June 22, 2023 CISA KEV Breakdown | VMware, Roundcube, Mozilla, Microsoft

June 22: 6 New Vulns | CVE-2023-20887, CVE-2021-44026, CVE-2020-35730, CVE-2020-12641, CVE-2016-9079, CVE-2016-0165
In this CISA KEV Breakdown, six vulnerabilities were added to the CISA KEV catalog. Two come back from the past being Firefox and Win32k vulnerabilities from 2016, as well as three more-recent Roundcube vulnerabilities that were part of Russian threat actor’s targeting of Ukrainian Government entities, and finally a vulnerability in VMware Aria from this year.
[wptb id=22242]Notable Vulnerability Additions
CVE-2023-20887 | VMware Aria Command Injection
A vulnerability in VMware Aria allows for an attacker to achieve command injection when accepting user input through the Apache Thrift RPC interface. This vulnerability can be exploited remotely, and there are multiple proof-of-concepts available publicly. It can be successfully exploited when an attacker sends a malicious payload to the /saas./resttosaasservlet endpoint on a vulnerable system. Read more about the initial disclosure, as well as discovery and proof-of-concept from Summoning Team here.
According to user @Y4er_ChaBug on Twitter, this vulnerability exploit is actually a workaround to the patch applied for CVE-2022-31702, and this appears to be true given the technical details of both vulnerabilities.
GreyNoise has launched a tag to track exploitation and scanning activity surrounding CVE-2023-20887, as well as a blog. Below is an example packet containing the RCE attempt from the GreyNoise blog.

Security Advisory(s):
https://www.vmware.com/security/advisories/VMSA-2023-0012.html
CVE-2021-44026, CVE-2020-12641, CVE-2020-35730 | Roundcube Vulnerabilities
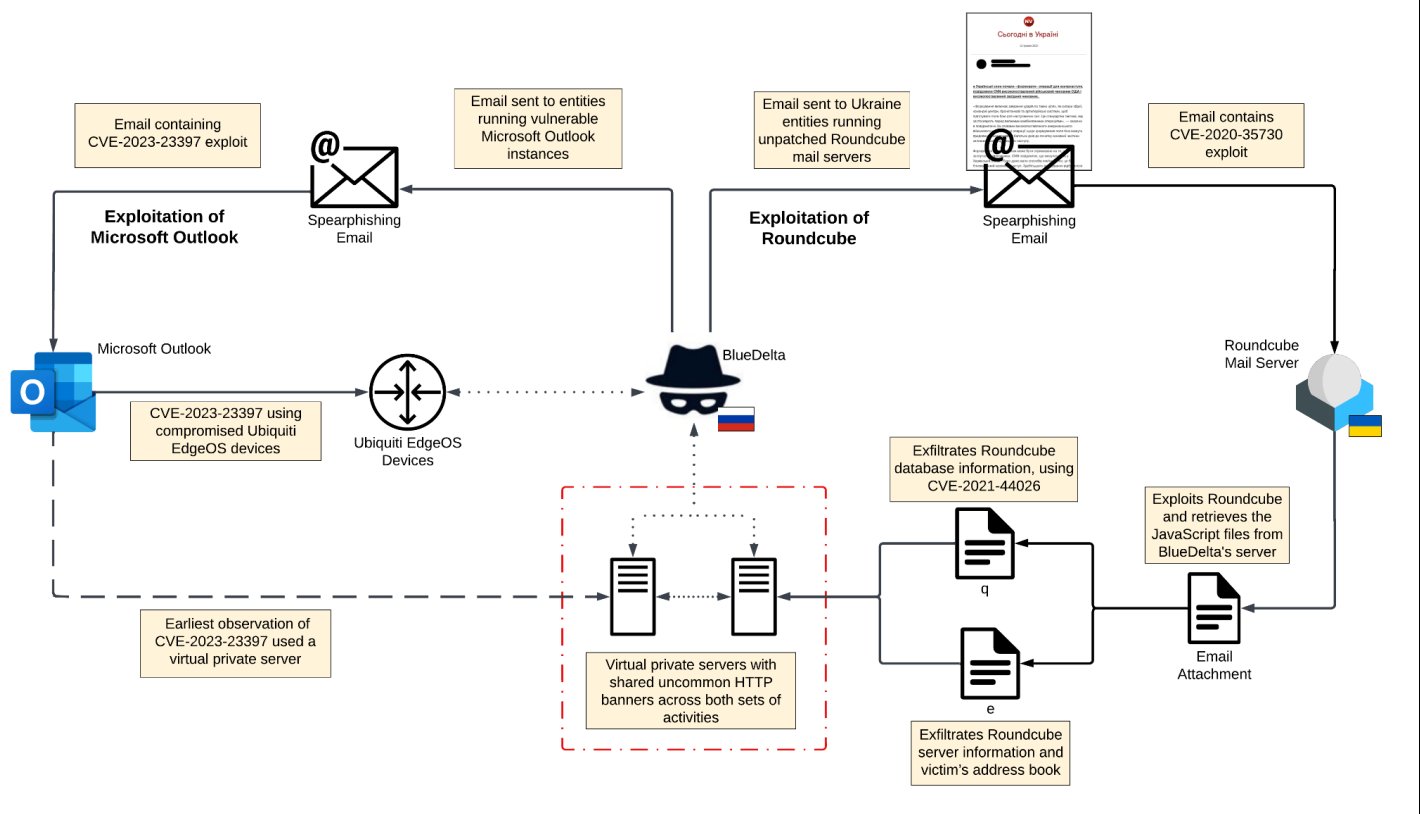
Recorded Future’s Insikt Group reported on June 20 in partnership with the Ukraine’s Computer Emergency Response Team a campaign targeting high-profile entities in Ukrainian government. The campaign consisted of separate highly sophisticated spearphishing emails against public-facing vulnerable Roundcube servers, as well as the exploitation of CVE-2023-23397 on edge devices to obtain further access that led to initial compromise.
