Nucleus Product Update 3.2
It’s March Madness @ Nucleus: New features, filters, finding criteria, and a sneak peek…
Welcome to the Nucleus Product Update 3.2. We’re marching right along, adding more value to our platform and services. It’s no secret this month is jam-packed with goodness – March Madness, St. Paddy’s, Women’s History, the first day of spring – March at Nucleus is no different.

This month we’re highlighting several newly released product features, meant to accelerate and elevate the things you’re able to do on our platform, including:
- A new status expirations feature for flexible and reliable review cycles
- New assignee and assigned team automation rule finding criteria
- Powerful new trends page filters for improved reporting and tracking
- Connector enhancements, including a major GitHub Repo improvement
And since it’s the month of the lucky, it’s your lucky day! We’re also including a sneak peek into a new feature coming soon, Asset Group Access Control (AGAC).
Check out all the details for these updates below.
Have questions or want to know more about anything you see here? Our team is happy to help. Just reach out to our crew at [email protected] for further assistance. Happy reading!
An all-new status expiration feature to temporarily change a finding status
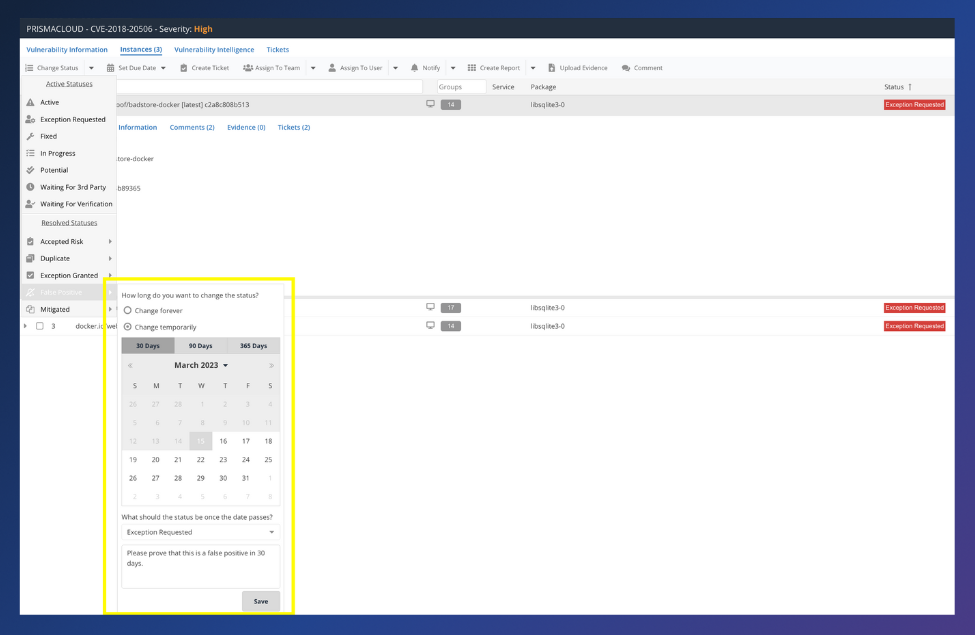
Released 2023, status expirations allow you to temporarily set a vulnerability finding to any resolved status for a specified period. You can read all about this new feature in this blog post. As mentioned in this post, when you cannot remediate a finding simply by deploying an update during the next maintenance window, you can now use Nucleus to track everything you can/can’t do and why, everything you did, attach all relevant evidence, mark the vulnerability under the appropriate status, and give it an expiration date. Once that expiration date passes, the status reverts back to an active state. Status expirations are available as a manual action, bulk edit, and in Finding Processing automation in Nucleus.
Status expirations are helpful in several situations, including when a risk acceptance requires annual re-evaluation or when recommended mitigations on a zero-day vulnerability need another review later to apply a future update. You won’t find automation-supported and context-rich status expirations in most of today’s vulnerability management tools and homegrown solutions, so we’re ecstatic about this one and hope you are too!
Learn more in this blog post and our Status Expiration How-To Guide.
