Release Spotlight: Asset Group Access Control – General Availability
We all remember the experience of doing laundry in a college dorm and how stressful that can be. For starters, why so many quarters? And if your clothes are in the dryer for more than a minute after the cycle ends, you already know those clothes are going to the floor by the hands of whoever is waiting for that dryer. And who can forget the worst thing – your roommate’s nasty socks ending up mixed in with your clothes, making you want to call the police (true story, ask me about it sometime).
As vulnerability management experts, we have enough of our own dirty “laundry” in the form of vulnerabilities. We do not want or need anyone else’s dirty laundry added, as we have a hard enough time trying to get through our own loads. Similarly, we don’t want anyone else getting a whiff of our own dirty items.
You can think of our latest release, Asset Group Access Control, as your preventative aid for ensuring that everyone’s items stay in their own basket – no laundry police required.
What will change and why it matters
On June 28, Asset Group Access Control (AGAC) will be generally available to all Nucleus users. This release will bolster your Vulnerability Management programs with notable improvements.
First and foremost, AGAC allows you to restrict a user’s access to specified asset groups and the findings associated with those asset groups in a Nucleus project. Most importantly, this gives large and complex organizations an extra layer of security by minimizing access to one team’s vulnerabilities rather than leaving access (and visibility) wide open to anyone across the org. Furthermore, it helps improve VM outcomes by reducing noise and clutter: Teams can stay focused only on the findings they can address and influence instead of burdening them with unrelated, out-of-context work.
As part of this change, we also needed to introduce dynamic asset grouping, which changes how assets are placed and maintained in asset groups. Previously, when an asset was put into an asset group by an automation rule, that asset would remain in the asset group forever unless manually removed, even if the underlying conditions which placed the asset had changed.
Now, by default, if anything about an asset no longer applies to the conditions of the rule which assigned it to a group, that asset will be automatically removed from that asset group.
With AGAC, you can restrict users to only the groups they should have access to, while dynamic asset grouping ensures those asset groups remain updated without requiring much manual intervention.
How it works
There are two vantage points when it comes to Asset Group Access Control:
- Admin – The Nucleus Admin can restrict user access to specified asset groups within a project through the User Page at the global dashboard level. We strongly recommend adjusting user roles to “Asset Group Restricted User” for any users you restrict. The Asset Group Restricted User role applies specific permissions which ensure the most secure experience when restricting users by asset group.
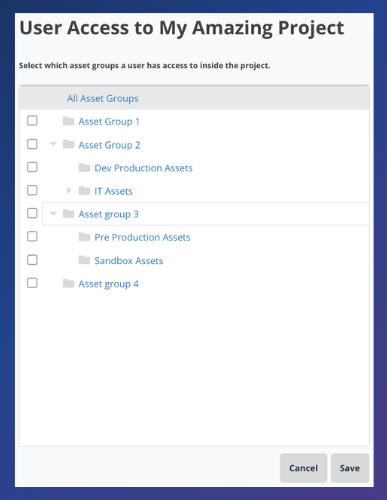
- User restricted by asset group – These users will only see findings and assets in groups under the restrictions assigned by the Admin.
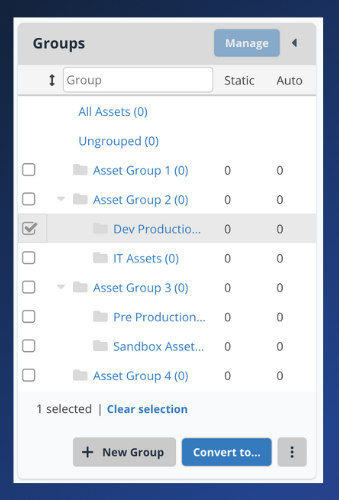
When it comes to dynamic asset grouping, you will notice various changes in the Asset Management page, along with new vocabulary to clarify the distinction between assets manually placed in groups and assets placed in groups by automation. When released, any organization can use these features regardless of whether that org is using Asset Group Access Control’s access restriction features described above.
- Static – Indicates assets placed into a group manually or by tags via a connector ingest. These assets will remain in place until otherwise indicated.
- Automatic – Indicates assets placed into a group via automation. Remember: If the conditions in the rule that placed the asset within the group are no longer relevant, the asset gets removed. If this behavior does not fit your use case, change from automatic to static to ensure the asset remains in place.
What’s Next for Asset Group Access Control
We have a lot in store to continue to build upon Asset Group Access Control. We want to continue to make AGAC an effortless experience that scales with even the largest organizations. Next up are additional AGAC features allowing Admins to restrict by asset group at the SSO Team level. These new permissions will enable Admins to assign a user to a team with a defined SSO object while also restricting access by asset group. They ensure users logging in are already automatically assigned to the team and asset groups to which they should have access.
AGAC Practical Application Examples
There are various practical applications in which AGAC can help to make Vulnerability Management programs much more efficient. One frequently noticed pattern is dividing asset groups by a person’s functional ownership within an organization. This pattern means that a particular person is responsible for a specific number of assets and ensuring forward progress on the vulnerability findings on those assets. AGAC can ensure that this person only sees the assets they need to worry about.
Of course, we’ve seen examples of more scaled solutions as well. For instance, an entire IT team claims ownership of all device-type assets, whereas the Dev team claims ownership of all application-type assets. With AGAC in place, all you have to do is divide the asset types into separate groups, and the division of assets between the IT and Dev teams is infinitely more apparent, without either team bearing the weight of the other team’s assets.
Ready to learn more about this new feature in Nucleus?
Check out our Asset Group Access Control article in the Nucleus Support Center or request a demo.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.































