More customization starts now with Asset Group Access Control V1 and a mega-punch of additional new features.
Welcome to the Nucleus Product Update 3.3. It’s the month of egg hunts and Earth Day! Did you know that the name for April stems from a verb meaning “to open”? In that spirit, we’re so glad you opened this and hope you’ll keep reading.
This month we’re giving you more control and access to configuration settings and vulnerability information in and outside the Nucleus platform.

These product additions include:
- An Asset Group Access Control (AGAC) limited availability launch (V1)
- More vulnerability data in ticket csv files to simplify and accelerate remediation steps
- New query for “mitigated via scan” status in key API endpoints
- New base container image view for enhanced reporting and visibility
- A Veracode connector update for more flexible data imports
We’re also including an invite to our upcoming quarterly product update webinar. Check out all the details below.
Have questions or want to know more about anything you see here? Our team is happy to help. Just reach out to our crew at support@nucleussec.com for further assistance. Happy reading!
Asset Group Access Control (AGAC) V1 is now live and available
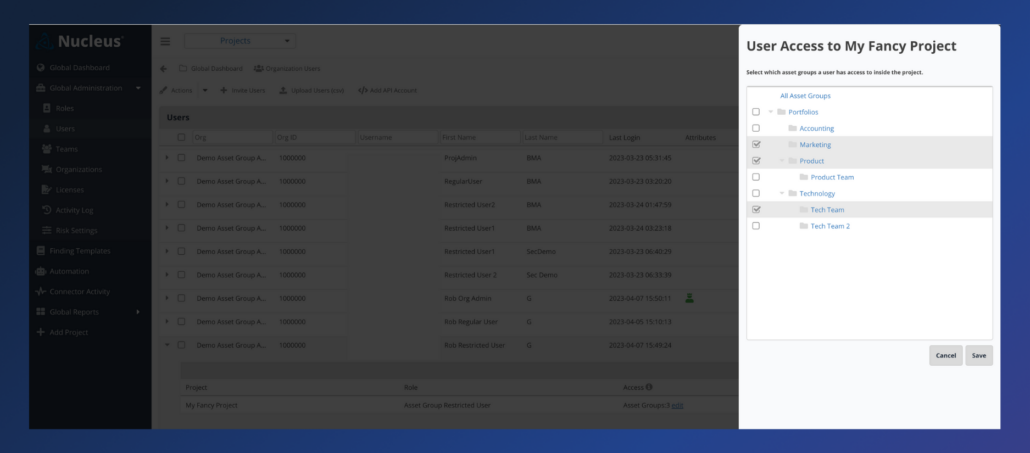
Released in March 2023, Asset Group Access Control (AGAC) V1 complements our existing role-based access control (RBAC) in the Nucleus platform. AGAC allows administrators to assign specific asset groups to users. In other words, Nucleus customers can now restrict user access to only specific asset and vulnerability data within projects where needed. For enterprises with lots of vulnerability data and people managing it especially, AGAC is a powerful tool to ensure only the people who need to see specific vulnerability data within a project have access to it, while others don’t.
We’ve also introduced a new role type, asset group restricted user, and an update to how we handle asset grouping, allowing us to keep asset groups up-to-date dynamically based on the conditions of automation rules that populate those asset groups. When combined, these updates fulfill a critical need for our customers to safeguard access to their sensitive data and streamline their mitigation teams’ experience, allowing them to focus on what matters most: remediating important vulnerabilities.
All current Nucleus customers are eligible to use these new features on request. For more information or opt-in, contact your Nucleus account manager or Nucleus Support at support@nucleussec.com. You can also find more information in this help article.
