Understanding CISA BOD 23-01: Improving Asset Vulnerability and Detection on Federal Networks
Last November, the Cybersecurity and Infrastructure Security Agency (CISA) released Binding Operational Directive 22-01, which led to the creation of CISA’s Known Exploited Vulnerabilities list, one of the best free resources of vulnerability intelligence available today. Here at Nucleus, we’ve talked a lot about the benefits of the KEV list and have even created our own CISA KEV Enrichment Dashboard to help layer additional enrichment intelligence onto vulnerability prioritization.
Recently on October 3rd, 2022, nearly a year after BOD 22-01 was released focusing on the reduction of risk attributed to known exploited vulnerabilities, CISA followed up with Binding Operational Directive (BOD) 23-01 – Improving Asset Visibility and Vulnerability Detection on Federal Networks.
“A binding operational directive is a compulsory direction to federal, executive branch, departments and agencies for purposes of safeguarding federal information and information systems … These directives do not apply to statutorily defined ‘national security systems’ or to certain systems operated by the Department of Defense or the Intelligence Community. This directive refers to the systems to which it applies as ‘Federal Civilian Executive Branch’ systems, and to agencies operating those systems as ‘Federal Civilian Executive Branch’ agencies.” – CISA.gov
To help you better understand CISA BOD 23-01 and learn how your organization can comply with this new CISA directive, we’re breaking it down and mapping out how Nucleus can help your organization meet its requirements.
The Requirements of CISA BOD 23-01
CISA BOD 23-01 specifically aims to improve asset visibility and vulnerability detection on federal networks by setting accelerated timeframes for the cadence of specific tasks, such as asset discovery and vulnerability enumeration. However, achieving the goals of this new CISA directive requires a vulnerability management strategy involving a broad set of people skills, processes, and tools that you may or may not have. Alternatively, using a vulnerability management platform built to unify, align, and empower your existing systems and resources can help you meet these and future CISA requirements more efficiently.
Nucleus maps to many of the specific requirements outlined by CISA BOD 23-01. We make it easy to identify gaps and store artifacts in one place and position you and other agencies to quickly meet the requirements of CISA BOD 23-01, plus the earlier CISA BOD 22-01. Nucleus also ensures coverage for any future CISA requirements involving asset and vulnerability discovery, enumeration, and remediation.
Though Nucleus covers most of the specific requirements outlined in CISA BOD 23-01, here’s a few of our favorites:
Automated Asset Discovery
CISA BOD 23-01 calls for asset discovery every seven days — approximately four times the rate of a typical patching interval and twice the rate of vulnerability enumeration. Performing discovery twice as frequently as your vulnerability enumeration allows you to identify and correct gaps quicker than before. Having a tool that is built to support a more aggressive cadence of asset discovery at scale makes this task achievable.
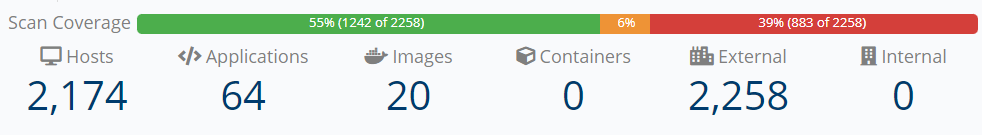
At Nucleus, we believe that vulnerability management begins with a good asset inventory and we built our platform to support it. Our asset management module includes a thermometer across the top of the user interface showing scan health with color-coded statuses to represent your different systems. Assets in red are systems Nucleus knows about and imported from your org’s existing asset inventories but hasn’t seen in your scan data. Systems in yellow have been scanned but haven’t been seen in more than 90 days, and therefore need investigation as to whether they are still live. Systems in green are being seen regularly.
As your environment changes, Nucleus does the same. Using asset processing rules, Nucleus can remove assets automatically as they are decommissioned. If the inventory system has a flag in its metadata stating whether a system is live, Nucleus can trigger off that metadata element. Asset removal rules run automatically after each scan is completed. If the asset management tool does not have such a facility, Nucleus can remove assets based on their absence from scans. The duration is set by the user and can be either time based or based on a number of scans. Assets can be completely removed or archived, which preserves the systems’ full history. If a system comes back, it comes back with its full history intact.
Asset processing rules also facilitate creating groups of assets, allowing Federal agencies to track assets and vulnerabilities on a system-by-system basis, not just at an agency-wide level.
Vulnerability Enumeration
CISA BOD 23-01 calls for vulnerability enumeration at approximately two times the rate of a typical patching interval. Performing enumeration twice as frequently as updates allows for the capture of both a before and after state, while still measuring progress in between. Nucleus has the functionality to support aggressive vulnerability enumeration, as well.
In addition to correlating vulnerability enumeration results against asset discovery results, Nucleus provides discovered and last seen dates, making it easy to sort every enumerated vulnerability based on its age. Your security analysts can also set due dates for each vulnerability enumerated, either manually or using automated rules. As future vulnerability enumeration indicates vulnerabilities have been remediated, Nucleus will update their state automatically. Additionally, when a vulnerability is in progress or is waiting on a third party, Nucleus users can set status to reflect that activity, add notes, and attach artifacts to help facilitate records management. This provides an audit trail for tracking compensating controls and handling false positives.
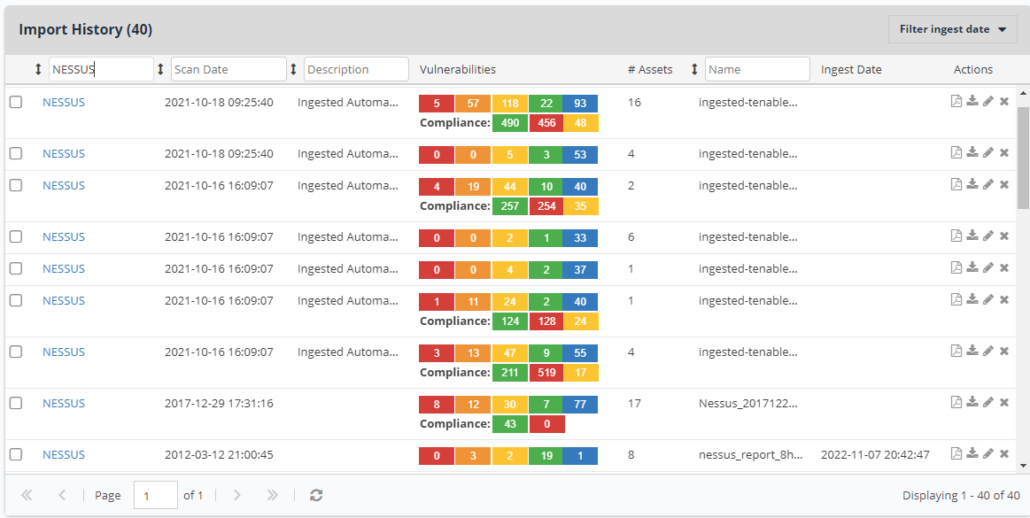
Nucleus also has a facility to notify users when vulnerability enumeration imports fail. Nucleus can import scans on a set schedule, and the scan import logs serve as a useful check that scans are indeed occurring on a regular basis. Each log entry contains a date and a basic count of the number of new or changed findings contained in the scan.
Implementing Policies with Processing and Ticketing Rules
Once integrations with other tools are in place, rules can be created within the Nucleus application to set due dates. Processing rules run after every scan import and results are displayed within the user interface. Rather than spending hours figuring out where you stand in terms of meeting due dates, Nucleus allows you to find that answer in seconds.
Remediation due dates typically have a pattern to them, based on severity, exploit activity, or some combination of the two. This gives the due dates some level of predictability. Your security analysts can use this information to create processing rules, which save considerable manual work. When exceptions to these rules occur, including but not necessarily limited to a vulnerability becoming part of the CISA Known Exploited Vulnerabilities (KEV) list, your security analysts can override due dates manually when needed.
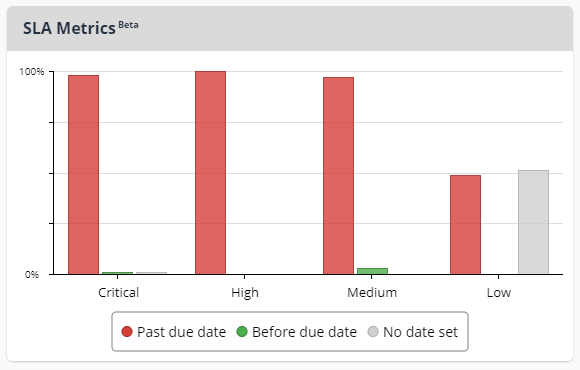
Nucleus provides a bar graph measuring compliance with due dates right on its main project dashboard page, providing useful remediation metrics on demand.
How Nucleus Helps Organizations comply with CISA BOD 23-01
Here is the full breakdown of how Nucleus maps to the different requirements within CISA BOD 23-01:
| CISA BOD 23-01 Requirement | Nucleus Capability |
| Perform automated asset discovery every 7 days. | Nucleus imports data from your asset discovery tools (i.e., runZero, Axonius, Nmap) and automatically correlates the data against your vulnerability enumeration. Nucleus also tracks last seen dates to support reviews for stale inventory. Retired assets can be archived either manually or via automated processing rules. |
| Initiate vulnerability enumeration across all discovered assets, including all discovered nomadic/roaming devices (e.g., laptops), every 14 days. | Nucleus imports vulnerability data from leading vulnerability scanners (i.e. Tenable Nessus, Qualys, Retina), correlates the data against asset discovery, and shows any gap in coverage directly in the user interface. Nucleus also provides last seen dates in the user interface and enables users to sort by those. |
| To the maximum extent possible and where available technologies support it, all vulnerability enumeration performed on managed endpoints (e.g., servers, workstations, desktops, laptops) and managed network devices (e.g., routers, switches, firewalls) must be conducted with privileged credentials (for the purpose of this directive, both network-based credentialed scans and client- or agent-based vulnerability detection methods are viewed as meeting this requirement). | Most vulnerability scanners have the ability to report whether a scan occurred with credentials and whether they had sufficient privileges as informational findings. Nucleus has the unique ability to pin those related findings to bring attention to them when authentication fails, and to open tickets based on any failures indicated by those findings.Sometimes scanners are not able to perform credentialed scans on certain brands of network devices. Nucleus can track these exceptions in one place – attached to the finding – making it easy to locate the documentation for auditors. |
| All vulnerability detection signatures used must be updated at an interval no greater than 24 hours from the last vendor-released signature update. | Most vulnerability scanners report the version number of their signatures as an informational finding. Nucleus can pin that finding for easy reference. |
| All alternative asset discovery and vulnerability enumeration methods (e.g., for systems with specialized equipment or those unable to utilize privileged credentials) must be approved by CISA. | Nucleus can attach documents and other artifacts to findings, making it easy to store these approvals so they can be produced on demand in the future. |
| Six, twelve, and eighteen months after the issuance, FCEB agencies will either: (1) Provide CISA (through a reporting interface in CyberScope) a progress report to include any obstacles, dependencies, or other issues that may prevent them from meeting the directive requirements and expected completion dates, OR (2) Work with CISA through the CDM program review process outlined in OMB M-22-05, or superseding guidance, to identify and resolve gaps or issues that prevent full operationalization of asset management capabilities, including those requirements in this directive. | Nucleus integrates with vulnerability scanners and ticketing tools, making it easy to track any back-and-forth communications regarding any given finding. Using a combination of finding statuses and comments, a user can quickly locate any obstacles, dependencies, or other issues without having to rely on e-mail and spreadsheets. |
Nucleus Makes It Easier to Comply with CISA BOD 23-01
Though the requirements outlined in CISA BOD 23-01 can be daunting to implement, they leave the possibility open for a future directive regarding patching and remediation. Nucleus makes it easier to provide evidence that current requirements are being met and is ready to help federal agencies meet future requirements. Nucleus was built from its onset with National Institute of Standards and Technology (NIST) Special Publication (SP) 800-40, Guide to Enterprise Patch Management, in mind. Nucleus is FedRAMP in-process, and the only solution of its kind listed in the FedRAMP marketplace.
In addition to the capabilities described in the rest of this post, Nucleus correlates enumeration results with vulnerability intelligence feeds that can help agencies identify vulnerabilities that have the best chance of landing on the CISA KEV list in the future. Approximately 0.5 percent of all vulnerabilities make it onto the CISA KEV, and approximately six percent of vulnerabilities have a 10 percent or greater chance of ever making it onto the list. Nucleus can identify and categorize those candidates automatically.
Implementing policy requirements in Nucleus rules is no harder than categorizing from raw scan results, and the bulk of the work takes place upfront. Rules are set once, and then fine-tuned over the course of time, making iterative improvements in the event of changes to the environment or the odd mis-categorization. Anytime due dates are adjusted, Nucleus will keep the adjustment in place and will not overwrite it.
For the most motivated, it is entirely possible to get Nucleus integrated with the asset inventory and vulnerability scanners to help meet the requirements of CISA BOD 23-01 and future CISA BODs in 30 to 45 days. For others, it may take a bit longer. However, once up and running, Nucleus will significantly strengthen and accelerate your ability to meet these and any future CISA requirements. We have helped our customers prioritize, assign, and remediate over 3.5 billion vulnerabilities collectively and we are purpose-built for scale.
Ready to get started on your CISA BOD 23-01 journey? Contact us today or click here to watch a Demo On-Demand.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.