Vulnerability Management: Build vs. Buy

The Path to Vulnerability Management Maturity
We’ve talked at length about Fixing the Broken Vulnerability Management Process, establishing the problems and chaos that plague security teams trying to address an explosion of technology and vulnerabilities with a mature vulnerability management (VM) program.
As you continue down the path toward achieving VM maturity, you will undoubtedly find that manual VM workflows are bottlenecks preventing your program from scaling and moving quickly enough to meet your objectives. You might even consider building your own vulnerability management platform internally to automate some of these bottlenecks.
Stop right there!
Proprietary in-house software, or homegrown vulnerability management solutions, tend to be clunky and immature. They often consist of little more than a database and a primitive user interface. They‘re often difficult, time-consuming, and expensive to maintain, as well. Consider this. Any time developers spend maintaining the vulnerability management system is time they can’t spend on internal projects that drive the business forward.
In-house solutions seldom meet the needs of the organization, rarely scaling sufficiently to meet increasing demand. They also tend to be purpose-built by one dedicated team to solve one vulnerability management problem. However, multiple stakeholders are involved in the vulnerability management process. This creates a situation where the homegrown solution solves only one problem, to the detriment of the vulnerability management process across the larger enterprise.
There are many reasons enterprises choose to build their own vulnerability management solution. Some of these reasons include:
Blissful Ignorance
Building a vulnerability management solution in-house seemed like the only option available. You were unaware that vulnerability management platforms already exist to automate manual VM workflows.
Unicorn Complex
Your organization is one-of-a-kind! You believe that your vulnerability management objectives, use cases, and workflows are too unique for an off-the-shelf VM platform to satisfy.
Pinching Pennies
You have your own software developers on staff. They’re more than capable of building a vulnerability management solution without spending more dollars on an external vendor, right?
Understanding the Value of a Vulnerability Management Solution
These reasons may seem sound, but they aren’t accurate. Here are some insights that can help as you move toward vulnerability management maturity without making the mistake of trying to “go at it alone.”
Insight #1: Terminology Matters
The primary reason that vulnerability management platforms like Nucleus are still foreign to many cybersecurity professionals is that the term “vulnerability management” was adopted by scanning vendors over 20 years ago. Even today, when most people think of vulnerability management, the first thing that comes to mind is vulnerability scanning, which is just one step (Vulnerability Discovery) in the larger vulnerability management process.
The Five Elements of a Mature VM Program
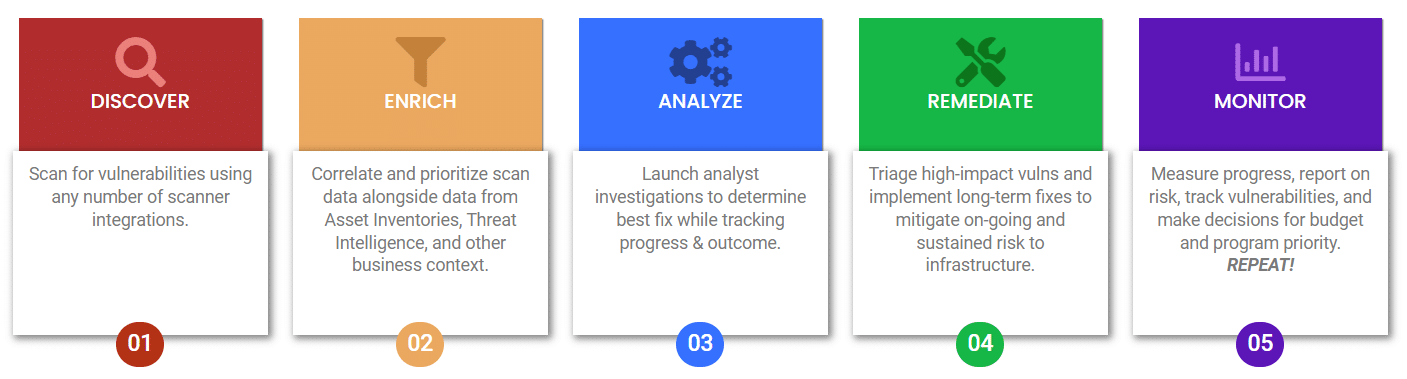
Unfortunately, many search engine results for “vulnerability management” still do not return results for platforms designed to automate the larger VM process. Making matters worse, the analyst community cannot agree on a good term for this space, so we’re stuck with categories like “Vulnerability and Risk Management” (VRM), “Risk Based Vulnerability Management” (RBVM), “Application Vulnerability Correlation” (AVC), or one of several other terms that are nearly impossible to differentiate from one another.
