Guide to CISA KEV Enrichment
At Nucleus, we are continually researching ways that organizations can leverage threat intelligence for smarter vulnerability prioritization.
In November 2021, CISA issued BOD 22-01 — a binding operational directive aimed at reducing the significant risk of known exploited vulnerabilities in the cybersecurity landscape. As part of this directive, federal agencies are required to remediate vulnerabilities within a specific frame of time that is determined by CISA, based on the criticality of the vulnerability.
BINDING OPERATIONAL DIRECTIVE 22-01: REDUCING THE SIGNIFICANT RISK OF KNOWN EXPLOITED VULNERABILITIES
“The United States faces persistent and increasingly sophisticated malicious cyber campaigns that threaten the public sector, the private sector, and ultimately the American people’s security and privacy. The federal government must improve its efforts to protect against these campaigns by ensuring the security of information technology assets across the federal enterprise. Vulnerabilities that have previously been used to exploit public and private organizations are a frequent attack vector for malicious cyber actors of all types. These vulnerabilities pose significant risk to agencies and the federal enterprise. It is essential to aggressively remediate known exploited vulnerabilities to protect federal information systems and reduce cyber incidents.
This directive establishes a CISA-managed catalog of known exploited vulnerabilities that carry significant risk to the federal enterprise https://cisa.gov/known-exploited-vulnerabilities and establishes requirements for agencies to remediate any such vulnerabilities included in the catalog. CISA will determine vulnerabilities warranting inclusion in the catalog based on reliable evidence that the exploit is being actively used to exploit public or private organizations by a threat actor.” — CISA.gov
Prioritizing vulnerability remediation using threat intelligence should be a key priority for any organization looking to quickly eliminate vulnerabilities that pose the highest risks. CISA KEV is not only highly trusted and freely available to all, but the low barrier to entry makes it a great place for any organization to start considering how threat intelligence can be incorporated into their vulnerability management program.
Once an organization has implemented vulnerability scanning across their network, applications, and cloud, CISA KEV can then be used to identify what known exploitable vulnerabilities exist within the environment which will provide a focused list on where to prioritize remediation efforts.
Once you get a handle on CISA KEV, we also believe it’s incredibly important to consider incorporating vulnerability threat intelligence beyond a single source. “Only a small subset (2%-7% of published vulnerabilities are ever seen to be exploited in the wild.”, says EPSS. Considering CISA KEV only covers approximately .5% of the total number of CVE’s, it’s a great place to start focusing your efforts but we strongly recommend considering incorporating additional vulnerability intelligence sources to identify a broader set of exploitable vulnerabilities, such as GreyNoise, Recorded Future, and other sources.
Enrichment Vendors
What truly sets our CISA KEV Enrichment Dashboard apart from the baseline information provided in the CISA KEV list is the multiple enrichment columns we have added from CVSS, EPSS, and GreyNoise Threat Intelligence, which layer additional intelligence on top of each CVE to help organizations better prioritize and remediate each vulnerability.
CVSS
The Common Vulnerability Scoring System (CVSS) is an open framework for communicating the characteristics and severity of software vulnerabilities that is maintained by NIST’s National Vulnerability Database. CVSS produces a score ranging from 0 to 10 and categorizes these ratings as None, Low, Medium, High and Critical.
EPSS
The Exploit Prediction Scoring System (EPSS) is an open, data-driven effort for estimating the probability that a software vulnerability will be exploited in the wild. EPSS fills that gap because it uses current threat information from CVE and real-world exploit data. The EPSS model produces a probability score between 0 and 1 (0 and 100%). The higher the score, the greater the probability that a vulnerability will be exploited.
GreyNoise Threat Intelligence
GreyNoise provides this insight by monitoring and analyzing scanning and exploitation traffic around the world via their global passive sensor network. Threat intelligence like this provides further validation in the value of using multiple threat feeds for discovering exploitation which should be used to prioritize vulnerability remediation.
- GreyNoise Traffic – This field shows the number of unique IP addresses actively scanning for this specific CVE in the past 90-days.
