What is EPSS?
In this episode of Nucleus Shortcuts, Adam Dudley and David Farquhar discuss Vulnerability Management and the Common Vulnerability Scoring System (CVSS).

EPSS stands for Exploit Prediction Scoring System and is framework that predicts the probability of a vulnerability being exploited. EPSS is often used to help in identifying high risk vulnerabilities to prioritize for remediation.
EPSS uses a percentage for probability. So if you see 94, the score is that is trying to say that vulnerability has a 94% probability of exploitation. And it stands to reason that a vulnerability with a score like 94, is something that deserves immediate attention, where a vulnerability with a score of like say 20 deserves to take a lower priority.
In this episode of Nucleus Shortcuts, Adam Dudley and David Farquhar discuss Vulnerability Management and the Exploit Prediction Scoring System (EPSS).
Episode Raw Transcript
Adam Dudley (00:00):
So what’s up with EPSS.
Dave Farquhar (00:02):
You can think of CVSs as a generalist EPSS as a very narrow specialist.
Adam Dudley (00:09):
That’s coming up next on nucleus shortcuts. Hey everyone. It’s Adam Dudley. Welcome to nucleus shortcuts where we help you with the fundamentals, tips, and tactics for building a scalable vulnerability management program. In this video, we’ll be talking with Dave Fark, who has remediated over 800,000 vulnerabilities in his career. Curious to know how Dave has used EPSS stick around to find out. Would
Adam Dudley (00:35):
You just kick us off with a brief take on you know, what the heck EPSS is? And maybe give us a light dose, a historical context. I think it’s a fairly new
Dave Farquhar (00:43):
Thing at it’s hard. It’s a percentage. So if you see 94, the score is that is trying to say that vulnerability has a 94% probability of exploitation. I just looked up the famous log for J 90.5. So 90.5% chance of exploitation is roughly what they’re trying to say. There, there you go. And it stands to reason that a vulnerability with a score like 94, 90 0.5, something like that deserves media attention, where a vulnerability with a score of like say 20 deserves to take a lower priority than those to contrast it with CVSs. Cvss is trying to sum up everything about vulnerability in a single number where EPSS is trying to do one thing. Well, and only one thing. So you can think of CVSs as a generalist EPSS as a very narrow specialist.
Adam Dudley (01:45):
Okay.
Dave Farquhar (01:47):
And so they are using statistical modeling to look at vulnerabilities that have been exploitable and look at other vulnerabilities, ideally vulnerabilities that are not yet exploitable and see, Hey, what do these have in common? Okay. And then based on how closely they resemble vulnerabilities that have become exploitable, try to predict will this vulnera is this vulnerability likely to become exploitable. And then they go and they score all of them. Now they even score the vulnerabilities that are exploitable. So that’s a little bit of nuance there getting
Adam Dudley (02:27):
Into the meat of the topic. You know, why does EPSS matter in the context of vulnerability management programs?
Dave Farquhar (02:33):
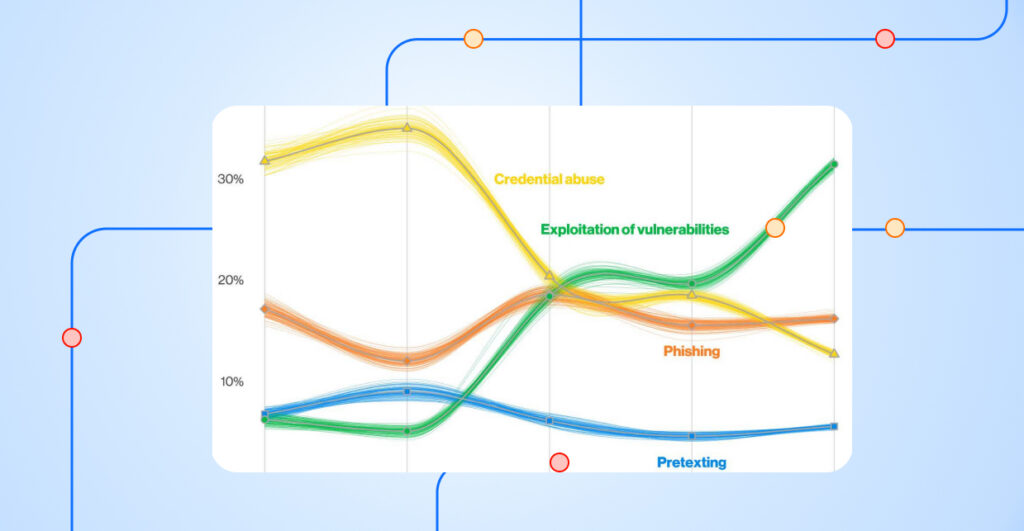
The big reason that I like EPSS better than CVSs is because it, it follows the bell curve much better than okay. Much better than CVSs does. The, the assumption with CVSs is that it’s following a bell curve or that it at least has an even distribution. And it doesn’t, that gives us two good use cases for EPSS. That first thing that you can use it for is prioritization mm-hmm <affirmative>. And there may be two reasons that you want to use this. So if man yet hasn’t scored a vulnerability yet, for some reason, mm-hmm <affirmative> you can use EPSS to fall back and prioritize that way.
Adam Dudley (03:15):
Okay.
Dave Farquhar (03:15):
Another thing that you could do would be to use Mandiant for critical and high vulnerabilities, then use EPSS to prioritize medium and low vulnerabilities.
