July 11, 2023 CISA KEV Breakdown | Microsoft, Netwrix

July 11: 5 New Vulns | CVE-2023-32049, CVE-2023-35311, CVE-2023-36874, CVE-2023-32046, CVE-2022-31199
In this CISA KEV Breakdown, four known-to-be-exploited vulnerabilities with two being 0-days from Microsoft’s July patch Tuesday update find their home in the KEV, as well as a Netwrix Auditor bug from 2022. For some by-the-numbers reporting related to patch Tuesday, check out BleepingComputer’s piece here.
[wptb id=22311]Notable Vulnerability Additions
CVE-2023-32049 | Microsoft Defender SmartScreen Security Bypass
A vulnerability in Defender SmartScreen was one of six vulnerabilities known to be exploited from this patch Tuesday, this feature has been long known to be continuously tested by attackers to bypass. Three bypass vulnerabilities now belong to the KEV from this technology alone.
Exploit code does not appear to be publicly available at this time, however vulnerabilities like this are typically popular for security researchers post-disclosure to release writeups detailing the bug.
It can be considered a testament to the fact that attackers, given one of the most common attack vectors in existence, will continue to find ways to streamline it.
This technology is one of many roadblocks that attackers continuously overcome as a means to deliver phishing emails in which the malicious attachment or landing URL attempts to bypass the ‘Open File’ popup from Defender when a suspicious file is opened.
Vulnerabilities such as this are when security teams should ensure strong defense-in-depth approaches are in place when a situation occurs causing a user to be exploited by this attack. This popup should be one of many more roadblocks for the attacker, and not the final one.
Security Advisory(s):
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2023-32049
CVE-2023-35311 | Microsoft Outlook Security Bypass
A vulnerability in the Outlook application’s preview pane security features can allow an attacker to exploit a user’s Outlook application by convincing a user to click a malicious URL. Exploit code does not appear to be publicly available at this time. Typically, vulnerabilities such as this and CVE-2023-32049 are quick to be incorporated into phishing campaigns. Exploit code does not appear to be publicly available at this time.
This vulnerability affects multiple versions of Outlook, and luckily requires user interaction to be exploited by an attacker. Typically vulnerabilities such as this that pose a far higher risk are when the preview pane is specifically affected in a way that previewing the email exploits the Outlook application to execute arbitrary commands.
Security Advisory(s):
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2023-35311
CVE-2023-36874 | Microsoft Error Reporting Privilege Escalation
A vulnerability in multiple Windows (10, 11) and Windows Server (2008, 2012, 2019, 2022) versions can allow an attacker to exploit and gain adminstrator privileges. Exploit code does not appear publicly available at this time. Limited information exists as to the attack path for the Error Reporting functionality to cause escalation to administrator.
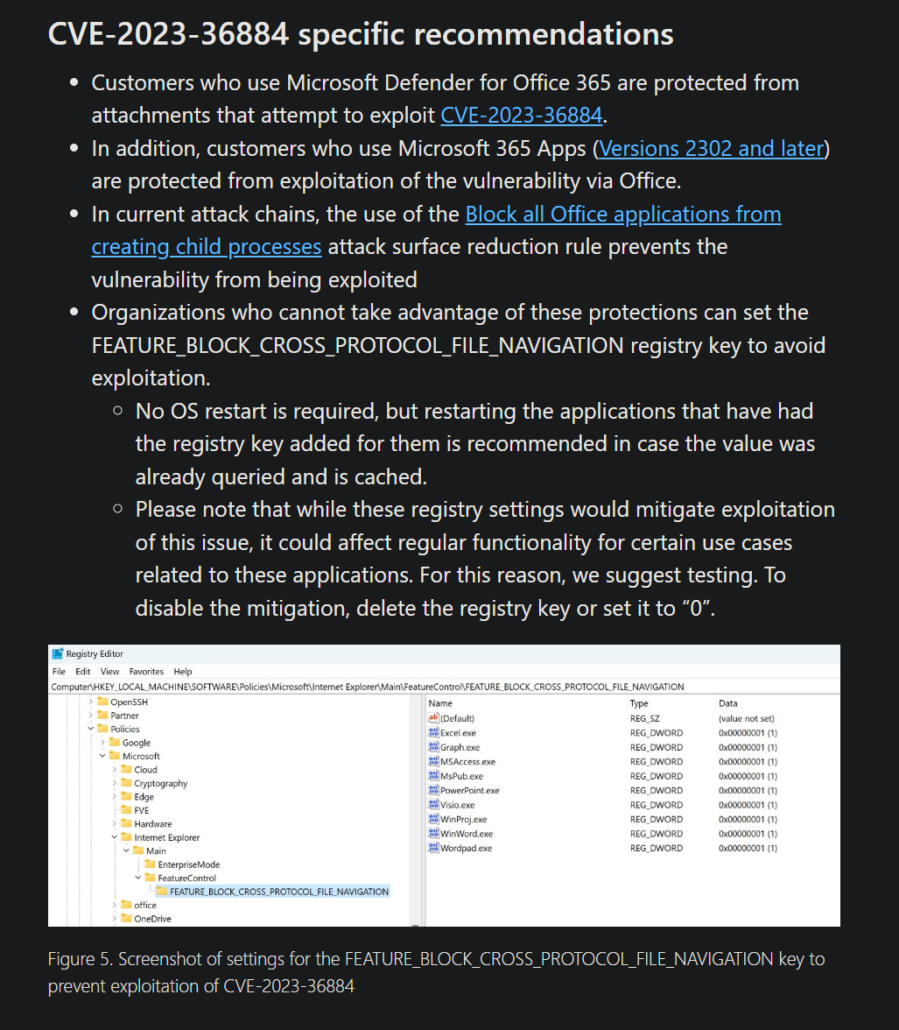
The folks over at Google TAG were first to discover this 0-day as well as CVE-2023-36884, which does not appear to have been added to the KEV yet. This is likely due to the fact that current mitigation surrounding CVE-2023-36884 is not yet a complete patch, but a recommended workaround from Microsoft in their blog linking exploitation of the flaw to Storm-0978.
