Discovering the Source of Vulnerability Management Chaos
Part 3 of a multi-part series in controlling the chaos of vulnerability management.
Are you in Vulnerability Scanner Data Hell?
The third of a multi-part series on controlling the chaos of vulnerability management. Read Part 1 and Part 2.
Imagine yourself back in grade school science class. Depending on your memory or how well you paid attention (slacker!), you might recall the second law of thermodynamics. It says that entropy (i.e., disorder or chaos) of systems always increases.
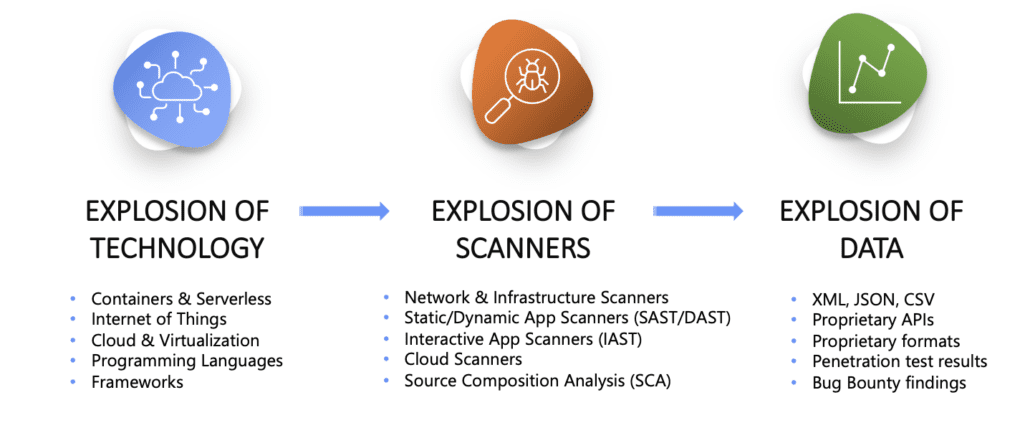
This is a great way to think of the challenges faced by many organizations in maturing a vulnerability management (VM) program. Chaos is the enemy of a well-structured and successful program. A chief source of chaos is too much scan data without a way to manage it effectively. To illustrate this point, we will start at stage one of the VM process, Discover.
In the Discover stage, scan data is often coming in from a disparate collection of scanning tools. Network, DAST, SAST, SCA, IAST, etc. Not to mention vulnerability data coming in from other means of discovery including cloud, compliance, pen testing, bug bounties, and disclosures. The sheer volume of sources and scan and vulnerability data in a large enterprise can be HUGE and overwhelming for teams to deal with.
Absent a way to aggregate and correlate the massive and ever-increasing volume of data, the chaos of your vulnerability management program is guaranteed to increase. (No fun for anyone!). To combat the chaos, some resource-starved security teams make do with primitive tools like spreadsheets, emails, and PDFs. Anyone who has ever used this approach knows it is like occupying a special rung of hell.
Better resourced security teams might succeed at stitching together a Frankenstein Funnel or pipeline for vulnerabilities comprised of half a dozen or more tools. It might take in raw scan data, normalize, and prioritize it. But it does all this without a lot of efficiency and often at a higher than necessary cost.
The enriched data is then distributed around the organization to the parties concerned, leaving it to them to deal with it. Making the security team in charge of vulnerabilities very unpopular! While this is a step in the direction of having a mature vulnerability management program, it is far from what a truly contemporary and scalable program can look like.
In most cases a sophisticated vulnerability aggregation and response automation tool can replace some of the pieces in a Frankenstein Funnel, streamlining and leveling up the program and resulting in significant savings for the organization. For the less mature programs still using spreadsheets, this type of tool can transform a VM program from immature to mature in very short order.
The problem is, this category of tool is relatively new and often either is unknown or gets confused with scanning, SIEM, or SOAR platforms. But now you know. And knowledge is power, but only with understanding. If you want to gain an understanding of how a vulnerability aggregation and automated response tool can transform your VM program, consider taking the Nucleus Demo on Demand available on your own terms and timing. Or, if you are not ready for that level of commitment, download our datasheet.
PART 1: SCANNING AIN’T PLANNING. Why you need more than just tools to manage vulnerabilities — Read Now.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.
































