Analyzing 925 Known Exploited Vulnerabilities in CISA’s KEV Catalog
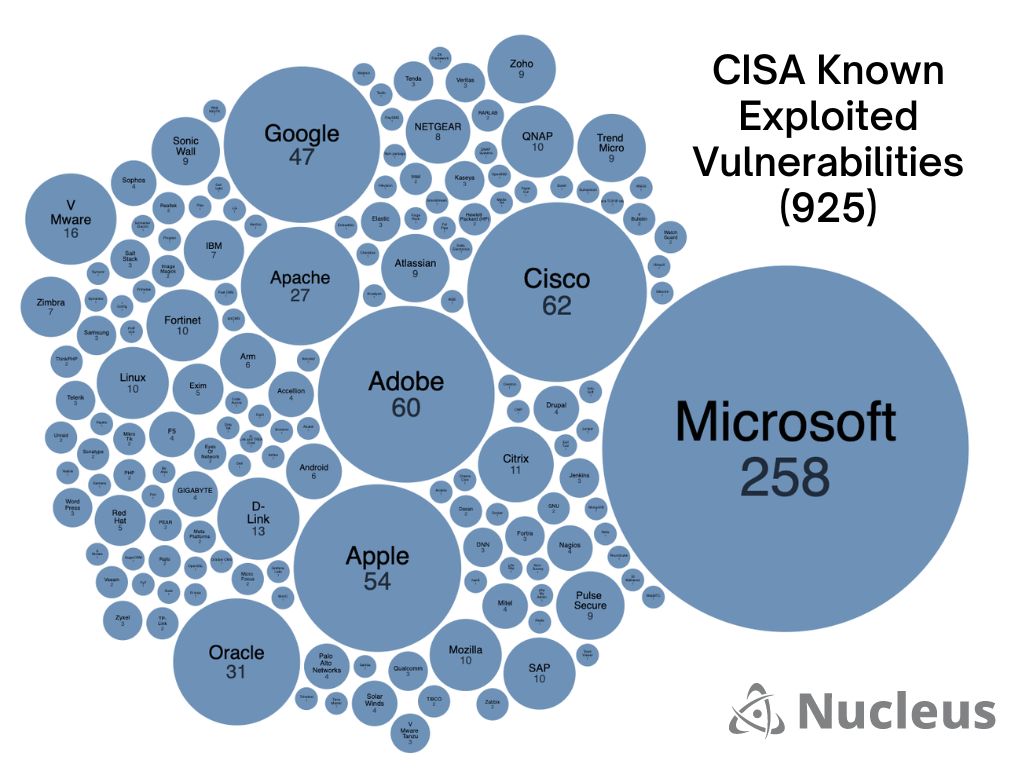
There are currently 925 known exploited vulnerabilities on Cybersecurity and Infrastructure Security Agency’s KEV catalog, making it an excellent resource for identifying potential threats. With 156 vendors included, it’s important to stay vigilant and prioritize remediation of vulnerabilities that have been identified as exploited to keep systems secure.
However, it’s also important to recognize that just because a vulnerability has been exploited doesn’t mean it’s currently being targeted. To determine what vulnerabilities should be prioritized for remediation, it’s critical to gain additional context beyond the KEV. This includes vulnerability enrichment through sources such as EPSS and Mandiant (now part of Google Cloud) and asset context, so you can make a risk-based decision on what vulnerabilities to fix first.
At Nucleus, we understand the importance of assessing vulnerability risk at scale. That’s why our platform automates the aggregation and correlation of asset and vulnerability data, making it easier for organizations to make informed decisions about their cybersecurity posture.
Top Products Featured on the CISA KEV Catalog
When it comes to known exploited vulnerabilities, Microsoft leads the pack with 258 vulnerabilities on CISA’s Known Exploited Vulnerability catalog:
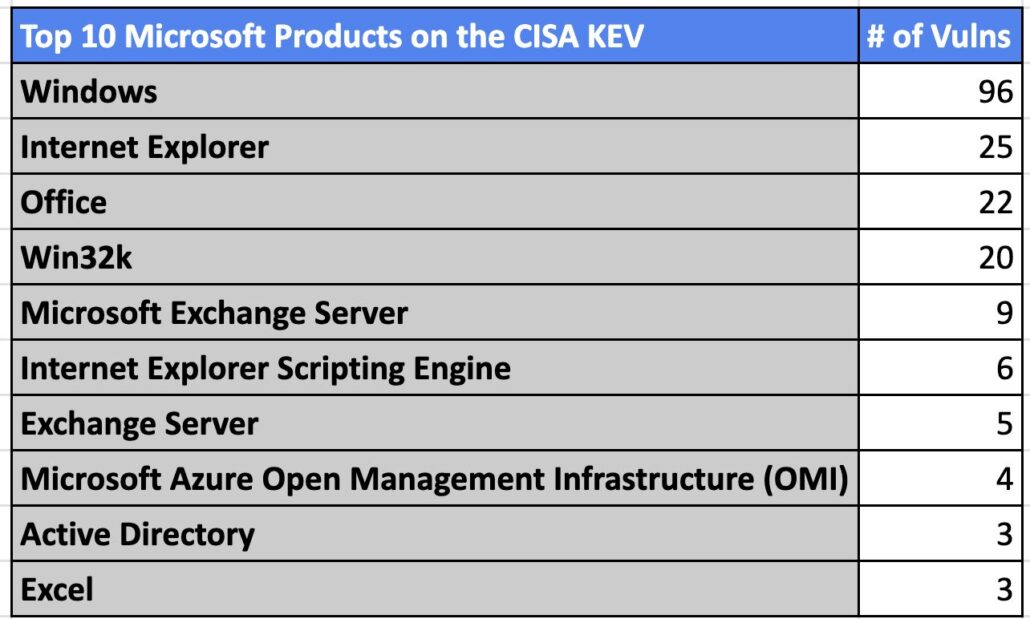
Of those products, Windows comes in the top spot, representing 37% of the Microsoft vulnerabilities on the CISA KEV and highlighting the importance of patch Tuesday.