Security Advisory(s):
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2023-36874
CVE-2023-32046 | Microsoft MSHTML Privilege Escalation
A vulnerability in the Windows MSHTML platform in multiple Windows (10, 11) and Windows Server (2008, 2012, 2019, 2022) versions can allow an attacker to escalate privileges. The vulnerability appears to require user interaction according to the details released by Microsoft.
Exploit code does not appear to be publicly available at this time, and much like CVE-2023-36884 there exists little information as to how this is exploited.
Microsoft MSHTML has been historically exploited in similar capacity to the other discussed vulnerabilities, in that user interaction through clicking a malicious attachment or interacting with a malicious landing page causes the user to execute malicious code with elevated privileges for the attacker.
Security Advisory(s):
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2023-32046
CVE-2022-31199 | Netwrix Auditor Code Execution
With the highest EPSS score of the bunch, the Netwrix Auditor contains a vulnerability prior to version 10.5 that a remote attacker can exploit to execute arbitrary code. This vulnerability was included in a joint advisory by CISA and other federal agencies. It was reported in the advisory that the vulnerability was used as a means of initial access by threat actors deploying Truebot malware.
If an actor were able to deploy Truebot malware for command and control, the file renames itself and loads FlawedGrace, in hopes to escalate privileges as well as establish persistence. Due to the extensive understanding of the attack path in public knowledge, and the fact that a remote unauthenticated actor can perform exploitation, organizations should be greatly encouraged to move Auditor boxes off the public internet, and to update to non-vulnerable version 10.5.10977.0+.
Security Advisory(s):
Requires login information: https://security.netwrix.com/Account/SignIn?ReturnUrl=%2FAdvisories%2FADV-2022-003
← July 7, 2023 CISA Kev Breakdown
Click here to expand our CISA KEV Breakdown Frequently Asked Questions
- What makes for a notable addition?
- A notable addition can arise from many different characteristics. If a particular vulnerability is notable to the security community or a subset of the security community or if the EPSS score reveals notable information about the vulnerability, this can constitute further analysis. It may also be the case that a particular vulnerability shines a light on everyday users and we will highlight important information and key takeaways to ensure users and readers have easy access to actionable information.
- When is the Breakdown released?
- We aim to have our analysis of each KEV update posted within 24 hours of the time in which the Catalog is updated. See CISA’s full catalog here
- I am not bound by BOD 22-01 or federal regulations, why should the KEV concern me?
- CISA encourages all organizations to utilize the Catalog as an attribute in your vulnerability prioritization framework. Organizations looking to lessen the scope on known dangerous vulnerabilities and make a goal to remediate them can understand where they currently stand against what CISA has confirmed as exploited vulnerabilities in the wild. See CISA’s section on “How should organizations use the KEV catalog?” here.
- What is EPSS?
- EPSS is the Exploit Prediction Scoring System. It is an open, data-driven effort for estimating the likelihood (probability) that a software vulnerability will be exploited in the wild. See the EPSS home page on FIRST for more information here.
- What is the difference between EPSS probability and EPSS percent?
- EPSS probability is the risk calculated by the model when determining the perceived threat of the vulnerability itself. Percentage is a relative comparison of the rest of the CVEs within the given sample. While the probability only changes upon refreshing the results from the model, the percentage can change purely based on the CVE sample given. In the case of the Breakdown, we use the percentage given by the pool of all CVEs with given EPSS data. Scores may vary post-release of the post given new information about the vulnerabilities and their perceived threat. For more information on applying and understanding EPSS data, see this article on the FIRST website, as well as their FAQ page.
- What is GreyNoise?
- GreyNoise is a platform that collects, analyzes, and labels data on IPs that scan the internet and saturate security tools with noise. Through their sensor network, GreyNoise observes vulnerability exploitation attempts for vulnerabilities that are exploited in the wild over the Internet. These are arguably vulnerabilities that should be at the very top of your priority list to remediate.
- Why are GreyNoise exploitation attempts only observed on ~20% of KEV vulnerabilities?
- Exploitation of many vulnerabilities in the CISA KEV will not be observed for many reasons that GreyNoise does a good job of explaining in this post. For example:
- The vulnerability may not be remotely exploitable
- Vulnerability exploitation may require authentication (and result in privilege escalation)
- The impacted software may not be exposed to the internet
- Mass scanning/exploitation is not occurring yet
- Exploitation of many vulnerabilities in the CISA KEV will not be observed for many reasons that GreyNoise does a good job of explaining in this post. For example:
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.