New assignee and assigned team automation rule finding criteria
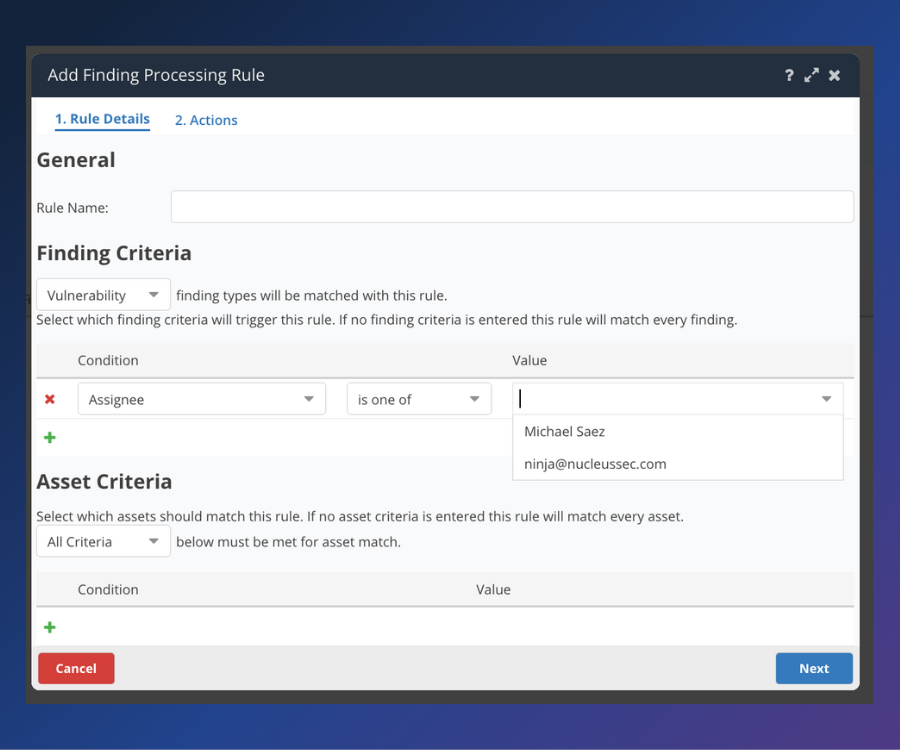
For each automation rule in Nucleus, you can choose Finding Criteria and/or Asset Criteria to trigger your rules. A field that wasn’t available before was a Finding Criteria condition based on who was assigned, either individual or team. This new feature is now available as part of our ticketing, finding processing, and notification rules. This assignee and assigned team automation rule finding criteria is especially powerful with ticketing rules, making it easier than ever to integrate Nucleus into your teams’ existing workflows. We continually aim to supercharge the full cycle of vulnerability management for you, and this new feature gets us one step closer.
Trends page filters for improved reporting and tracking

We already had asset filters on the Trends Page in Nucleus. You could choose a few different asset properties to filter by, but assets were only one side of the coin. Now, you can go into the Trends Page and filter vulnerability data as well. The vulnerability data can be filtered using severity, discovered date, source, exploit available and name. For example: Do you want to know how your teams are performing on critical, exploitable vulnerabilities discovered last week? It’s now easier than ever to find out. These filters can also apply to reports, which can be downloaded, to ensure you can easily use this information to measure and track your progress. This was a much-anticipated release and can be a helpful tool for monitoring and reporting on the health of your vulnerability management program.
More reliability and accuracy with GitHub Repos

When a repo is deleted in Github, Github sends a webhook. Previously, we didn’t ingest that webhook info from Github. Now, when you delete a repo in Github, we ingest that info and reflect it in your vulnerability data in Nucleus. This ensures that you aren’t reporting on data that is no longer relevant due to it being tied to a repo that no longer exists. We know having data that you can trust is important and this feature allows you to have that extra layer of assurance with your Github data in Nucleus.
Upcoming release spotlight: Asset Group Access Control (AGAC)
Yep. We’re doing it. Telling you about something before it’s here! That’s a first and we like it.
Coming in the next weeks, Asset Group Access Control (AGAC) is being added on top of our already existing role-based access control (RBAC). This new capability allows administrators to assign specific asset groups to users. In other words, you will now have the ability to restrict user access to only specific asset and vulnerability data within projects where needed. For enterprises with lots of vulnerability data and people managing it especially, AGAC is a powerful tool to ensure only the people who need to see specific vulnerability data within a project have access to it, while others don’t.