Internet Explorer follows closely behind, demonstrating the risks of EOL software. However, it’s important to note that we shouldn’t immediately discount IE as a risk until we assess our environment and ensure it’s not in use. It’s likely still present in many enterprises due to dependencies on legacy software requirements.
Office comes in third on the list, which is no surprise given its ubiquity in the enterprise. It’s essential to ensure Office and its components are regularly updated and patched to minimize the risk of exploitation.
Over the past few years, anyone still running an Exchange server has been scrambling to patch exploited vulnerabilities such as ProxyLogon, and ProxyShell.
Overall, it’s important to prioritize mitigation/remediation of vulnerabilities on the CISA KEV list, especially for the top Microsoft products that are commonly used in the enterprise. Beyond patching, it’s also crucial to take a proactive approach to vulnerability management and regularly assess your environment with context such as confirmed exploitation for potential risks. By doing so, you can better protect your organization from potential attacks and ensure your systems remain secure.
Looking Closer at the Vendors and Products in the CISA KEV Catalog
To help further sift through the 925 known exploited vulnerabilities listed in the KEV Catalog, I created an interactive prototype that provides a simple and intuitive way to quickly click and understand which vendors and products have the most vulnerabilities on the CISA KEV:
Spoiler Alert: While Microsoft Windows leads the list with 96 confirmed exploited vulnerabilities, our prototype allows you to easily explore other top vendors like Cisco and products impacted like macos that are at risk.
The Timeline of Known Exploited Vulnerabilities
Another question we get asked frequently here at Nucleus is about the age of the CVEs listed in the CISA KEV and how they map to the National Vulnerability Database maintained by National Institute of Standards and Technology (NIST). To answer this question, we used the Nucleus Security CISA KEV enrichment dashboard to create a chart that shows the 925 CISA KEV vulnerabilities organized by the year the CVE was published:
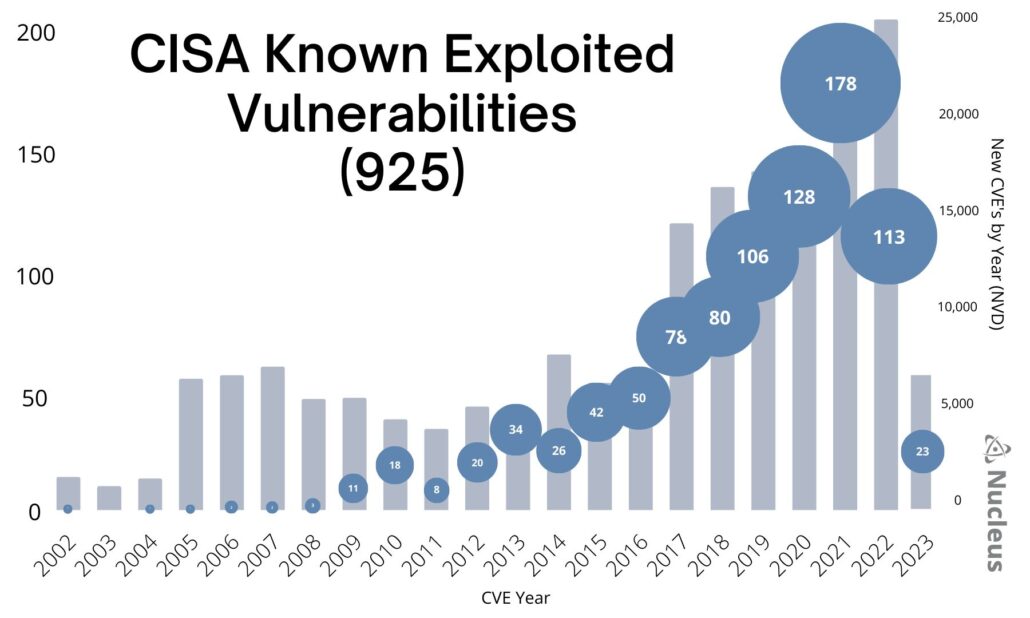 From this data visualization, we observed several key trends:
From this data visualization, we observed several key trends:
1. The majority of vulnerabilities weight to more recent years, which aligns with the accelerating growth of the NVD.
2. Overall, the trend curve appears to align closely with yearly vulnerability disclosure.
3. Data from 2022 and 2023 indicate a significant time delay between when a new CVE is identified, when exploitation occurs, and when CISA identifies and adds the vulnerability to the CISA KEV. It would be interesting to research zero days > KEV and Vulnerability time progression but I also assume someone like Mandiant (now part of Google Cloud) or Cyentia Institute might already have this research at their fingertips. (Add another research project to the list.)
4. Vulnerability disclosure and exploitation continue to rise.
By understanding the trends within the CISA KEV, we can better contextualize and prioritize our vulnerability management efforts. Want to learn more about CISA KEV and how to use it to improve your vulnerability prioritization efforts? Check out our full guide to CISA KEV enrichment below: