Tracking Resolved Vulnerabilities in Nucleus
Why tracking the number of Resolved vs Active instances of a vulnerability is a huge win and what it means for your program.

Being able to quantify the number of vulnerabilities your remediation teams have fixed, and track the number of resolved vs still active instances of a vulnerability is a huge win, in several ways. Did you know that Nucleus is the only risk-based vulnerability management tool that gives you a list of the vulnerabilities that you have remediated or resolved in the past x number of days?
Let’s talk about how to leverage this information, newly available in Nucleus, to turbocharge your vulnerability management program.
Where to Find Resolved Vulnerabilities
In Nucleus, pull up the dashboard for any of your projects. At the top, you’ll see a vulnerability overview that tells you how many vulnerabilities you have in total, and also how many unique vulnerabilities you have. Reporting both is important, because the unique number will look more like what your system administrators probably see in their patching tools. The number still won’t be exact, but it will be closer.
Here’s how to use these numbers:
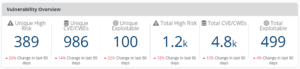
By deploying 389 updates, you can expect to fix about 1,200 high-risk vulnerabilities. Or if you want to try to clear the deck of CVEs, you can deploy 986 updates to fix 4,800. To get a list, just click on any of the numbers in the UI.
Here’s a pro tip when it comes to using that list, which builds on our advice of asking your patching teams to work dumber and lazier. When you see a vulnerability come up in that list and Nucleus says it’s partially mitigated, that’s a sign that there might be some caveman patching going on. When you click on a vulnerability that originated from a network-based scanner and click on Instances, take a good look at the status. If you see that somewhere between 70 and 90 percent of the instances are resolved and you’re not seeing any further improvement, then that’s the time to assess whether that vulnerability carries enough risk to be worth shifting to the brain surgeon approach to fix the rest.
But don’t stop there. Go back to the main dashboard and scroll to the bottom for some other key KPIs:
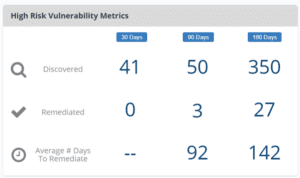
Clicking on any of those numbers brings up another dashboard telling you how many unique vulnerabilities you’ve discovered and remediated in that time period, broken down by severity, and the average number of days it’s taking for you to remediate them. You probably have SLAs defined in your vulnerability management policy; this number tells you at a glance if your teams are meeting them. And if you want a different time period, just select a different time period from the drop-down.
In a matter of seconds, you know if you have a functioning VM program. No other tool in the industry makes it this easy to find what your teams have fixed in the last few months, and that knowledge can help you in at least three ways.
Perceived Accuracy
In almost every vulnerability management health check I’ve performed or participated in over the years, data accuracy was the biggest complaint I heard. It’s always the first thing that system administrators call into question. As a former system administrator, I can tell you we don’t have a standard playbook we share with each other, but we think enough alike that we independently arrive at the same tactics.
I found that when I show them what vulnerabilities they’ve fixed, that tends to lessen their objections. When they see something on the list that no other human being knows they deployed, including where they deployed it and approximately when, it gets harder to argue that the vulnerability scanning tools are just making stuff up.
People are more likely to act on the data when they believe in it.
The Psychological Value of Positives vs Negatives
Many years ago, a psychology professor shared an insight with me that negatives weigh about seven times as much as positives. That’s why one backhanded comment can ruin your day even if you get four or five compliments the same day.
Vulnerabilities are by definition negative. And I’ve personally witnessed what happens when a director or a CISO gets up in front of a group of system administrators and tells them they have hundreds of thousands (or millions) of vulnerabilities and they’d better start fixing them. Nothing good happens from that. Generally what happens is they tune it out. It’s a defense mechanism.
If I wait until the number of closed vulnerabilities outnumber the open ones by a factor of 7, I may be waiting a while. Fortunately, I can drive remediation in the meantime by reporting on the risk score and recommending 10 vulnerabilities to fix first. But I find that once one team does reach that factor 7 tipping point, the perceived difficulty of fixing vulnerabilities plummets. And sometimes one team reaching that tipping point can help the others get there.
The HR Value of the Closed Vulnerability Count
In 2013, an IT manager asked me how many vulnerabilities his team had remediated in the past year. There was no easy way for me to get that information, but I was able to give him an estimate with reasonable confidence. He wanted it for annual reviews, so I did what I could to get him better numbers in 2014. And the 2014 number was rather impressive. It was also due largely to the efforts of one person. The number of fixed vulnerabilities I could attribute to him looked like a pinball score, and his manager and the CISO were able to use that pinball score to get him a promotion and a raise that year.
I can’t recall a time he ever questioned any of my recommendations after that.
How Helping Others Helps You
Never underestimate the power of momentum when it comes to enterprise vulnerability management. One of the reasons why vulnerability management is so hard is because you have to fight the momentum of vulnerabilities that have been accumulating in backlog for years.
Letting Nucleus tell you when to switch from one style of patching to the other helps you pivot easily to get that momentum going in the right direction. But you have to measure that success or you’ll lose that momentum in a month or less. Especially when the solution is counter-intuitive. But now Nucleus makes measuring the success easy.
The other reason why vulnerability management is hard is the job is all about getting other people to do something. When they see that what they’re doing is working, and it’s a neutral external third party that’s validating it, they’re much more likely to continue doing it. And that’s what makes you a successful vulnerability management professional.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.































