It’s a month of NEWs – new Snyk and Prisma Cloud experiences, new Trends Page metrics, new Nucleus Risk Score automation criteria, and a new release.
Welcome to the Nucleus Product Update 3.5. As our headline reads this month, it’s a month of new. Multiple new features and product capabilities are meant to improve your Nucleus platform experience and options significantly. There’s also a new release in store, and we want to ensure you are prepared and ready to take full advantage of it.

Key highlights from this update include:
- Expanded Trends Page metrics with additional vulnerability age data
- Better management of container image vulnerabilities for Prisma Cloud users
- Snyk connector refresh with big user experience and asset management upgrades
- New automation option using the Nucleus Risk Score
We’re also providing a final reminder for the upcoming June 28 Asset Group Access Control (AGAC) general availability release, with much-anticipated product features that directly address needs expressed by our users.
Get the details for all updates below.
Have questions or want to know more about anything you see here? Our team is happy to help. Just reach out to our crew at support@nucleussec.com for further assistance. Happy reading!
Final Reminder: AGAC v1 GA Live June 28
On Wednesday, June 28, Asset Group Access Control (AGAC) will be automatically enabled for all customers in the Nucleus platform. These changes do not require action, as they apply automatically, but they may change your experience managing asset groups in your project(s).
AGAC is meant to complement our existing role-based access control (RBAC) in the Nucleus platform and gives admins more control over who sees and modifies data (and where) for enterprises with lots of vulnerability data (and lots of people managing it). AGAC is a powerful tool to ensure only the people who need to see specific vulnerability data within a project can access it, while others don’t.
As part of this release, we ensure that asset groups stay updated in a more dynamic fashion. Combined, all these product changes fulfill a critical need for our customers to safeguard access to their sensitive data and streamline their mitigation teams’ experience.
In preparation for this release, we strongly encourage you to do the following:
- Review/adjust/update your user roles within Nucleus. If you plan to restrict users by access group once this functionality releases on June 28, assign those users the new “Asset Group Restricted User” role to ensure strict access/controls.
- Review your assets and identify any you’d like to keep permanently associated with certain asset groups. Once this change is live, using the Asset Management interface, you can switch assets to static (rather than automatic) to avoid any automation rule removing them from the asset group(s) they are in currently.
- Review your asset group automation rules to ensure that any rules which place assets into groups have up-to-date, still relevant conditions.
You can learn more about this update in the Asset Group Access Control support article. For further questions or help, please email support@nucleussec.com or contact your Nucleus Account Manager.
Expanded Trends Page metrics with additional vulnerability age data
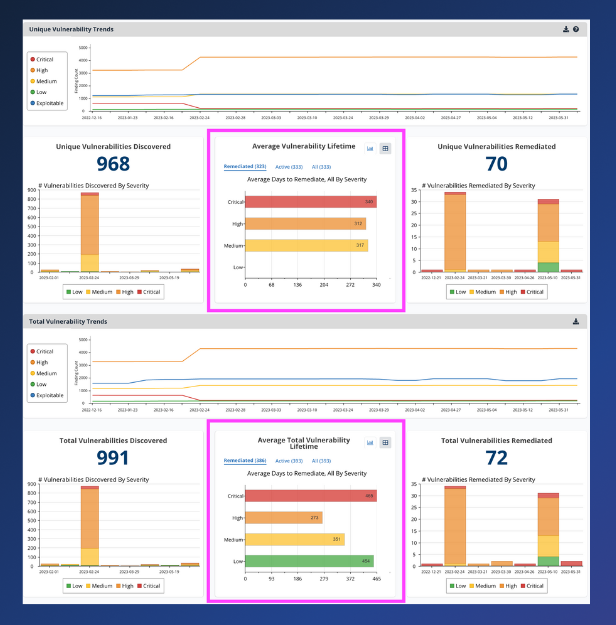
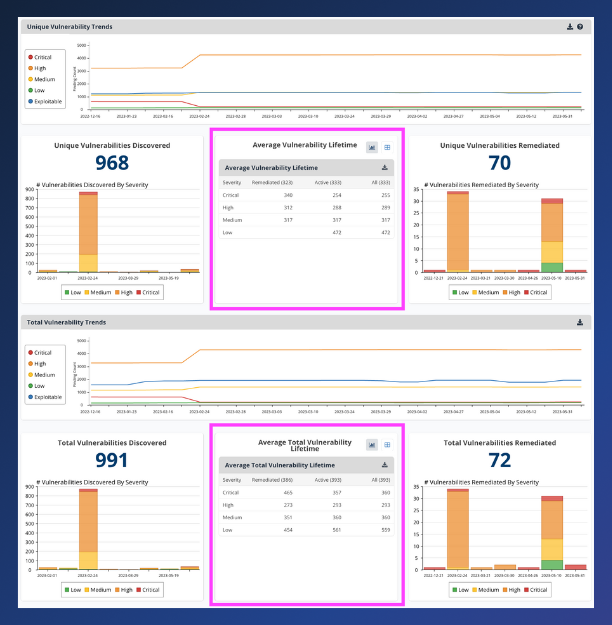
On May 24, we released a new Trends Page update designed to provide expanded information on the age of vulnerabilities in your projects to help you monitor your vulnerability management performance and progress more effectively over time. Previously, the Trends Page showed only the average lifetime of remediated findings by severity. With this update, you now have the option to view the average age of active or all findings while still being able to view the average lifetime of remediated findings.
This change represents a massive time saver for organizations that use metrics like vulnerability age (also known as dwell time) in conjunction with time-to-remediation to track the success of their vulnerability management programs. You can now answer two related but distinct questions more easily: 1) How long is it taking me to patch? and 2) How long have vulnerabilities been active in my environment? We’ve also added a table view so you can quickly expose the raw numbers populating the chart.
Read this Release Spotlight or review our product documentation to learn about these Trends Page updates.
Better management of container image vulnerabilities for Prisma Cloud users
On May 17, we released persistent statuses on container images, enabling our customers to set statuses on container image vulnerabilities and apply that status to all vulnerability instances on images in the same repository. Similarly, when ingesting scans with container image vulnerabilities, Nucleus will set the status of newly ingested container image vulnerabilities to match the status set manually by users on any other instances of the same vulnerabilities on other container images in the same repository. This new feature enables easier vulnerability management on ephemeral container images. To enable this feature for your organization, please get in touch with Nucleus Support at support@nucleussec.com.
Snyk connector refresh with big user experience and asset management upgrades

Released May 24, the Snyk connector rebuild enables scan data ingests by target instead of project, representing vulnerabilities on a repository asset instead of separate project assets in Nucleus projects. Nucleus customers can now import all projects from a target in a single job and have them automatically combined into a single application asset representing the target code repo instead of individual assets for each project. This upgrade will significantly reduce license consumption for the heaviest Snyk users and provide a better Nucleus platform experience. It does not change or impact container image asset ingests into Nucleus.
This update is currently available as part of an early-access program. There are steps required to prepare a project for this new functionality and properly migrate your existing data, so please get in touch with Nucleus Support at support@nucleussec.com if you’d like to get this started. Though optional at this time, this migration to the “new” Snyk will eventually be default behavior for all Nucleus customers.
New Finding Processing automation option using the Nucleus Risk Score
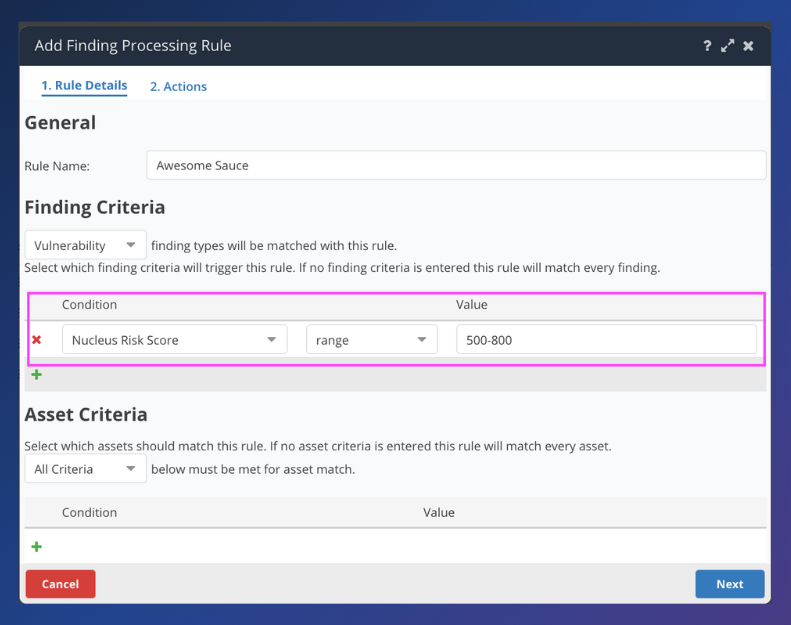
As of May 24, the Nucleus Risk Score is now available as criteria in Finding Processing automation, including a range operator. This new option enables Nucleus customers to create automated rules based on the Nucleus Risk Score. For example, creating an automation rule for any Nucleus Risk Score above 900 that sets or assigns a specific due date.
