EPSS Score Is Predictive, but Late: What 18% of CISA KEV Vulnerabilities Reveal
Part 2 of 4 | The Exploitability Intelligence Gap Research Series

EPSS is a predictive scoring model, and security teams assume it is an early warning signal. Nucleus research across 18% of CISA KEV-listed CVEs over 6 months found it isn’t.
Vulnerability management teams are drowning in CVEs. With tens of thousands published every year and only a fraction worth escalating, teams are hunting for signals that can help them defend before exploitation happens. EPSS is one of the most commonly used signals because it promises something scarce: a quantitative, data-driven estimate of exploitation likelihood in the next 30 days that teams can plug directly into their vulnerability prioritization workflows. However, using a rising EPSS score as an early-warning signal on its own is an operational mistake.
EPSS was not designed to be an early warning signal. Teams often assume a rising score means exploitation is imminent, but while a probability signal can be accurate, it can still arrive late. By the time exploitation is confirmed on a KEV list, attackers may already have a head start. So, at what point in time does EPSS move enough for defenders to act?
What We Found: EPSS Moves 121x More After a CVE Hits KEV
To understand how early or how late EPSS reflects real-world exploitation risk, Nucleus studied 22 of the 122 CVEs added to the CISA KEV catalog between October 2025 and March 2026, representing 18% of KEV additions in that window. For each one, we analyzed how the EPSS score changed before and after KEV listing (the point at which active exploitation is publicly confirmed), and when the score crossed common prioritization thresholds of 1%, 10%, and 50%.
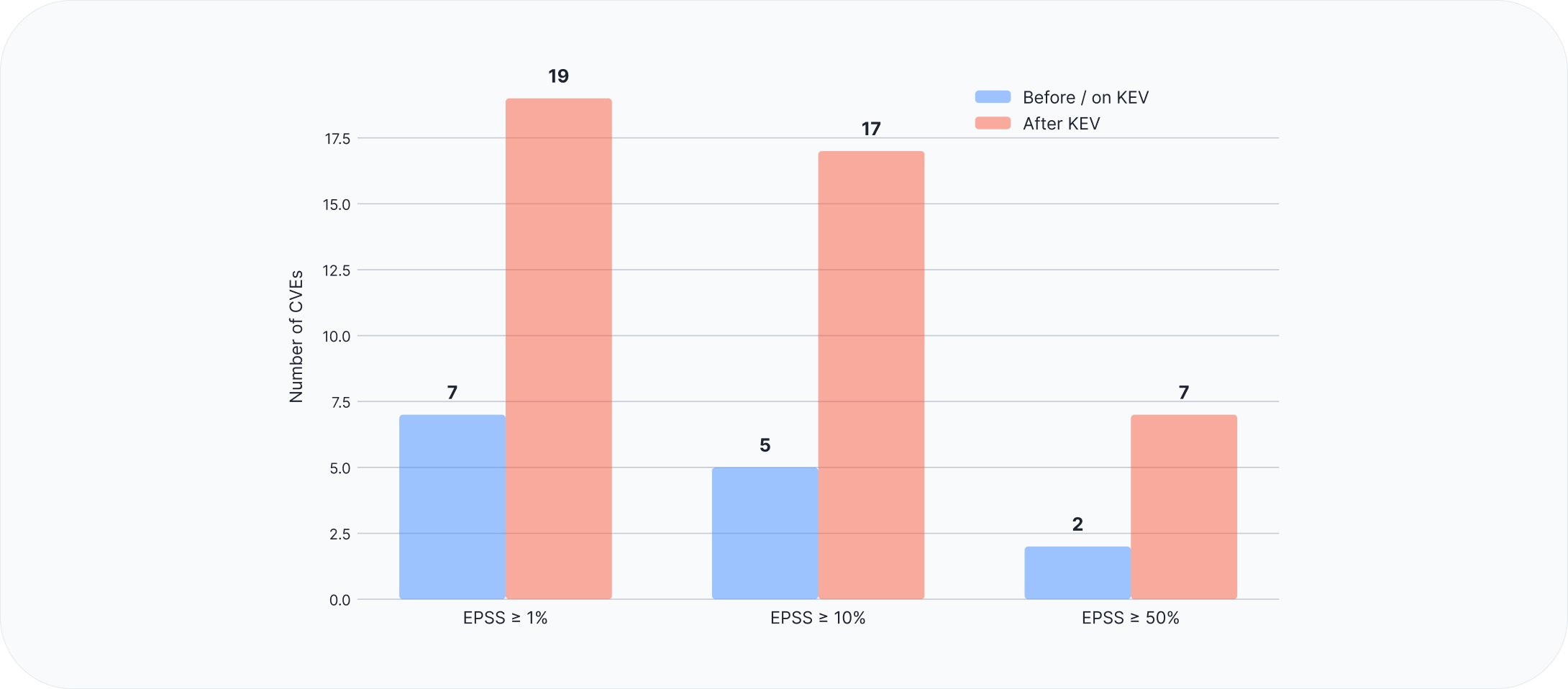
The key finding is that EPSS is not acting as an early signal, because the median EPSS movement was 121 times larger after KEV than before. In other words, the score that’s supposed to give vulnerability management teams a head start barely moves until CISA has already confirmed the risk. That’s the same pattern we highlighted in Part 1 of this blog series, where risk was already real before the signals could catch up. In that analysis, 8 of these 22 CVEs were already being exploited before KEV listing.
But if EPSS isn’t moving early, when does it actually rise?
The Real EPSS Spike Lands Two Days After KEV Listing
The data shows that the EPSS spike seen two days after a CVE is listed on KEV (KEV+2 days) isn’t just the largest single-day movement in the dataset; it’s the dominant feature. It shows up across every vulnerability we studied. All 22 vulnerabilities showed a positive jump in EPSS on the second day after being added to the KEV catalog, reinforcing that this is not an isolated spike but a systematic response.