Once gaining a foothold, the attackers would leverage further Roundcube exploits to exfiltrate data from Roundcube. The campaign has been linked to a historical actor dubbed BlueDelta which utilized CVE-2023-23397 in campaigns targeting the European sector as well as Ukraine.
CVE-2020-35730 is used initially to exploit vulnerable Roundcube email servers due to a link reference mishandling in rcube_string_replacer.php. The attack-chain attempts to utilize both this and CVE-2020-13965 as means of gaining further access into vulnerable Roundcube devices. Once further compromised, the attackers can then leverage CVE-2021-44026, a SQL injection vulnerability to exfiltrate data from the mail server.
While these campaigns have been primarily focused on European sectors according to interest from BlueDelta activity, it is encouraged for all organizations to assess their exposed perimeter devices for remotely exploitable vulnerabilities such as these Roundcube vulnerabilities.
Security Advisory(s):
CVE-2020-12641: https://roundcube.net/news/2020/04/29/security-updates-1.4.4-1.3.11-and-1.2.10
CVE-2020-35730: https://roundcube.net/news/2020/12/27/security-updates-1.4.10-1.3.16-and-1.2.13
CVE-2021-44026: https://roundcube.net/news/2021/11/12/security-updates-1.4.12-and-1.3.17-released
CVE-2016-0165 | Microsoft Win32k Privilege Escalation
A vulnerability exists in Win32k, specifically the win32kbase.sys driver component, which calculates a value in a struct represented by a 64 bit value, but is then placed in a 32 bit register, resulting in a potential for overflow to occur. To exploit the vulnerability, an attacker would first need to gain local access to the machine. Exploit code has existed publicly for nearly as long as it’s date of disclosure.
The vulnerability was uncovered as a 0-day and reported as exploited in the wild in Google Threat Analysis Group’s (TAG) 0day Tracker Sheet. Since exploitation activity as well as a patch have been known for quite some time, this vulnerability was reported to CISA by Nucleus’ own Patrick Garrity and suggested it be added to the KEV due to meeting the required criteria.
