KNOWLEDGE CENTER
What Is Unified Vulnerability Management?
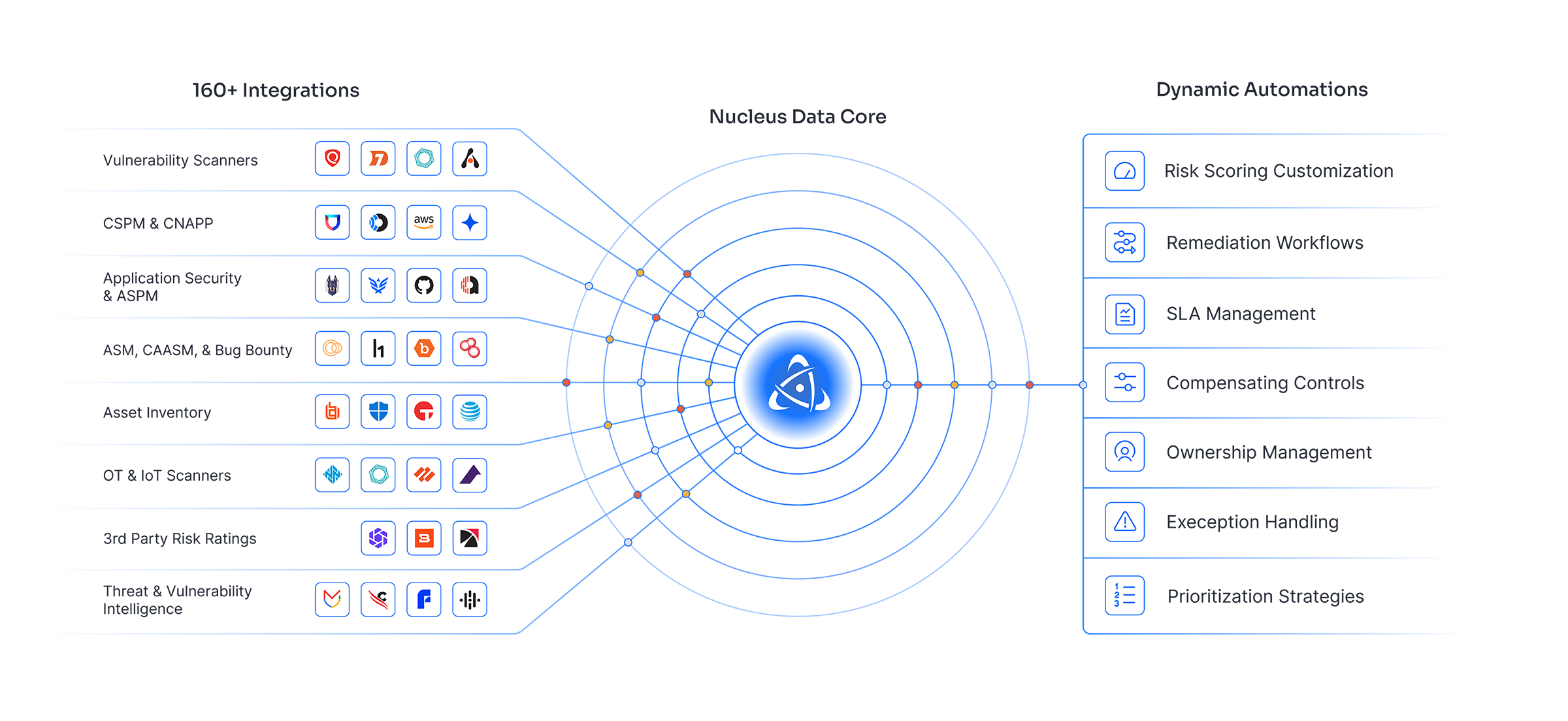
Unified vulnerability management is a cybersecurity approach that consolidates vulnerability data from multiple tools and sources into a single platform to provide centralized visibility, risk prioritization, and coordinated remediation.
Why Unified Vulnerability Management Matters
Modern organizations rely on multiple security tools to scan networks, applications, cloud environments, and configurations. This creates fragmented data and operational silos.
Unified vulnerability management solves this by:
- Aggregating data from multiple scanners and tools
- Normalizing and deduplicating findings
- Prioritizing vulnerabilities based on real business risk
- Enabling coordinated remediation across teams
Without a unified approach, security teams often lack full visibility into their risk exposure.
Key Benefits of Unified Vulnerability Management
Centralized Visibility
A unified platform provides a single view of vulnerabilities across all environments, including network, application, cloud, and endpoint systems.
Improved Risk Prioritization
By combining vulnerability data with asset context and threat intelligence, teams can focus on the issues that pose the greatest risk.
Reduced Tool Fragmentation
Organizations can continue using best-of-breed tools while consolidating their outputs into one system.
Faster Remediation
Unified workflows streamline ticketing, ownership assignment, and tracking, reducing time to remediation.
How Unified Vulnerability Management Works
A unified vulnerability management platform typically:
- Ingests data from multiple scanners and security tools
- Normalizes and correlates findings across sources
- Enriches data with threat intelligence and asset context
- Prioritizes risk using a consistent scoring model
- Distributes remediation tasks to appropriate teams
This approach ensures that vulnerabilities are evaluated consistently across the entire attack surface.
Challenges Without a Unified Approach
Organizations that rely on disconnected tools often face:
- Inconsistent risk scoring across systems
- Limited visibility into overall risk posture
- Difficulty prioritizing across vulnerability types
- Operational inefficiencies due to siloed workflows
Attackers do not differentiate between vulnerability types, making unified visibility essential.
Unified Vulnerability Management vs. Traditional Approaches
| Unified Vulnerability Management | Traditional Vulnerability Management |
|---|---|
| Centralized visibility | Tool-specific visibility |
| Unified workflows | Separate workflows |
| Context-driven prioritization | Limited context |
| Automated correlation | Manual correlation |
Frequently Asked Questions
What is unified vulnerability management in simple terms?
It is a way to combine vulnerability data from multiple tools into one system to improve visibility and prioritize risk.
Is unified vulnerability management the same as exposure management?
Not exactly. Unified vulnerability management focuses on consolidating vulnerability data, while exposure management expands to include broader risk factors.
Do organizations still need multiple tools?
Yes. Unified platforms integrate existing tools rather than replacing them.
Key Takeaways
- Unified vulnerability management centralizes security data
- It improves risk prioritization and remediation efficiency
- It reduces tool fragmentation and operational complexity
- It is essential for managing modern, complex attack surfaces
Related Resources
Want to See Nucleus in Action?
Watch our demo on-demand.