We’re also introducing a new role type, asset group restricted user, and as well as an update to the way we handle asset grouping. This will allow us to keep your asset groups up-to-date dynamically based on the definitions of automation rules that populate those asset groups. When all brought together, these updates fulfill a critical need for our customers to be able to safeguard access to their sensitive data and to streamline the experience of their mitigation teams, allowing them to focus on what matters most: remediating important vulnerabilities.
We’re very excited about all of these new features. Stay tuned for more coming soon!
Other happenings: Nucleus Webinar Series
Over recent months, the Nucleus team has sponsored several high-quality webinars featuring our founders and strategic partners. Our latest, Taking a Risk-Based Approach to Assessing Your Attack Surface, is happening on March 22 at 2 pm EST. Registration is open. Our last, Maximizing Vulnerability Remediation Efforts Through the Power of Threat Intelligence, took place last month and is available on-demand now.
Click here to expand our full Release Notes
You can access the Nucleus change log to view the complete, unedited version of release updates posted each week. Select the subscribe to the RSS feed option on this page if you would like to receive weekly change log updates. This new Nucleus Product Update is intended to fully summarize and outline those weekly changes for you, with more details, each month. The product updates include all the following features and improvements:
New Features
- Added the ability to include an expiration when changing the status of a vulnerability to one of the resolved statuses. Select which active state the vulnerability will revert to and add an optional comment as well. Available as a manual action, bulk edit, and in Finding Processing automation.
- Added functionality in asset processing automation so that asset groups are updated dynamically based on dynamic field values.
Product Improvements (Performance, Experience, & Functionality)
- Added assignee and assigned team as criteria in various areas throughout automation: ticketing and issue tracking, notifications, Finding Processing.
- Added additional filtering on the Trends page for: finding discovered date, exploitable vulnerabilities, finding name search, source, finding severity, finding status
- Added additional NOT operators to Trends page filtering by Source and Name.
- Improved the way we store and update asset ports.
Reporting Improvements
- Updated the Vuln Details XLSX report generator to include data from child asset groups as well as parent asset groups. Select between including ANY, or ALL assets within selected asset groups when generating this report type.
Integration Improvements
AlienVault:
- Made a few updates to AlienVault ingestion
- Support their new file header change
- Use Vulnerability_ID as the finding name in Nucleus
Crowdstrike:
- Updated the Crowdstrike connector so that we are pulling from their new v2 devices endpoint.
Dependabot:
- Updated Dependabot connector to use new GraphQL properties to indicate if a repo doesn’t have Dependabot alerts enabled when trying to ingest it into Nucleus.
Github:
- Improved the Github connector so that assets from deleted Github repos are de-activated in Nucleus.
Invicti/Netsparker:
- Sped up Netsparker scan downloads.
Prisma Cloud:
- Added retries in certain scenarios for Prisma ingestion and removed partial scan ingestion.
Qualys:
- Enhanced speed of the Qualys connector by splitting download and processing scans into separate jobs.
Sonatype:
- Improved Sonatype Nexus IQ when importing by org so that if an application has no scans in it, we don’t unnecessarily refresh scans.
Bug Fixes
- Fixed an issue by updating ticket experience to more accurately reflect ticket update times in tool tip pop overs in the tickets page.
- Fixed an issue where manually uploading scan files resulted in certain findings not mitigating as expected in limited scenarios.
- Fixed an issue where host metadata was only ingesting for active findings in Crowdstrike.
- Fixed an issue by updating Asset Removal automation to use “source” instead of “connector” as a condition.
- Fixed an issue where certain AWS regions were not populated when creating an Asset Inventory Sync rule.
- Fixed an issue by implementing more robust retries for Tenable.IO scheduled ingests.
- Fixed an issue where the assignees drop down field in the Jira Connector was limited to 100 assignees. The issue has been resolved for all Jira connectors with a successful connection to Nucleus.
- Fixed an issue where filtering by teams on the remediated page was not filtering as expected.
- Fixed an issue on the Compliance > Active Findings page where filters were not completely visible when added.
- Fixed an issue with Tenable WAS where we were adding new connectors in Nucleus upon refresh in certain scenarios.
- Fixed an issue by adding a retry when we don’t get a response back from Snyk.
- Fixed an issue where vulnerabilities with certain characters were displayed with visible HTML.
- Fixed an issue where CVSS score was inconsistent between views in the platform in certain scenarios.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.