- GreyNoise Tag – This field links to the GreyNoise Tag Trends page for each CVE, providing a time-series look at active exploitation traffic (note – GreyNoise does not cover all the CVEs in CISA KEV)
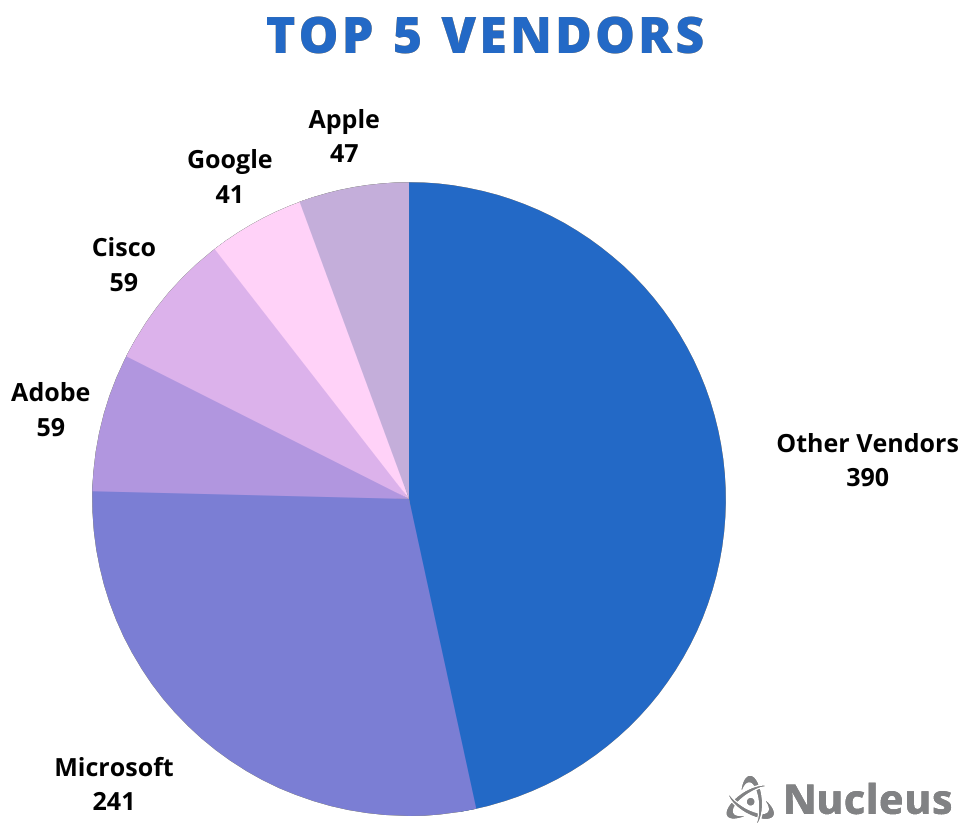
Most Featured Vendors
- The top five most featured vendors on the CISA KEV list include Microsoft (with 241 vulnerabilities), Adobe, Cisco, Apple and Google, making up more than 53% of all vendors included.
- Certain brands, like Apple, carry a perception that just buying and using them will keep you secure. As we see from the CISA KEV list, you also must keep them up to date.
How to Identify, Prioritize, and Remediate Exploitable Vulnerabilities on the CISA Kev List
CISA KEV provides a great place to start making progress at reducing an organization’s risk. By following a simple course of action, such as the four steps below, organizations can make meaningful progress toward a more mature vulnerability management program that starts by leading with intelligence.
- Scan and identify which assets in your environment have known vulnerabilities that CISA has confirmed as being exploited in the wild
- Automate remediation workflows to assign SLAs for remediation
- Integrate Remediation workflows with existing ticketing systems such as ServiceNow and Jira
- Measure CISA KEV due date SLAs to ensure federal compliance mandates
How Nucleus Can Help
It’s obvious to us that CISA and the US government understand the importance of sharing the vulnerability intelligence they have not only with federal agencies, but also making the threat intelligence available for all to incorporate and act on. They have made this evident through their CISA KEV catalog, which remains a trusted, free, and reasonable sized list of vulnerabilities that every organization should strongly consider using to prioritize vulnerability remediation.
Nucleus not only helps you identify which assets in your environment have been flagged as CISA Known Exploited Vulnerabilities, but we also help you cross reference the data that CISA provides with threat intelligence, CVSS, and more to help you better understand every vulnerability’s risk to your environment.
Want to learn more about the CISA KEV use cases within our Nucleus Security platform? Click here.