Vulnerability Remediation with a Plan
Approach vulnerabilities in your environment with business context and intelligence about active exploits in the wild.
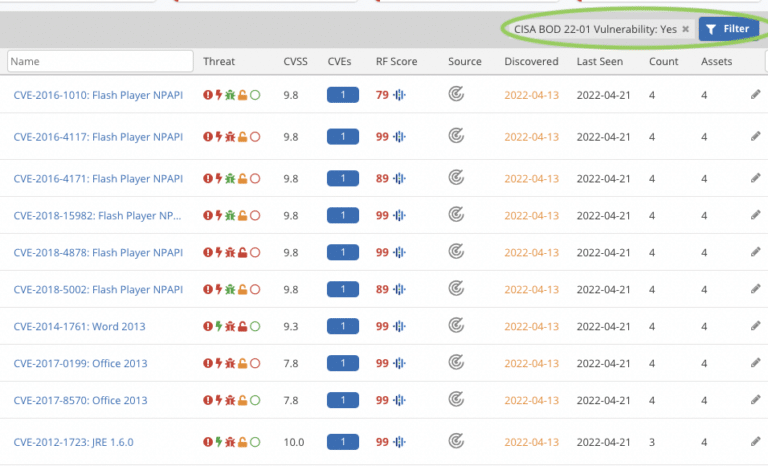
IDENTIFY
Identify CISA Known Exploited Vulnerabilities in Seconds
Identify which assets in your environment have known exploited vulnerabilities. Cross-reference CISA KEV with Mandiant threat intelligence, CVSS, and more.
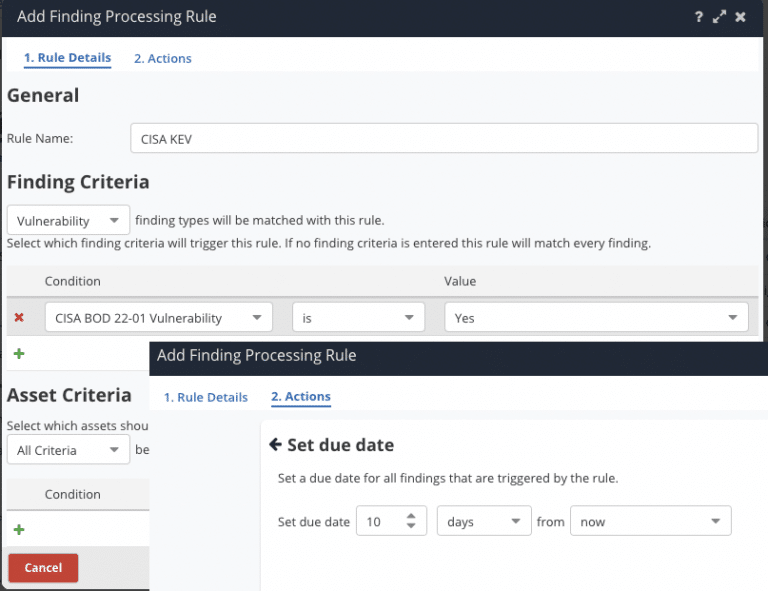
PRIORITIZE
Prioritize Remediation Based on CISA KEV
Use the CISA KEV catalog to prioritize remediation while automating workflows with integrations to ServiceNow, Jira, and other ticketing systems.
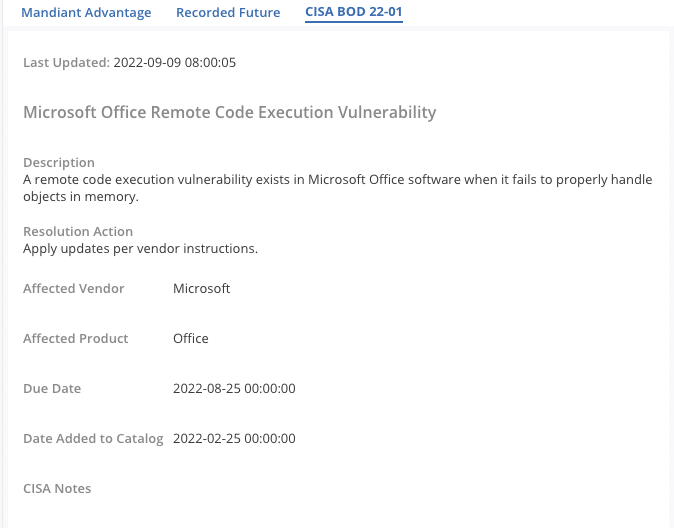
COMPLY
Meet CISA BOD 22-01 Federal Remediation Requirements
Track CISA KEV vulnerabilities to ensure federal compliance with CISA Binding Operational Directive 22-01.
RESOURCES
Discover the Latest From Nucleus
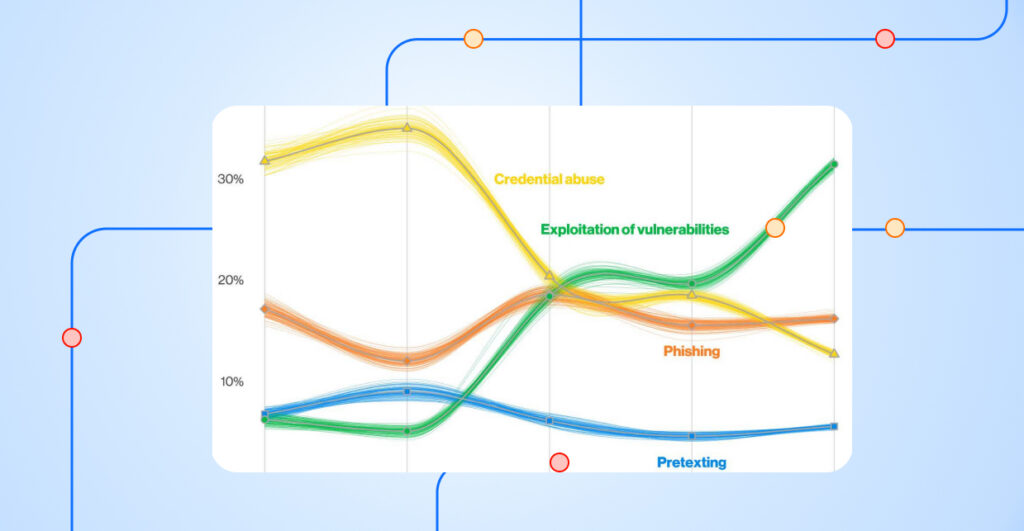
The Verizon 2026 DBIR Confirms the Shift from Vulnerability Management to Exposure Management
READ MORE
Public PoC Exploits are a Clear Signal for Defensive Action
Part 3 of 4 | The Exploitability Intelligence Gap Research Series
READ MORE
EPSS Score Is Predictive, but Late: What 18% of CISA KEV Vulnerabilities Reveal
Part 2 of 4 | The Exploitability Intelligence Gap Research Series
READ MOREWatch a Demo Today
Learn more about the Nucleus Unified Vulnerability Management platform right away.
Watch our in-depth, on-demand demo to see us in action.