Additional vulnerability data in ticket csv files to simplify and accelerate remediation steps
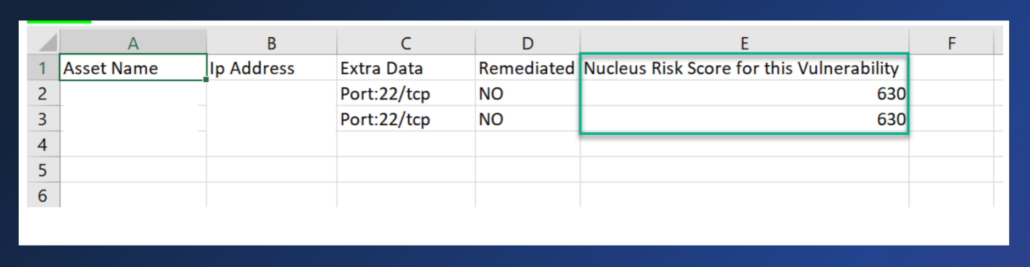
Released March 2023, the additional vulnerability data in ticket csv files simplifies and accelerates remediation steps for Nucleus customers. These much-awaited additions ensure customers get a better information pipeline to remediation teams in shorter times and fewer steps. Instead of having to leave their typical workflows in tools like Jira, remediation teams now have access to essential vulnerability data as part of the Jira ticket attached csv file. This information includes things like assets affected in the ticket, all the asset fields for all asset types, etc.
Now, remediation teams can resolve vulnerabilities they see in the Nucleus platform without navigating between multiple tools. The now-included csv information enables Nucleus customers to determine vulnerability locations without returning to the Nucleus platform, immediately improving and accelerating the customer remediation experience. We’ll continue to add to these features and make things more configurable in the coming months.
New “mitigated via scan” query in key API endpoints