Security Advisory(s):
https://learn.microsoft.com/en-us/security-updates/securitybulletins/2016/ms16-039
CVE-2016-9079 | Mozilla Firefox & Thunderbird Use-After-Free
A vulnerability exists in Firefox before version 50.0.2, Firefox ESR before version 45.5.1, and Thunderbird before version 45.5.1 that can allow an attacker to execute code. An attacker would first need to convince a user, likely through the use of social engineering, to interact with a malicious application crafted by the attacker. It was reported around date of disclosure that this vulnerability was primarily exploited as a means to identify information on users behind Tor browsers, since Tor is based on Firefox. This vulnerability was also referenced in having been exploited in the wild in Google TAG’s 0day Tracker Sheet.
Since exploitation activity as well as a patch has been known for quite some time, this vulnerability was reported to CISA by Nucleus’ own Patrick Garrity and suggested it be added to the KEV due to meeting the required criteria.
Security Advisory(s):
https://www.mozilla.org/en-US/security/advisories/mfsa2016-92/#CVE-2016-9079
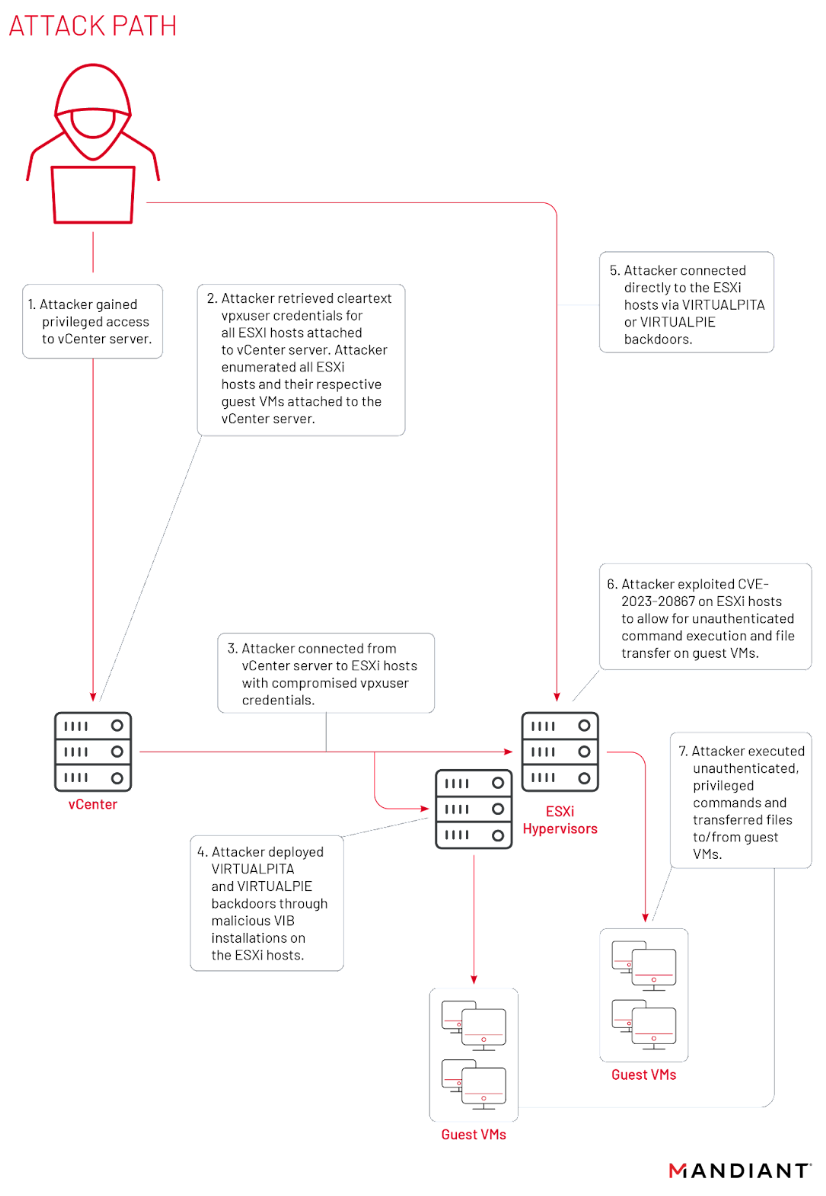
Footnote – CVE-2023-20867
Nucleus Security is also aware of CVE-2023-20867 which is a VMware ESXi 0-day that has been confirmed as exploited by Mandiant. They report in their blog that a novel malware system developed by UNC3886 was used to backdoor VMware ESXi hosts, vCenter servers and Windows virtual machines. The exploitation of CVE-2023-20867 was sophisticated and executed under the noses of EDR for quite some time. As of recently, a fix has been available by the VMware team, as well as SUSE. Organizations are encouraged to assess impact from this vulnerability as we predict that is likely to be added to the KEV soon.