Insight #2: You’re Not (Very) Unique
Insight #3: Learn from Others’ Mistakes
If you are part of a large organization, you may have internal software developers with extra capacity to support a new project to develop an internal VM capability. Many companies try this, and the vast majority eventually fail. The reason is that most companies underestimate the level of effort required to build and indefinitely maintain their own VM platform internally. An enterprise–class vulnerability management platform will cost millions of dollars to develop over the course of many years, will absorb the time of many senior security engineers, software developers, and project managers, and will come with a never ending (and ever-growing) maintenance tail.
Are there cases where it makes sense to build a platform vs. buying one? Sure, we’ve seen exceptions, but they are few and far between. You may have a very limited set of use cases that don’t justify the cost of a VM platform designed to solve many larger problems. In these cases, we would suggest developing the minimum set of tools/utilities you need to get by as a stopgap, keeping close tabs on this rapidly evolving space. More than likely, if you cannot find the right vendor solution today, it will be available soon.
Critical Features of an Effective VM Workflow Tool
Nucleus Streamlines Enterprise Vulnerability Management
Nucleus automates vulnerability management processes, enabling organizations to mitigate vulnerabilities 10 times faster, using a fraction of the resources that it takes to perform these tasks today.
Nucleus Security’s vulnerability and exposure management platform integrates with your existing tools, providing a single pane of glass to monitor your security posture and manage your vulnerability data. Integrating with over 150 scanners and external tools, Nucleus ingests your entire scope of vulnerability data, consolidates it in one place, and automates your vulnerability management processes so that your team works more effectively while preventing critical findings from falling through the cracks.
Nucleus delivers value right out of the box, allowing you to manage vulnerabilities at scale through a simple, three-stage process:
- Collect and Normalize. Nucleus ingests and normalizes all the vulnerability data in your enterprise, including your tools, penetration tests, and audits, allowing security personnel to analyze, track, and search from a single console.
- Prioritize, Deduplicate, and Enrich. Nucleus enables organizations to produce custom risk scoring algorithms based on risk tolerance and priorities, resulting in risk scoring that is contextual to each organization, a significant reduction in time to determine the true risk of each vulnerability, along with more accurate reporting.
- Automate Response and Remediation. Using bi-directional integrations with ticketing systems, issue trackers, incident response tools, SIEMs, and more; as well as flexible automation rules, and real-time views of all active vulnerabilities and remediation statuses, Nucleus enables organizations to respond to vulnerabilities rapidly and at scale.
Over 150 Integrations and Counting
Nucleus currently integrates with 150+ vulnerability and security tools and is continuously adding more based on customer requests. We also maintain an open GitHub project for customer contributions and our proprietary FlexConnect integration framework to respond rapidly to new integration requirements.
Support for SSO and Custom Roles
Nucleus integrates with your single sign-on provider so that you can map your existing roles to Nucleus roles, minimizing administrative overhead.
Enterprise Speed and Scalability
Nucleus scales to support any sized organization and remains performant regardless of the number of tools in use, concurrent users, or amount of vulnerability data imported.
Scheduled Reporting
Built-in reports for all levels of stakeholders, from executive to technician, can be automatically emailed at any scheduled interval.
Accurate Vulnerability Status
It is critical that security personnel track every change to vulnerability status, not just discovery and remediation. Nucleus supports over 10 different vulnerability statuses, ranging from false-positive to risk-accepted, and documents each step along the way to produce a complete and detailed history of each vulnerability, from discovery to remediation.































