Our Top 5 Takeaways from Black Hat 2022
A couple of weeks ago, the Nucleus team headed off to Las Vegas for the first in-person Black Hat USA conference in a couple of years. Not only was it great to reconnect in person with colleagues, customers, and industry friends, but there was also an infectious buzz throughout the air that had nothing to do with the infamous parties or lights of Las Vegas.
Still buzzing from #BlackHat2022! 🌀🥷 It was so great to reconnect with all of our #cybersecurity friends and colleagues last week — and a big thanks to everyone who stopped by our booth, attended one of our sessions, or caught up with us in Vegas! #BHUSA2022 #hackersummercamp pic.twitter.com/FcE7Suwbu8
— Nucleus Security (@nucleussec) August 16, 2022
This year at Black Hat 2022, it was no different. Here are five industry trends and key takeaways that we are still thinking about from this year’s conference:
1. Industry growth is not slowing down anytime soon
There were over 300 exhibitors in this year’s Black Hat business hall, including a space occupied by our own Nucleus team inside “Innovation City.”
Among both new and seasoned exhibitors alike, one of the biggest areas of focus was the assessment and detection of assets and threats or recent acquisitions. “Recent calls for security collaboration have meant vendors are no longer shying away from keeping data for themselves and are exposing APIs for the benefit of the security community,” reported Forrester in a recap of the event. “Startups are using these APIs to ingest whatever data they can and provide their own proprietary risk scoring and prioritization. Expect more vendor entrants into this asset/threat prioritization and prediction space, some of which will eventually get bought by larger vendors.”
2. Cyber security needs to continue to focus on the right things… but even faster
While the increase in innovation and industry growth is encouraging, there was also a consistent reminder within this year’s sessions to not lose sight of the problems still to be solved. Chris Krebs, former CISA director and keynote speaker at Black Hat, cautioned that he would not count us any more secure than we were in the 25 years since the first Black Hat event.
“The unthinkable complexity of cyberspace… that’s where we’re at right now,” Krebs said during his keynote address. “Things are getting more complex, we’re generating more data, and we have a maturing industry that’s solving core infrastructure problems. Just not at the pace that we want it to.”
Chris Eng, CRO at Veracode, echoed these statements in the final briefing of the event. “We’re seeing a lot of the same security trends year after year, we just need to be quicker at adapting. We already know what things to do in large part. They’re just not getting done fast enough. It can feel discouraging, and we are seeing things get better in pockets (integrating security in DevSecOps, for example), it just happens slowly.”
3. Buzzword Bingo is hotter than ever
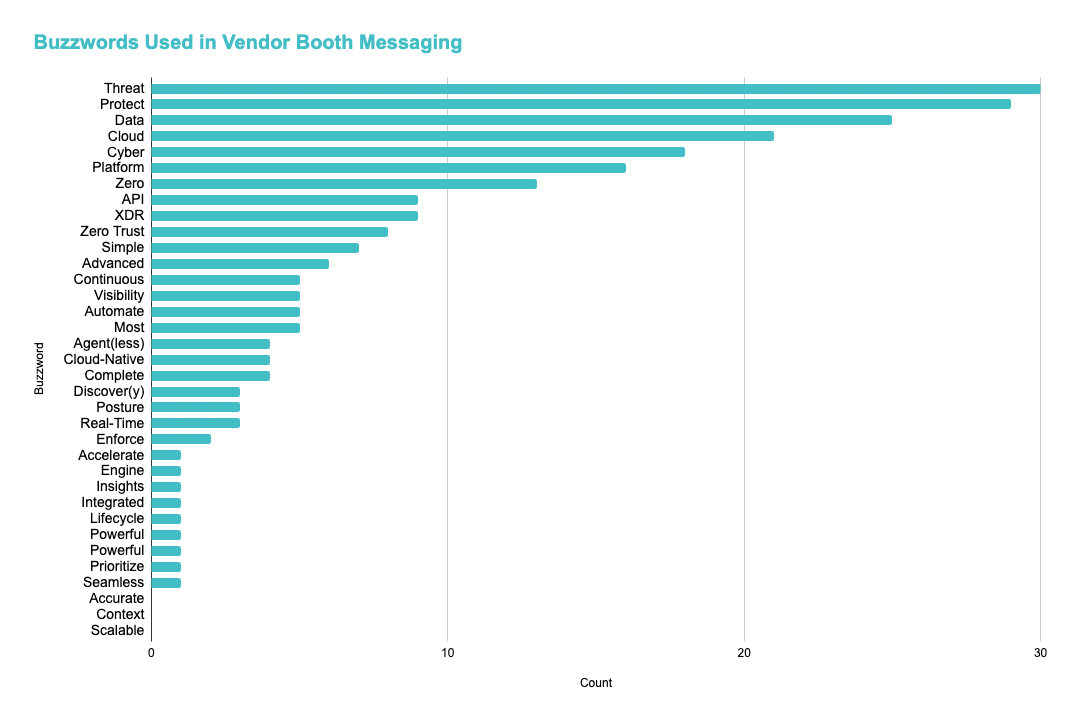
As the number of security vendors increases, so do the industry buzzwords. One of our favorite recaps of Black Hat 2022 was an analysis of the most common Black Hat buzzwords by Dani Woolf at Audience 1st.