← June 13, 2023 CISA Kev Breakdown
Click here to expand our CISA KEV Breakdown Frequently Asked Questions
- What makes for a notable addition?
- A notable addition can arise from many different characteristics. If a particular vulnerability is notable to the security community or a subset of the security community or if the EPSS score reveals notable information about the vulnerability, this can constitute further analysis. It may also be the case that a particular vulnerability shines a light on everyday users and we will highlight important information and key takeaways to ensure users and readers have easy access to actionable information.
- When is the Breakdown released?
- We aim to have our analysis of each KEV update posted within 24 hours of the time in which the Catalog is updated. See CISA’s full catalog here
- I am not bound by BOD 22-01 or federal regulations, why should the KEV concern me?
- CISA encourages all organizations to utilize the Catalog as an attribute in your vulnerability prioritization framework. Organizations looking to lessen the scope on known dangerous vulnerabilities and make a goal to remediate them can understand where they currently stand against what CISA has confirmed as exploited vulnerabilities in the wild. See CISA’s section on “How should organizations use the KEV catalog?” here.
- What is EPSS?
- EPSS is the Exploit Prediction Scoring System. It is an open, data-driven effort for estimating the likelihood (probability) that a software vulnerability will be exploited in the wild. See the EPSS home page on FIRST for more information here.
- What is the difference between EPSS probability and EPSS percent?
- EPSS probability is the risk calculated by the model when determining the perceived threat of the vulnerability itself. Percentage is a relative comparison of the rest of the CVEs within the given sample. While the probability only changes upon refreshing the results from the model, the percentage can change purely based on the CVE sample given. In the case of the Breakdown, we use the percentage given by the pool of all CVEs with given EPSS data. Scores may vary post-release of the post given new information about the vulnerabilities and their perceived threat. For more information on applying and understanding EPSS data, see this article on the FIRST website, as well as their FAQ page.
- What is GreyNoise?
- GreyNoise is a platform that collects, analyzes, and labels data on IPs that scan the internet and saturate security tools with noise. Through their sensor network, GreyNoise observes vulnerability exploitation attempts for vulnerabilities that are exploited in the wild over the Internet. These are arguably vulnerabilities that should be at the very top of your priority list to remediate.
- Why are GreyNoise exploitation attempts only observed on ~20% of KEV vulnerabilities?
- Exploitation of many vulnerabilities in the CISA KEV will not be observed for many reasons that GreyNoise does a good job of explaining in this post. For example:
- The vulnerability may not be remotely exploitable
- Vulnerability exploitation may require authentication (and result in privilege escalation)
- The impacted software may not be exposed to the internet
- Mass scanning/exploitation is not occurring yet
- Exploitation of many vulnerabilities in the CISA KEV will not be observed for many reasons that GreyNoise does a good job of explaining in this post. For example:
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.