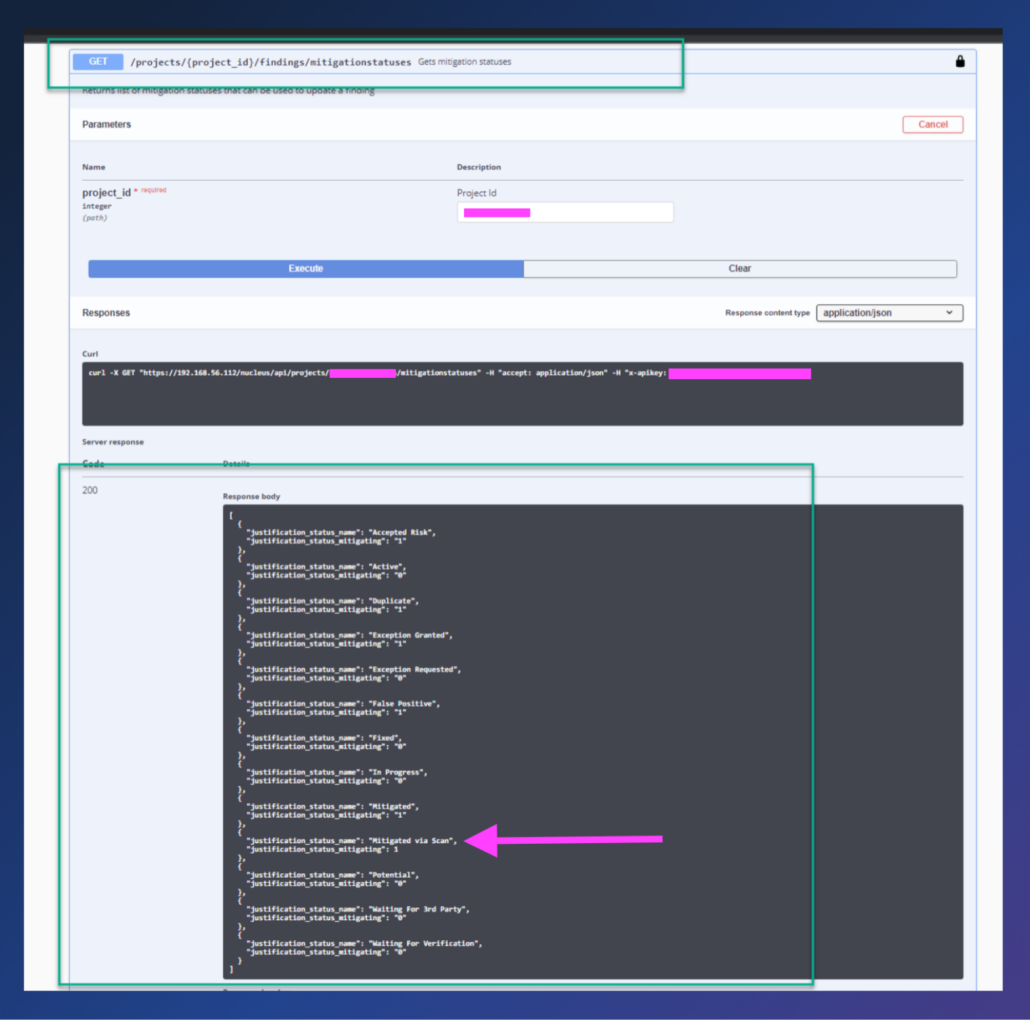
Released March 2023, we updated key API endpoints to return mitigated via scan results, enabling querying for findings that have a mitigated via scan status. The mitigated via scan status, which indicates that a finding was mitigated via a scan ingest, has always been present in the Nucleus platform, but now it’s easier than ever to include this status in any instrumentation relying on the Nucleus API. Try it out in the findings search API, where you can now include the mitigated via scan status (and optionally a mitigated date in searches) and see the status “Mitigated Via Scan” returned from the finding mitigation statuses API.
Enhanced reporting and visibility with new base container image view for Prisma Cloud
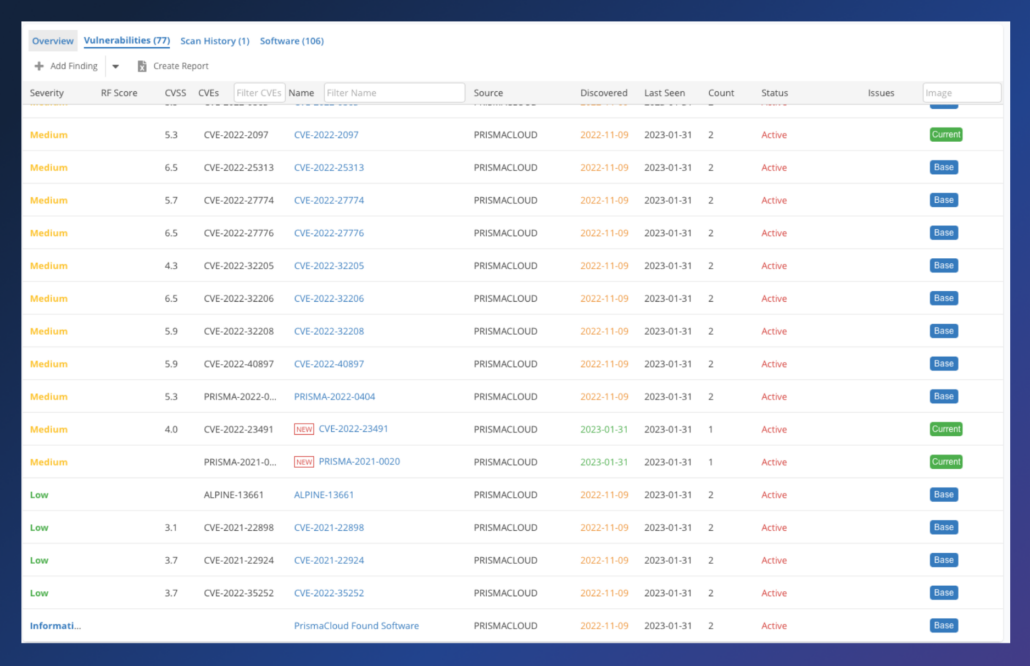
Released this month (April 2023), the new base container image view for Prisma Cloud enables Nucleus customers to detect and view relationships between container images. This information can be used to determine whether a vulnerability was introduced on the base image or another image. As remediation teams work to determine where vulnerabilities live, this new view can be highly beneficial when working with containers.