The most common buzzwordy terms featured in the booths and marketing of this year’s vendors included phrases we’ve all seen time and time again, such as “Threat”, “Protect,” “Data,” “Cloud” and “Zero.” However, the author’s problem was not so much with the buzzy phrases themselves, but the redundancy and false promises that often follow these taglines.
“Come at me with XDR, come at me with SOAR, come at me with cyber resilience. That’s fine. I get it. But then give me, you know, the meat and potatoes behind it. What it really means. I think vendors just have to change the way they lead with buzzwords.” – said Leo Cruz, CISO at St. Joseph’s School for the Deaf
For our industry to move at the fast and efficient pace that many thought leaders are challenging us to, it’s important that we all begin leading with genuine messaging that is backed up with data. We here at Nucleus have always made it a priority to make sure the capabilities and results of our tools and solution tie back to the promises we make in our messaging – and we will continue to do so as we grow over time.
4. The world needs to start putting increased value on secure products
Another essential component to increasing speed in the cyber security industry and making more effective changes will require that industries and individuals as a whole begin putting increased value on secure products.
In his opening keynote session, Chris Krebs quoted Daniel Miessler who once said, “software remains vulnerable because the benefits of insecure products far outweigh the other side.” Too often security is viewed as the thing that slows down the greater eco system, and it’s up to us within the cyber security community to move that needle.
“We don’t have a system that changes the balance of the value of secure products,” Krebs said. “Big Tech companies came to the White House to make promises and show support, but we have to accelerate that process.”
5. Prioritization should include increased focus on exploitability
Here at Nucleus, we talk about the importance of prioritized risk based on your business context a lot. After all, not all bugs or vulnerabilities are created equal. And, just as importantly, if all vulnerabilities are prioritized as critical, then no vulnerabilities are critical.
One of our favorite briefings at Black Hat 2022, “Calculating Risk in the Era of Obscurity: Reading Between the Lines of Security Advisories,” highlighted this line of thinking in their session. “We all know that applying patches is one of the best things you can do to protect your enterprise and reduce the risk of security breaches,” said the speakers from Zero Day Initiative. “But ‘just patch it’ isn’t always feasible. You must prioritize based on risk, and inaccurate info or faulty patches increase cost and risk for companies. If you’re only deploying critical bugs first, which do you start with?”
If you’re only deploying critical bugs first, which do you start with?
“CVEs don’t look at exploitability or whether a risk is likely to be used in the wild. They also don’t tell you whether a bug is critical to your enterprise.” #blackhat2022 pic.twitter.com/05HTtrKzqz
— Nucleus Security (@nucleussec) August 11, 2022
Want to see for yourself how Nucleus does this? Check out this on demand demo of our platform.
What do you think about these five thoughts from Black Hat? And what was your biggest takeaway from this year’s conference? Reach out on LinkedIn or Twitter and let us know!
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.