Vulnerability Management Benchmarking: Metrics and Practices of Highly Effective Organizations
Webinar Summary
To effectively manage vulnerabilities, organizations must establish efficient vulnerability management practices. This upcoming webinar aims to delve into the core aspects that distinguish highly effective vulnerability management strategies. Through a blend of qualitative and quantitative insights, we will:
- Explore the practices of the highest performing organizations in vulnerability management. From organizational culture and leadership commitment to the adoption of advanced technologies and processes, we will dissect the key components that contribute to their success.
- Leveraging data pulled from the Nucleus database, we will present a quantitative analysis of vulnerability management effectiveness so you will be able to measure your organization’s performance against industry standards and identify areas for improvement.
- Outline what next-level maturity looks like, for organizations that have already achieved a degree of maturity in their vulnerability management efforts.
- Discuss advanced metrics for measuring success, the integration of vulnerability management into broader security and IT operations, and how to sustain and improve upon current levels of performance.
Whether you are just beginning to build your vulnerability management program or looking to elevate an already mature operation, this webinar will provide valuable perspectives on what good looks like in vulnerability management.
Key Takeaways
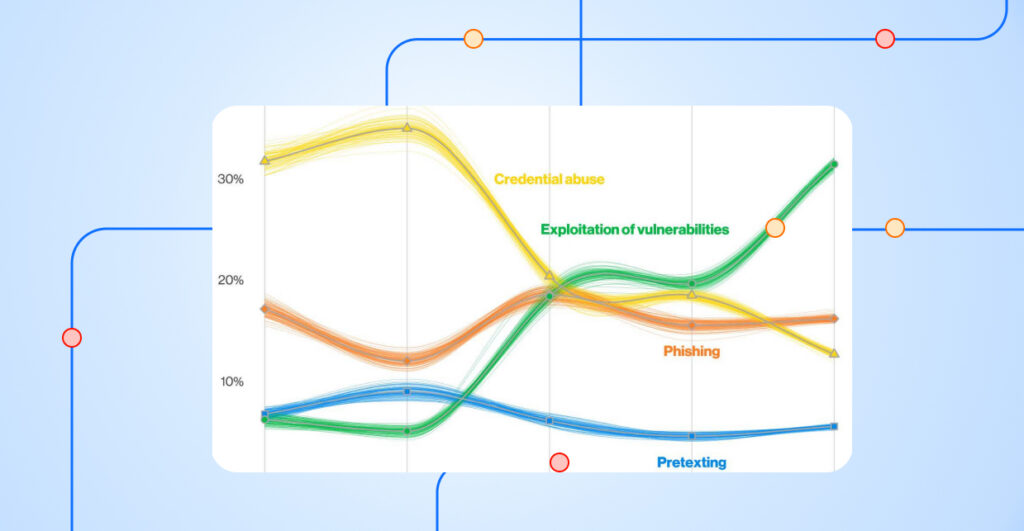
Mean Time to Remediate (MTTR)
One of the core metrics discussed was the Mean Time to Remediate (MTTR), which measures the average days an organization takes to address vulnerabilities. Interestingly, top-tier organizations (the best-performing 10%) have an MTTR of approximately a month for all vulnerabilities, with critical ones being resolved in about five days. This starkly contrasts with lower-tier organizations, where even less critical vulnerabilities linger much longer, likely due to prioritization challenges and resource constraints.
Vulnerability Age and Management
The average age of vulnerabilities in the bottom 50% of organizations is significantly higher than in the top echelon. This discrepancy underpins the struggle of many organizations in managing vulnerability effectively, compounded by issues like false positives and the complexity of cloud and ephemeral assets.
Service Level Agreements (SLAs)
The discussion underscored the vital role of SLAs in gauging the health of vulnerability management processes. SLAs differ widely across organizations, with higher performance being notched by entities deploying precision-based SLAs, tailored to their specific operations, unlike the generic, policy-based SLAs which are common in lower-performing settings.
Impact of Patching and Compliance
The webinar highlighted how vendor patching capabilities and compliance requirements profoundly impact vulnerability management. Organizations adhering to strict compliance frameworks often exhibit faster remediation times, driven by the urgency compliance enforces.
The Role of Automation
Emphasizing the importance of technology, Scott and Ryan discussed how Nucleus’s data aggregation system assists in streamlining vulnerability management by enhancing visibility, triage, prioritization, and reporting. This system, which has compiled data on over 13 billion vulnerabilities, aims to provide a robust foundation for decision-making.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.