More flexible data imports for Veracode now with import all or by tag options
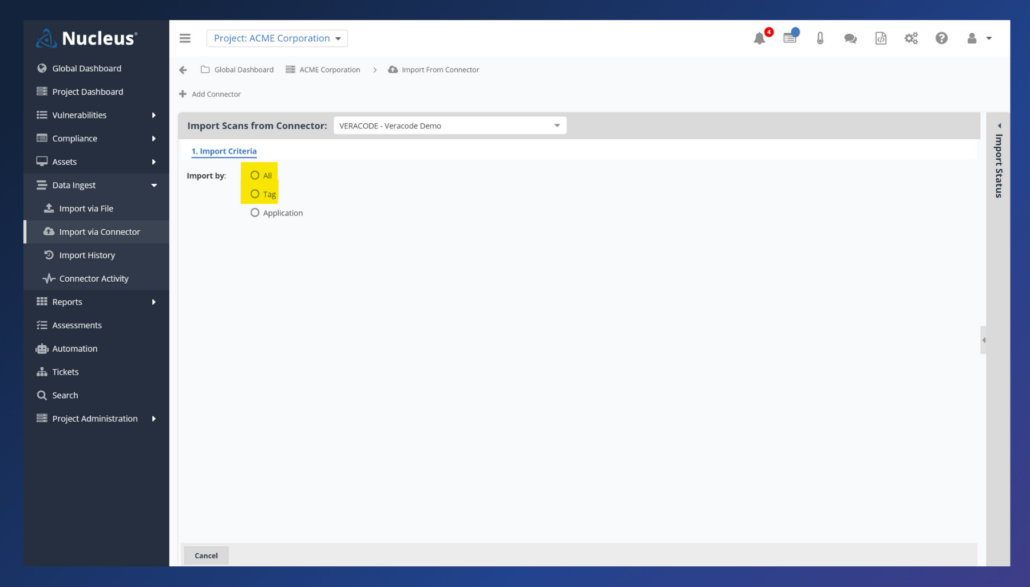
Continuing our ongoing quest to make it easier to import your data quickly, reliably, and confidently, we’ve enabled a new enhancement to our Veracode connector. Previously, users would specify the applications they wanted to import scans from. However, many Veracode customers extensively use tags to organize their many application scan results, so we added the new ability to specify which tags we should look for when importing. This approach cuts down on manual labor by making it easier to categorize information abstractly from applications and have Nucleus respect that categorization with just a few clicks. For example, customers may want to specify which product or business unit each application is a part of and then tell Nucleus to import those scans only. We also added the import all option for customers who want to bring in everything without too many manual steps. You can read more about the Veracode scanner updates here.
Your personal invite to our upcoming Nucleus Quarterly Product Update webinar
We’re excited to invite you to our next Nucleus Quarterly Product Update webinar on Wednesday, April 19, at 2 pm ET. Featuring our COO, Scott Kuffer and Director of Product, Rob Gibson, this session will be focused on new features and improvements we’ve made, plus a look ahead. This interactive webinar is always a hit and includes a dedicated Q&A session as the end of our formal presentation. Register here for access to the live event or on-demand recording afterward.
Click here to expand our full Release Notes
You can access the Nucleus change log to view the complete, unedited version of release updates posted each week. Select the subscribe to the RSS feed option on this page if you would like to receive weekly change log updates. This new Nucleus Product Update is intended to fully summarize and outline those weekly changes for you, with more details, each month. The product updates include all the following features and improvements:
New Features
- Added asset group access control so that Org Admins can restrict which asset groups their users can access in a project. Contact support or account management to activate.