Adam Dudley (03:30):
Okay.
Dave Farquhar (03:31):
The theory being, if a, if Mandi calls it a medium or a low that there isn’t exploit activity, or not very much exploit activity going on yet, but if the EPSS score is higher, that says that it has the potential to become a problem sometime in the future. Got it. So that would be a way to get ahead of the curve without saying, yeah, I need you to fix all the mediums at all the lows. So the other place that you could consider using this would be in your risk acceptances. Now there is an equation somewhere in my big green CI S S P book that says risk equals probability times impact,
Adam Dudley (04:13):
Right.
Dave Farquhar (04:14):
Impact. Isn’t too hard. You can just go in and Google the average cost of a ransomware incident or the average cost of a breach mm-hmm <affirmative> and call that your impact. If you wanna keep things nice and simple and have a nice dollar figure here.
Adam Dudley (04:30):
Got it.
Dave Farquhar (04:31):
Take the EPSS score because it’s a percentage and multiply that 6% of $5,000 doesn’t scare me nearly as much as 94% of $5,000. So when we have EPSS data, it will show in the vulnerability intelligence section of a finding mm-hmm <affirmative>. So I’m gonna pull up, we’ve got log for J in this demo environment. Here we
Adam Dudley (05:00):
A classic.
Dave Farquhar (05:01):
Yes.
Adam Dudley (05:04):
Becoming a classic. <Laugh>
Dave Farquhar (05:05):
Becoming a classic it’s very quickly became one of the all time grades. Yes. Yeah. <Laugh> so you will see the EPSS score in between the CVSs score and the, the Mandi rating. I could bring up another one as well. So here’s one that is a little bit less classic and you can see here, Mandy yet rated at a medium UPSs score is only 1.4%.
Adam Dudley (05:29):
Okay. And
Dave Farquhar (05:30):
Not exploited in the wild, according to man yet. So, and thingss been around for three or four years, not how doesn’t look like a great prospect here. So this is kind of where, what we like to see this kind of a score, so, right. Hey, you know, do I accept this risk? I’m more inclined to accept this one, the last one than we
Adam Dudley (05:53):
Looked at, for sure. <Laugh> yeah. The previous one warrants, some additional investigation. Right,
Dave Farquhar (06:00):
Right. And like, this is one of, this is a nice example where I can find you CVSs eight that have low EPSS scores. This wasn’t, hasn’t quite an eight, but it’s a 7.8. <Affirmative> so getting close there mm-hmm <affirmative> but EPSS score is 1.4%. So does not have a bright future as far as becoming exploitable, as far as we know, just doesn’t have those attributes. Mm-Hmm <affirmative> the, now the good news there being, when you are able to reduce the number of vulnerabilities that you’re really worried about using threat intelligence and pre-read intelligence like this, it is much more practical to look at asset criticality. In business context, you can do that across 2% of your environment, much, or 2% of your vulnerabilities, much more easily than you can and get across 80% of them. So this is how you would go about checking to see in your environment. What percentage of the matter? So note this number at first mm-hmm <affirmative>, so we’ve got 89,000, almost 9,000 vulnerabilities in our environment takes number here. And I filter and I come down here and find EPSS and I’m gonna say greater than, and I’m gonna go ahead and say six, seven. Okay. And I search, I’ve got 235. If that number seems a little bit too much, I want to prioritize and say, which ones have a score of like 90%.
Adam Dudley (07:34):
Okay. Should be a much solid, smaller than it is. Yeah.
Dave Farquhar (07:37):
Yeah. So now we’re at 42, so yeah. Okay. That’s that seems like a manageable number. Mm-Hmm <affirmative> so you can go and do that to, and then also keeping in mind, you will probably be doing this as a second pass. At least if I were doing this. Okay. I would fix my Mandiant criticals first. Sure. Then my man yet highs, then now all I have are things that Manian has scored medium and low mm-hmm. <Affirmative> take this pass at it. Now I’ve set myself up for future success and then we can figure out how we wanna prioritize from there. We can look at an automation rule. Nice. So if I do go to automation and go to finding processing, and I’ve got all kinds of things in this environment here mm-hmm <affirmative> let’s take a look at this one. So I went and I created a rule that says, Hey, if I’ve got a man yet risk rating that is medium or low.
(08:44):
If I’ve got an EPSS score, that’s greater than 0.6, six. And I could say 0.67, if that makes you more comfortable, whatever risk tolerance you’re comfortable with does does 67% seem like seem unacceptable? Does 50% seem unacceptable? Mm-Hmm <affirmative> does 90% seem unacceptable. Every organization has a little bit different degree of risk tolerance. So if you know that that’s what E E PSS is just trying to predict likelihood of exploitation. So put a number in there that makes you feel that you are comfortable with then based on that set a severity, if you would like mm-hmm <affirmative> and always put a reasoning in when you recast mm-hmm <affirmative>. And the other thing that I did here was have it set a due date, say, Hey, you know, 45 days from when the rule runs, we want to go and we want to fix vulnerabilities that meet this criteria. So give you a month and a half. So that’s just an example, but you know, feel free to adapt that to your particular situation. Before
Adam Dudley (09:53):
We wrap up this episode, in your view, is there something that’s most important for folks to take away from
Dave Farquhar (09:58):
Our conversation today? There is some visibility that we don’t have into exactly. You know, how they’re doing the modeling and all that, but keep in mind that with statistics, there’s always a margin of error. Sure. Industry standard margin of error is 5%.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.