Press Release: Nucleus Security Releases Free CISA KEV Enrichment Dashboard

Nucleus Security Releases Free CISA KEV Enrichment Dashboard and Research, Providing Further Insight Into Vulnerability Prioritization
One year after CISA released the Known Exploited Vulnerabilities catalog, Nucleus Security’s new Enrichment Dashboard offers vulnerability researchers deeper context and insight into each release.
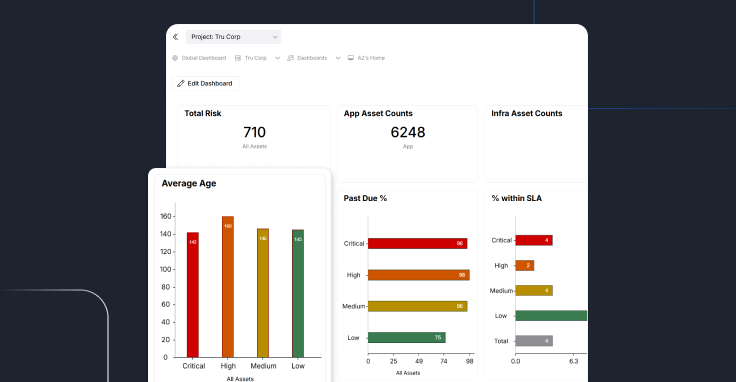
SARASOTA, Fla.–(BUSINESS WIRE)–Nucleus Security, a leader in risk-based vulnerability management and process automation, today launched the CISA KEV Enrichment Dashboard, a free tool that enables vulnerability researchers to quickly observe known and exploitable vulnerabilities identified by CISA and layer additional enrichment intelligence onto their vulnerability prioritization. The CISA KEV Vulnerability Enrichment Dashboard provides a complete list of the CISA Known Exploitable Vulnerabilities (KEV) Catalog, which is then enriched with CVSS, EPSS and GreyNoise Threat Intelligence.
“The CISA KEV is one of the best free sources of vulnerability intelligence available today, but the data is limited to just a few informational fields and doesn’t provide any context regarding the observed exploitation activity.” – Stephen Carter, Co-Founder and CEO of Nucleus Security.
There are approximately 198,000 known critical vulnerabilities and exposures (CVE), of which only a small subset are confirmed as actively being exploited. The CISA KEV catalog names less than .5% of all identified CVEs – drawing attention to those that are the most risky and confirmed as being active or exploited. The CISA KEV list itself also exposes some of the primary weaknesses in CVSS scoring, which many organizations use to decide and prioritize which vulnerabilities to patch by using a CVSS score of 7 or higher to determine which vulnerabilities to remediate. However, 12% of vulnerabilities that are confirmed as exploited by CISA have a CVSS score below 7.0.
The above data demonstrates that organizations that prioritize remediation solely based on CVSS are leaving themselves open to vulnerabilities that have been, or are actively being, exploited in the wild. The Nucleus Security CISA KEV Enrichment Dashboard aims to close these gaps by providing more context and guidance to vulnerability researchers. Through their research, and the development of the CISA KEV Enrichment Dashboard, Nucleus Security has made the following observations as of October 2022:
Most Exploited Vendors
- The top five most exploited vendors on the CISA KEV list include Microsoft, Adobe, Cisco, Apple and Google, making up more than 53% of all vendors included.
- Certain brands, like Apple, carry a perception that just buying and using them will keep you secure. However, as we see from the CISA KEV list, you also must keep them up to date.
Most Exploited Software
- The top five most exploited products on the CISA KEV list include Microsoft Windows, Adobe Flash Player, Microsoft Internet Explorer, Microsoft Office, and Google Chrome.
- Avoiding Microsoft Windows, Microsoft Office, and Google Chrome isn’t practical for most organizations, and it is important to note that the alternatives to Windows and Chrome, at the very least, are also on this list.
Exploitation Activity is Validated by GreyNoise
- Over a 90-day period, GreyNoise detected 145 unique CISA KEV Catalog vulnerabilities that had scanning and exploitation attempts in the wild.
- Threat intelligence like this provides further validation in the value of using multiple threat feeds for discovering exploitation which should be used to prioritize vulnerability remediation.
High EPSS Scores as Predictive Indicators of Potential CISA KEV Candidates
- When looking at Nucleus’s CISA KEV Enrichment Dashboard, 33% of CISA KEV vulnerabilities have an EPSS score higher than .5, or a 50% probability of being exploited in the next 30 days. However, when looking at EPSS scoring distribution across NVD, only 1.4% of all vulnerabilities have a score of .5 or higher.
- EPSS is likely a good predictive indicator of what vulnerabilities could be future candidates for landing on the CISA KEV list.
End of Life Products
- Two of the most common products often featured on the CISA KEV list are “end of life”: Adobe Flash and Internet Explorer.
- It is often difficult for organizations to eradicate tools like Internet Explorer because legacy software dependencies on internet explorer are still relatively common on corporate intranets. Keeping Internet Explorer up to date and putting rules in your web proxy to keep Internet Explorer off the public internet is prudent.
“The CISA KEV is one of the best free sources of vulnerability intelligence available today, but the data is limited to just a few informational fields and doesn’t provide any context regarding the observed exploitation activity,” said Stephen Carter, Co-Founder and CEO of Nucleus Security. “We needed a way to quickly analyze and further prioritize the hundreds of vulnerabilities in the KEV, and we did that by enriching it with other sources of vulnerability intelligence. It was immediately clear that we had a case where the whole is greater than the sum of its parts, and we wanted to make this available to the community.”
The Nucleus CISA KEV Enrichment Dashboard, available to anyone, allows vulnerability enrichment data to be easily sorted, searched, and exported. To learn more about CISA KEV and how to use the Enrichment Dashboard for vulnerability prioritization, check out Nucleus Security’s Guide to CISA KEV. You can also check out more observations and insights from the Nucleus Security research team in this recent post, Top CISA KEV Observations.
About Nucleus Security
Nucleus Security is a Risk-Based Vulnerability Management (RBVM) solution that automates time-consuming vulnerability management processes, enabling large and complex enterprises to scale their vulnerability management program and remediate vulnerabilities 10x faster. Supporting nearly 100 integrations, Nucleus Security creates a unified vulnerability inventory, fully enriched with the world’s leading threat intelligence, and provides the automation engine needed to eliminate the stovepipes of chaos found in large enterprise vulnerability management programs today. Harness the power of a unified vulnerability solution today at https://nucleussec.com/.
Contacts
Media
Taylor Hadley
LaunchTech Communications
(978) 877-2113
[email protected]
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.