Product Improvements (Performance, Experience, & Functionality)
- Improved efficiency of notifications pipeline so that jobs run more quickly.
- Added a range operator when setting Nucleus Risk Score as a condition in Ticketing automation.
- Added a column for the Nucleus Risk Score in the Vulnerability Details export.
- Added the last-connected-date to the response of the /projects/project_id/connectors API endpoint.
- Enhanced filtering by CVE number in the active vulns page at both the project level and global level to more easily filter by multiple CVEs.
- Improved filtering by Teams on the active vulns page to more easily filter by multiple teams.
- Added the ability to query by the “mitigated via scan” status in the findings search API. The status “Mitigated Via Scan” is now also returned from the finding mitigation statuses API.
Reporting Improvements
- Updated the Vulnerability Details xlsx report to include new columns in the host info tab for: asset type, asset owner team, support team, asset description, and asset groups.
Integration Improvements
AWS ECR:
- Improved the AWS ECR Basic connector so that we no longer ingest old images.
AWS S3:
- Improved files uploaded to AWS S3 buckets to have the mime-type of application/json so browsers automatically download them as the correct file type.
- Completed release of S3 connector as generally available.
- Fixed an issue in the S3 file upload so justification_assignee is represented as an object instead of a JSON encoded string.
InsightVM:
- Improved the InsightVM connector by increasing timeout length upon scan ingestion.
- Fixed an issue with InsightVM where manual ingests failed in certain scenarios.
Other:
- Improved the /findings/search endpoint to avoid 503s on especially large queries.
- Updated the /findings endpoint response code with 200 when querying for an asset with no findings.
Prisma Cloud:
- Updated Prisma Cloud connector to improve de-duplication of findings that have the same finding name.
- Fixed an issue in Prisma where CI image scans were not properly de-duplicating in certain cases where Prisma was inconsistently formatting ids.
Qualys:
- Improved Qualys retries in certain scenarios.
Rumble:
- Improved asset matching to avoid asset duplication and added a lot of new metadata.
- Adjusted the Rumble connector to only ingest live assets.
Tanium:
- Improved host matching to the Tanium connector.
Veracode:
- Adjusted Veracode connector so that findings are more unique for better de-duplication.
Bug Fixes
- Fixed an issue where the Active Vulnerabilities page stops displaying properly in some browsers.
- Fixed an issue with Nipper scans failing if the scans contained a “Potential Vulnerabilities” section.
- Fixed an issue with the Vulnerabilities view in the Global Dashboard not loading in certain scenarios.
- Fixed an issue with certain symbols importing incorrectly during custom file imports.
- Fixed an issue with compliance filters so applied filters are easier to view.
- Fixed an issue when setting a dynamic field to better handle fields that include spaces.
- Fixed an issue where the Support Team was not displayed in the Edit Asset window unless a Business Owner Team was set.
- Fixed several issues with metadata in Axonius:
- Prevented inappropriate transformation of Tenable uuid metadata from Axonius.
- Ensured that mac_address and operating_system_name fields are updated on assets.
- Fixed an issue where mitigated instances were not showing in the vulnerability details instances view.
- Fixed an issue in ServiceNow CMDB where ingestion failed where certain request URIs were exceeding character limits imposed by ServiceNow.
- Fixed an issue where the Teams filter was not filtering as expected in the Top Risks page.
- Adjusted group selection in the asset filter view so that asset groups and “ungrouped” cannot be selected simultaneously, thereby resulting in an error.
- Fixed an issue that was causing asset group rules to run slower than usual and caused the vuln details report to incorrectly render certain characters
- Fixed an issue that was causing scheduled Security Center asset based vulnerability ingests to result in an error.
- Fixed an issue where group filters were not persisting on scheduled reports.
- Fixed an issue where dynamically setting a support team in an Asset Processing rule was incorrectly setting the business owner team.