Nucleus Release 2021-06-30
Another new release of Nucleus with several enhancements and a new connector! Take a look at some of the highlights.

Overview
At Nucleus, we understand that vulnerability management is a continuously evolving landscape. What was normal two years ago is in many ways different to a year ago, which is in turn different to how we do vulnerability management today – and it’s going to keep changing.
Beyond the breadth of technologies that we need to look after and the ever-changing vulnerability data sources we ingest, it impacts the very fabric of our vulnerability management programs. What we do with data once we have it and ultimately how we prevent bad actors from harming our organizations and in turn our customers are increasingly complex.
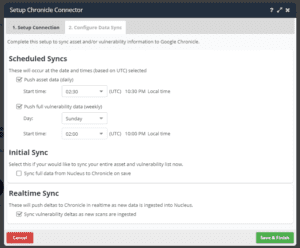
Google Chronicle Connector
That’s the reason we’re extremely excited to have partnered with Google Chronicle on our first purpose-built SIEM connector – opening a world of new use cases for correlating vulnerability data alongside security logs and alerts.
Nucleus is obsessed with precision and terms like “scalpel-like accuracy” for a reason. In a scaling VM program, you need accuracy and precision in your data, decisions, and workflows. With this connector, Nucleus customers can now achieve that precision in their incident response workflows by synchronizing Nucleus-enriched vulnerability data and asset data with the associated risk attributes to their Google Chronicle instance. Vulnerability data sent to Chronicle is asset aware too, giving you all of your asset’s organizational context such as asset groups and risk attributes right alongside the vulnerability data.
This integration enables SOC and incident response teams to (among many other situations!) do their investigations of an incident without ever needing to leave their SIEM! They can see the asset’s business context, all vulnerabilities, risk, and threat intelligence correlated to an asset for use in their investigations from a single console. This data is now all at your fingertips alongside your network traffic, SIEM events, and log data. By correlating data from all these different sources and putting them in the hands of your analysts, the incident response process and decision-making process just got better and more scalable.
Greater Insights on the Resolved Vulnerabilities Page
A major component of a comprehensive and resilient vulnerability management program is to be able to drill down into meaningful insights and drive the outcomes that matter to you and your organization. Uniquely within the vulnerability management space, Nucleus allows you to see all your mitigated vulnerabilities, and access their history in the vulnerability record itself. This is great for auditing purposes, as well as celebrating the wins with the teams that do remediation work.
For this release, we’ve invested a lot of time in further enriching the insights that you can take from the Resolved Vulnerabilities page so that you understand how and when vulnerabilities were remediated with scalpel-like accuracy (nice callback right?).
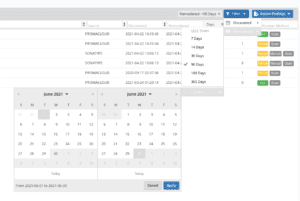
Better Date Filters
Previously the Resolved page discovered and remediated filters were limited to 3-month increments. Now you can select any date range to get the view you need when you need it.
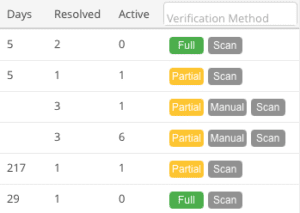
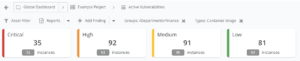
New Counts tracking number of resolved vs number still active
We’ve also updated the Resolved vulnerabilities grid to include the number of instances that were mitigated and the number that are still active. This gives you a further level of reporting which, for example, could be used to inform your weekly, fortnightly or monthly vulnerability management reports.
Better Verification Method Search
You’ll also notice that the verification method column has been updated to allow you to easily see how the vulnerability was resolved, whether it was fully resolved or only partially resolved, and report against that. This also helps you to easily search for the verification attribute of the vulnerability and report on all Scan mitigated vulnerabilities, or vulnerabilities that were only partially mitigated via a scan.
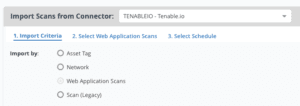
Tenable.io Connector Updates
The Tenable.io connector has had some under the hood upgrades to make it future ready. This release includes a migration away from the legacy v1 API to the Tenable WAS v2 API and a new option in the Import via Connector page to import just Web Application scans:
You can now also optionally ingest asset additional metadata in to Nucleus, and push asset (and metadata) from other sources back to Tenable.io for a more complete picture of asset information in Tenable itself. This will allow you to use the asset data coming in from 3rd parties and sync those unscanned assets back into Tenable.io so that you can automatically get the unscanned asset list back into your scanning system. This should help with scan coverage issues in enterprises where it can be difficult to reconcile your scanned assets with what you own.