Your invite to our upcoming webinar

Join Orange Cyberdefense (OCD) Head of Security Research, Charl van der Walt, Catherine Boddy, OCD Head of Vulnerability Operations, and Stephen Carter, Nucleus CEO and co-founder, for an in-depth discussion about the research OCD has done around different vulnerability prioritization methods including CVSS, EPSS, and CISA KEV, often used to prioritize their vulnerability management efforts. Register here.
Click here to expand our full Release Notes
You can access the Nucleus change log to view the complete, unedited version of release updates posted each week. Select the subscribe to the RSS feed option on this page if you would like to receive weekly change log updates. This new Nucleus Product Update is intended to fully summarize and outline those weekly changes for you, with more details, each month. The product updates include all the following features and improvements:
New Features
- Updated the Average Vulnerability Lifetime and Average Total Vulnerability Lifetime charts on the trends page to include counts for remediated findings, active findings, and findings with both active/mitigated. Consume the data in chart form, or table form, and export the data via CSV.
- The Snyk connector now has the ability to ingest scan data by target instead of project, representing vulnerabilities on a repository asset instead of separate project assets in your Nucleus project. This is available as part of our early-access program. Please reach out to your customer success manager to have this enabled.
Product Improvements (Performance, Experience, & Functionality)
- Added finding package data as available criteria within Finding Processing, ticketing and issue tracking, and notification automation. Ticketing APIs have been updated as well.
- Updated ticket creation via the Instances View with smoother timeout, failure, in-progress, success scenarios.
- Improved the speed of Finding Processing rules that are limited by asset groups when run manually from the UI.
- Improved manually updating severities for container image findings, so that the severity carries through on the same finding/image in the same container repo in the future. Contact support or account management to activate.
- Updated the Asset Group Restricted User role (available to Asset Group Access Control beta users) to include permissions around updating finding statuses. Users restricted by asset group can edit findings that they have access to, and those changes will be isolated to the instances by which that user is restricted.
- Improved speeds around team actions and filtering, especially in Nucleus projects with a large number of teams.
- Sped up ticket creation, especially in environments with a lot of tickets.
- Added the Nucleus Risk Score as a condition in Finding Processing automation.
- Improved post-scan processing of finding processing rules so that they run more quickly for very large scans.
- Updated the name of the informational finding used when a scan has no vulnerabilities across all source tools to consistently be called “No Vulnerabilities Found”. This name used to be called “Asset Has No Vulns” or “Scan Has No Vulns”. Note that all findings in projects have been updated to reflect the new naming.
Reporting Improvements
- Implemented a new approach to file generation for the S3 connector so that very large projects continue to upload files quickly.
Integration Improvements
Axonius:
- Increased timeout of Axonius requests.
Checkmarx:
- Updated Checkmarx asset matching logic to prevent assets from incorrectly being over-matched.
Prisma Cloud:
- Added retries in certain 503 scenarios upon Prisma Cloud ingest.
Security Hub:
- Improved interaction with scan files in the Security Hub connector to be able to handle very large scans.
Tenable:
- Increased efficiency in the Tenable.io connector by increasing chunk size of finding asset counts.
- Improved the resiliency of the Tenable.io connector to cater for scenarios where the Tenable.io API is unreliable and is randomly failing to return complete data, or in some cases, any data at all.
Bug Fixes
-
- Fixed an issue where nested asset groups were not updating correctly when using automatic asset group removal.
- Fixed an issue where the Vulnerability Summary Detailed XLS failed to load in cases with large numbers of assets and tags.
- Fixed an issue where the Crowdstrike connector was not setting as mitigated for assets from subsequent scans with no vulnerabilities.
- Fixed an issue when formatting to asset CSVs attached to tickets.
- Fixed an issue when the default Nucleus footer was still showing in emails triggered by Nucleus, even if an org had a custom footer specified.
- Fixed an issue where certain characters were stripped from connector credentials, which caused authentication to fail.
- Fixed an issue in Finding Processing automation where manually running a disabled rule was incorrectly applying to CVE findings.
- Fixed an issue in the NexusIQ connector where we were attempting to download scans that no longer existed in NexusIQ.
- Fixed an issue where the count in the active vulnerabilities page did not match the vulnerability details .xlsx export when certain severities were applied.
- Fixed an issue when trying to fetch a deleted project from Snyk for better error handling.
- Fixed an issue when removing inactive assets through the UI, where the inactive date was shifted to the removal date.
- Fixed an issue where applying a filter on the Active Vulns page, and editing the findings was affecting all instances of the vulnerability, even those that have been filtered out.
- Fixed an issue in Finding Processing automation where changes to severities in an earlier rule was not recognised in a later rule.
- Fixed an issue in ticket automation for ServiceNow, where the caller field could not be changed.
- Fixed an issue where the credentialed column was not populating as expected in the Vulnerability Details xlsx report.
- Fixed an issue in the Qualys connector where the scan was downloaded repeatedly.