerabilities. CVSS produces a score ranging from 0 to 10 and categorizes these ratings as None, Low, Medium, High and Critical. (Check out this Nucleus Shortcuts video to learn more about how CVSS is used for Vulnerability Management.)
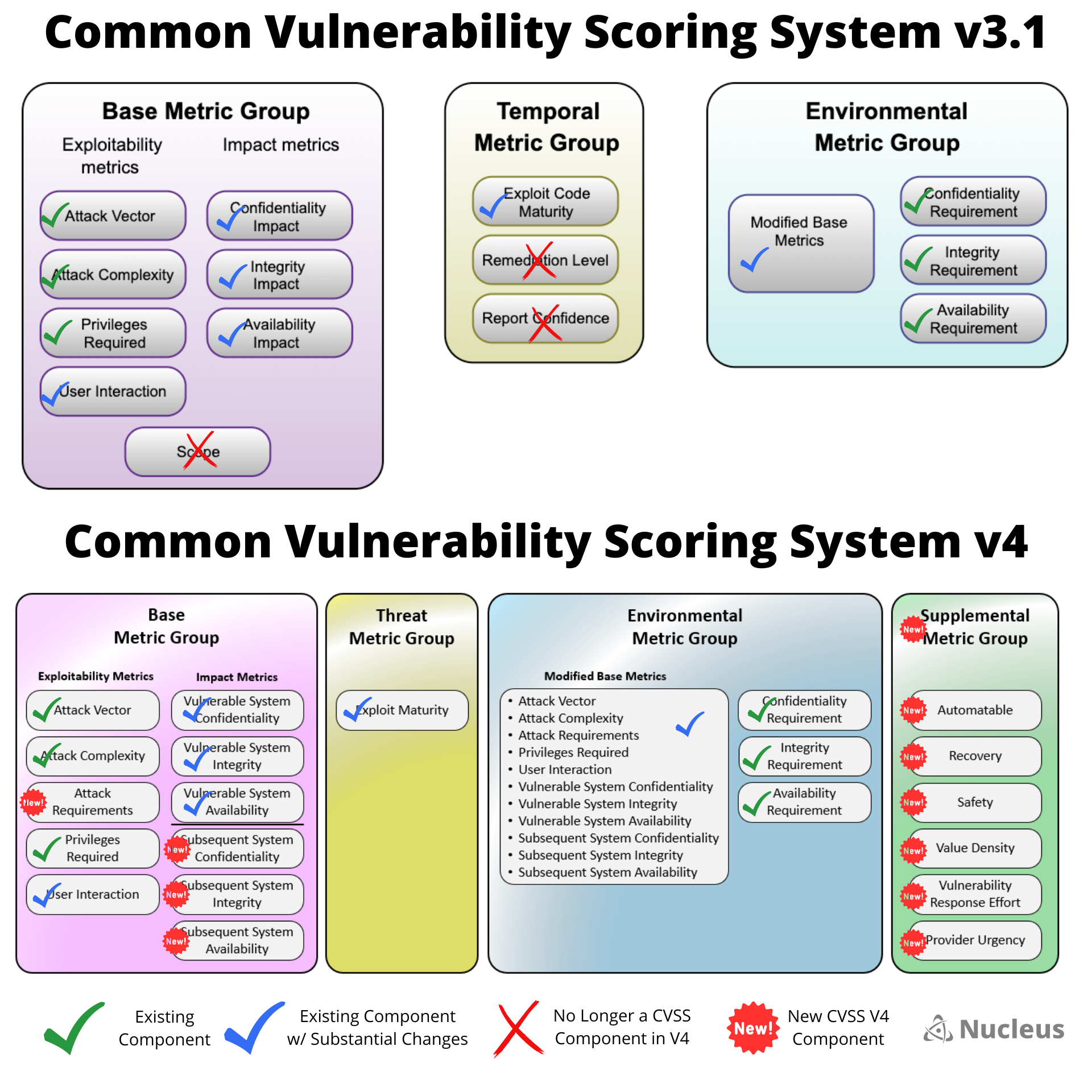
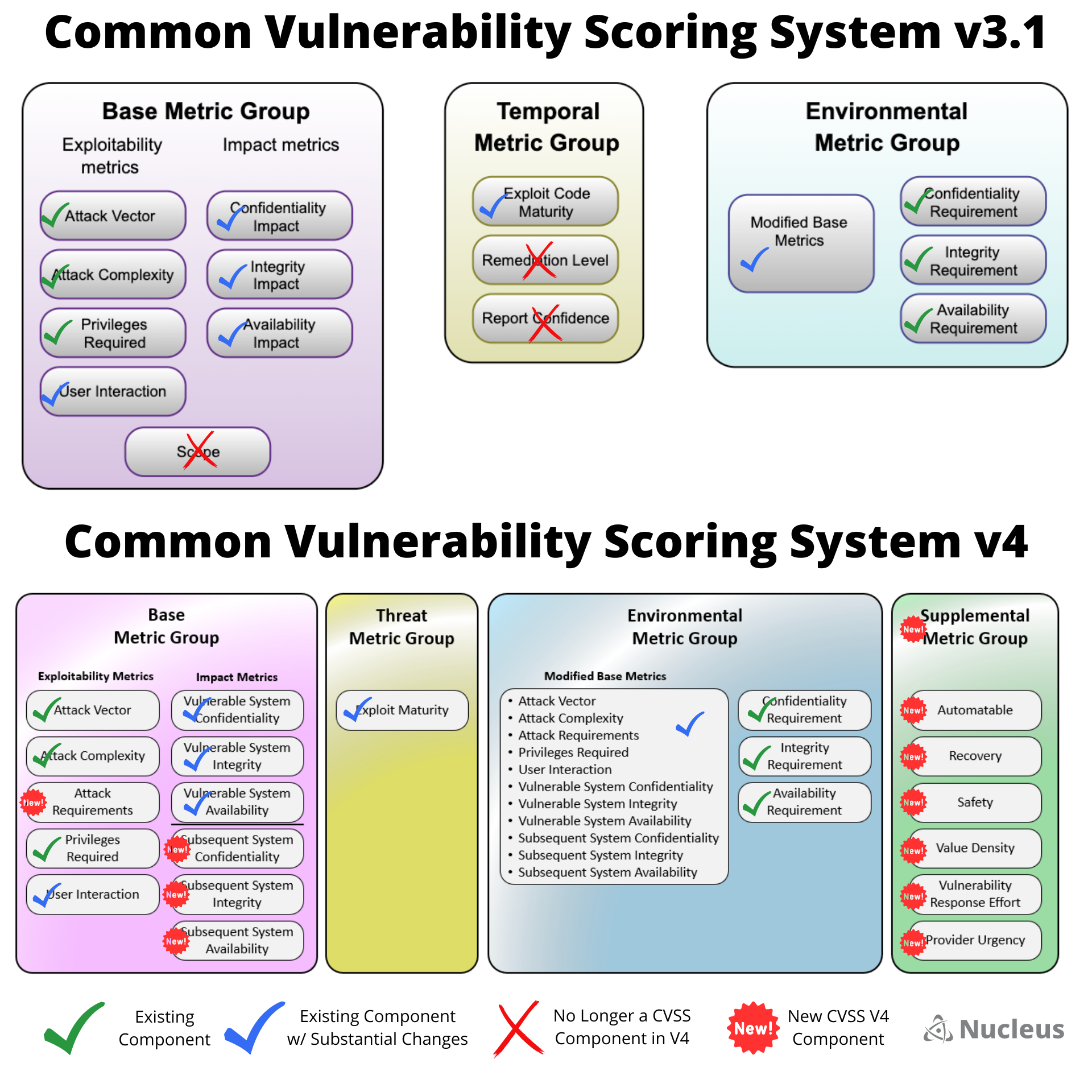
This new preview from FIRST brings some exciting changes to the CVSS V3.1 framework that most cybersecurity professionals have been using up until now, including:
- A reinforced concept that CVSS it not just the Base score
- Finer granularity through the addition of new Base metrics and values
- Enhanced disclosure of impact metrics
- Temporal metric group renamed to Threat metric group
- New Supplemental Metric Group to convey additional extrinsic attributes of a vulnerability that do not affect the final CVSS-BTE score
- Additional focus on OT/ICS/Safety
They have also introduced additional scoring systems that have been adopted to handle complimentary aspects of vulnerability assessment and patch priority, such as EPSS and SSVC. These welcome additions to the vulnerability scoring toolbox will help to provide innovative exploit prediction and decision support.
To help you understand the full differences between CVSS V3.1 and V4.0, we have created a visualization that compares the different metrics between each version:
Personally, our Nucleus team is intrigued by how the new scoring methodology in CVSS V4.0 will enhance vulnerability analysis. It has the potential to provide vulnerability analysts with more effective scoring, which would address some of the historical shortcomings of CVSS. For instance, the fact that there’s not enough real time threat and supplemental impact details represented, or that scores published by vendors are often High or Critical (7.0+).
This new update could also potentially lead to better assessments of the impact of vulnerabilities. However, it’s important to remain cautiously optimistic until the scoring itself demonstrates significant improvements. The changes in metrics are complex and require careful consideration to fully digest – even by our team.
Click here to check out the updates to CVSS V4.0
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.