To enable this, head over to the connector setup page, edit your Tenable.io connector and select the sync asset metadata options:
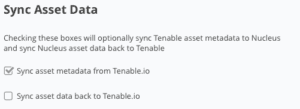
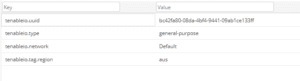
And now for something completely different… to how our existing connectors work. If you have your Tenable.io instance setup to interact with Azure, GCP, AWS, McAfee EPO, ServiceNow or BigFix, we’ll also pull in all of the associated metadata and store it as though it came from the respective source. This means that your existing asset processing rules that leverage data additional metadata from other sources (for example, aws.account-id) will automatically apply to instances scanned from Tenable.io!
Better, Faster Global Asset Group Filtering
Applying your asset context to filter all vulnerability pages in Nucleus is now even easier! Since the very early days of Nucleus, the Asset Filter button has enabled you to narrow down the vulnerabilities to show only vulnerabilities of interest by applying asset group and asset type filters and keeping them persistent from page to page.
With this release we’ve updated this button to show a popup, so that you can create more complex queries around your filters, making filter selection better and faster (hint, you can search for groups instead of scrolling through a list).
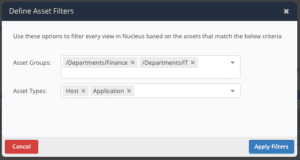
Once you’ve applied your filter, it’s displayed at the top of each page so you always know the context that you’re looking at and can alter if you need any last-minute changes:
More Application & Device Metadata
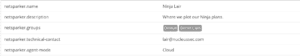
With every release, Nucleus improves your ability to automate your vulnerability management program at scale. On top of the additional metadata now being ingested from Tenable.io, this release includes updates to both the AttackForge and Netsparker connectors. This new support for metadata will allow you to use these fields in the Nucleus Automation Framework and start scaling your VM processes. Below is a complete list of keys that will be ingested from these tools for use with the Nucleus Automation Engine:
AttackForge

Netsparker
Tenable.io
API Enhancements
We are always trying to make the API more usable, and with every release, we’re making enhancements to the Nucleus API so that you can get more done faster.
-
Ability to run an asset processing rule via the API: This has been a hot request, and we are happy to announce that users can now automatically set an asset processing rule to run via the API so that when you automatically create an asset processing rule, you can trigger the rule to process as part of the rule creation.
-
The GET /asset endpoint now returns all fields: There were certain fields missing from the GET asset endpoint response so that the API docs didn’t match the result. This has been fixed in the latest release.
Complete list of changes and bug fixes…
- NEW Connector for Google Chronicle
- NEW Org Admin Users in organizations can configure inactive or never logged in user accounts to auto-disable after a set number of days of inactivity
- NEW Searchable tags on the “Resolved Vulnerabilities” page for better reporting of resolved vulnerabilities
- NEW “Resolved Vulnerabilities” page now has columns for counts of both resolved and still active vulnerabilities for better reporting and tracking purposes
- NEW The “Resolved Vulnerabilities” page can now filter vulnerabilities by discovered and remediated using custom date selectors
- UPDATE The Tenable.io connector now ingests additional metadata
- UPDATE The Tenable.io connector now can now sync asset data back to Tenable.io
- UPDATE The AttackForge connector now ingests additional metadata
- UPDATE The Netsparker connector now ingests additional metadata
- UPDATE Asset filtering now indicates what is being filtered on each page
- UPDATE Asset merge and archive actions speed updates
- UPDATE Enhancements to the PagerDuty connector and webhook
- UPDATE Nucleus can now import the RPM type vulnerabilities from Sonatype
- UPDATE Various performance improvements to increase the speed of the application
- UPDATE PrismaCloud connector update to parse certain package names better
- UPDATES Improvements related to viewing certain pages in Safari
- BUGFIX Fixed an issue where, in certain cases, if you filtered by asset group and then made a status change to a top-level unique vulnerability, the status change affected all vulnerability instances of that unique vulnerability, not only instances within the asset group you filtered
- BUGFIX Fixed an issue with timezones not being applied correctly for certain custom reports.
- BUGFIX In certain limited situations marking scans as auto-imported was not shown with the connector auto-import indicator on the Connector Setup page.
- BUGFIX Fortify references now display fully
- BUGFIX Other various enhancements and minor bug fixes
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.
