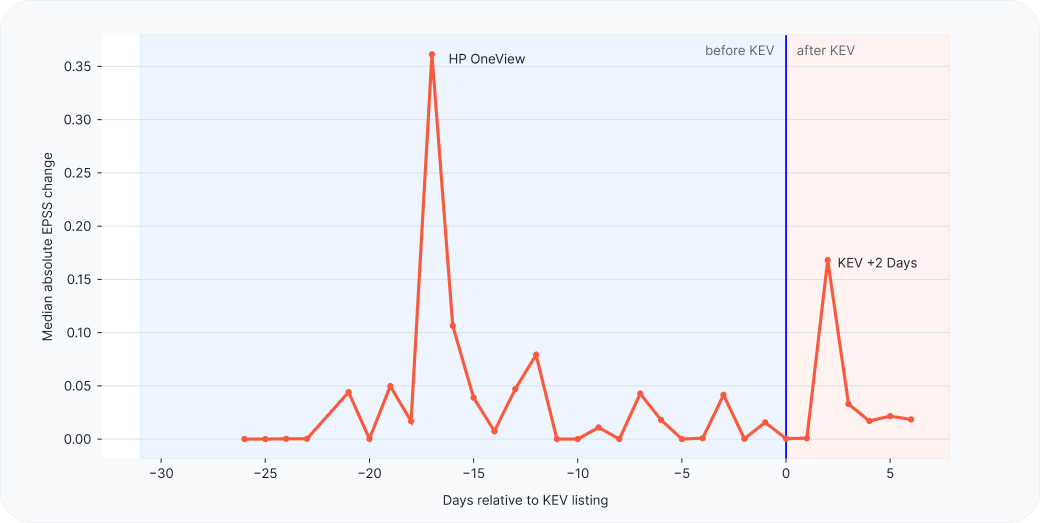
The most interesting finding is how concentrated the movement is in such a short window. The KEV+2 mark alone accounts for 54% of all absolute EPSS change across six months of KEV additions, and the first three days after KEV listing account for 89% of all post-KEV movement. A score meant to provide a 30-day head start is doing most of its work within 72 hours after being listed on KEV. By then, it’s not really an early warning; it’s a confirmation signal.
Why Teams Mistake EPSS for an Early-Warning Signal
If EPSS consistently arrives late, why do teams keep mistaking it for an early-warning signal? The answer is that EPSS tends to rise early only when a vulnerability is already getting attention from multiple sources at the same time. HPE OneView is the perfect example, showing strong EPSS movement before KEV inclusion, despite no confirmed pre-KEV exploitation. On its own, this appears to demonstrate the early-warning behavior teams expect from EPSS. However, HPE OneView had several clear signals firing at once before CISA listed it:
- Public PoC was available.
- Widespread media and security community coverage.
- Exploit weaponization activity was already underway.
- Patch availability created urgency for defenders.
- The broader security community was actively focused on the CVE all at once.
EPSS isn’t really discovering risk; it’s reacting to it. The score goes up when a CVE starts getting attention across the ecosystem. In our sample, the other 21 vulnerabilities didn’t hit that level of attention until after KEV listing. By that point, exploitation was already known and spreading, so EPSS was catching up, not getting ahead.
This also helps explain why a public proof-of-concept (PoC) on its own doesn’t have the same impact. Without broader signals like media coverage, active exploit development, or patch context, early PoC activity rarely moves EPSS in a meaningful way. As a result, a prioritization strategy based only on EPSS will catch the most visible, high-noise cases while missing the rest.
That leads to a bigger question: which signals should vulnerability management teams rely on to act first, and where does EPSS fit once those signals are already in play?
Where EPSS Belongs in the Vulnerability Management Prioritization Stack
Effective, risk-based vulnerability management requires teams to use a prioritization model that works for the typical CVE, not just the loudest ones. If EPSS often rises after KEV inclusion, the key question is where it fits in the process. Our research suggests that EPSS is most effective as part of a layered vulnerability prioritization model that combines and unifies the upstream signals that actually move first.
To operationalize EPSS for proactive vulnerability management, security teams can use Nucleus Insights, which combines AI-driven, analyst-curated exploitability intelligence with operational context in one place. It consolidates fragmented signals directly into vulnerability and exposure management workflows, while the Nucleus Threat Rating unifies fragmented signals into a clear view of real-world risk based on indicators such as confirmed exploitation, likely exploitation, malware use, OT impact, and public exploit availability. Together, these capabilities enable faster, more confident prioritization and remediation.
Attackers Don’t Wait for EPSS
Programs that wait for EPSS thresholds to be crossed are acting on a signal that often comes after the risk has already been validated. EPSS is valuable, but not the first signal to watch. Attackers, meanwhile, aren’t waiting on it. They operate on their own timeline, exploiting CVEs based on the same upstream signals defenders struggle to consolidate, such as public PoC, weaponization activity, patch availability, and vendor advisories. Some may even use the EPSS lag in their favor, knowing that as long as the score stays low, defender patching tends to stay slow.
That window, between when a vulnerability becomes exploitable and when EPSS catches up, is the exploitability intelligence gap. Nucleus closes it by aggregating those earlier signals, such as confirmed exploitation, public PoC, weaponization, vendor intelligence, and media activity, and weighting them in a layered model so teams can act on early evidence instead of waiting for downstream confirmation.
Download the Exploitability Intelligence Gap whitepaper →
Want to see how Nucleus closes the gap in practice? Request a demo.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.

































