Nucleus Product Update 2.10

More speed, connector improvements, security controls and trust
Welcome to Nucleus Security’s October 2022 product update! Our crew has been hard at work over the last month applying significant performance, reporting, and connector improvements to the Nucleus vulnerability management platform. Implementing several changes that help you better trust the data in Nucleus, our crew focused on the speed of data ingests being closer to real time and analytic workload processing at faster speeds so that data is always useful. This month’s product update includes:
- Faster load, ingest, and processing speeds
- Improved trends page data and reporting
- More security controls
- Metadata additions for Snyk and Attack Forge, plus S3 improvements
Check out all the details for these updates below.
Have questions or want to know more about anything you see here? Our team is happy to help. Just reach out to our crew at [email protected] for further assistance. Happy reading!
Faster load times and processing speeds
This release includes several improvements to Nucleus, including dramatic improvements to several page load times and the overall performance of our platform. By focusing on finding or implementing new ways to do things faster and more efficiently within Nucleus, we cut the active vulnerabilities page load time from 1 minute down to 2 seconds for 15 million vulnerabilities, and decreased the vulnerabilities details page load time from 2 minutes to 3 seconds.
We also introduced a few new enhancements “under our hood” geared towards speed and resiliency. These improvements include rearchitecting the way we track a finding’s entire history to better support data resiliency and speed of data ingest at massive scale (i.e., environments with millions of vulnerabilities). When it came to background tasks for re-activating assets during scan ingests, we improved the speed and efficiency there, as well. We’ve also significantly reduced processing times to add comments on all instances of a vulnerability with a changed severity across large data sets.
Improved trends page data and reporting
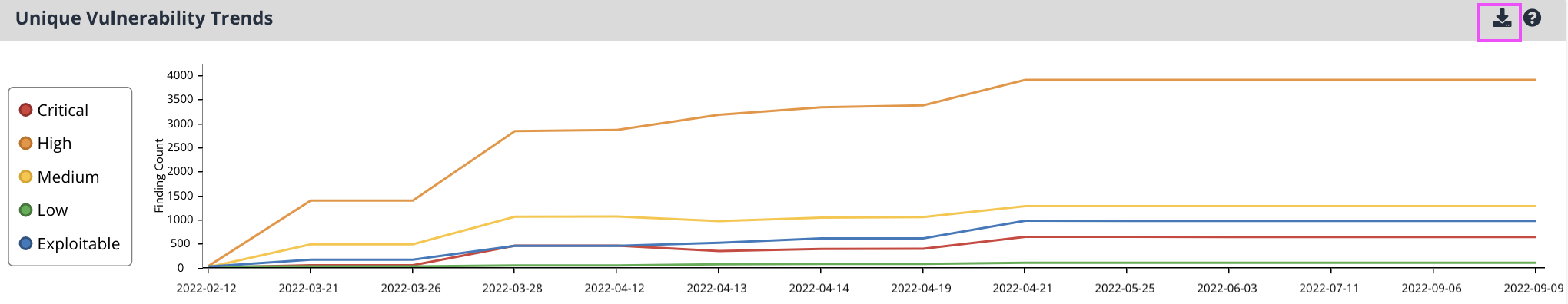
With this update, Nucleus users can now export raw chart data on the trends page. This enhancement allows you to quickly and directly access the data that populates many of the charts on the trends page, giving you the freedom and flexibility to correlate and utilize the data wherever and however you see fit.
Additionally, you can now filter trend reports based on filters you have applied in the UI. By incorporating your applied UI filters on any user generated reports, you immediately improve clarity and alignment between the information you are viewing both on and off our platform. It also ensures you can review the data you want more quickly and efficiently, with output reflecting your filtering settings in Nucleus.
Metadata additions for Snyk and Attack Forge, plus S3 improvements
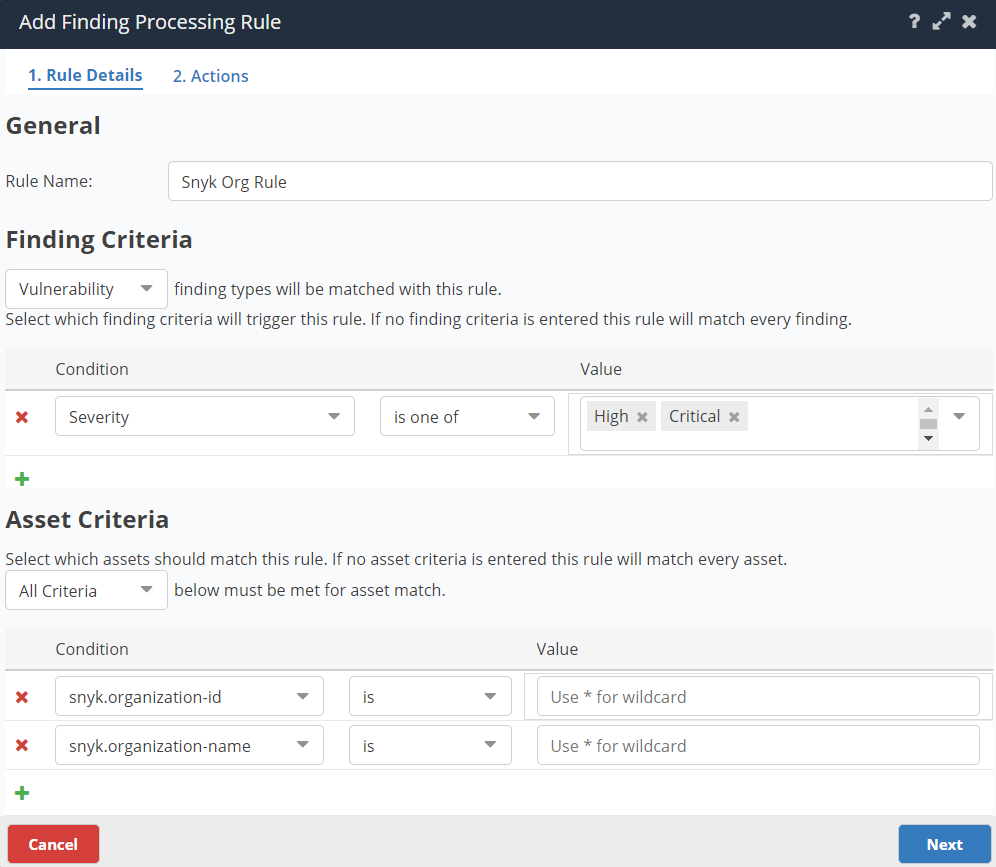
We have added the Snyk org ID and name as metadata in Nucleus in this latest product update. This additional metadata can now be applied to workflow automations, giving you more options for eliminating tedious manual work. We have also added 5 additional pieces of asset metadata, plus remediation notes and related info for Attack Forge. In addition to the new metadata, we have also made things faster and more efficient with this connector. We have improved logic to auto-resolve vulnerabilities between subsequent scan ingests from Attack Forge, while also adding multiple fields to finding references, such as likelihood of exploitation and custom tags.
We have also adjusted the S3 file size output so that S3 files can be ingested into third-party reporting tools more easily. You can now get your data seamlessly from S3 into third-party reporting tools, such as Snowflake. This improvement helps us further ensure you get the data you need when (and where) you need it.
More security controls
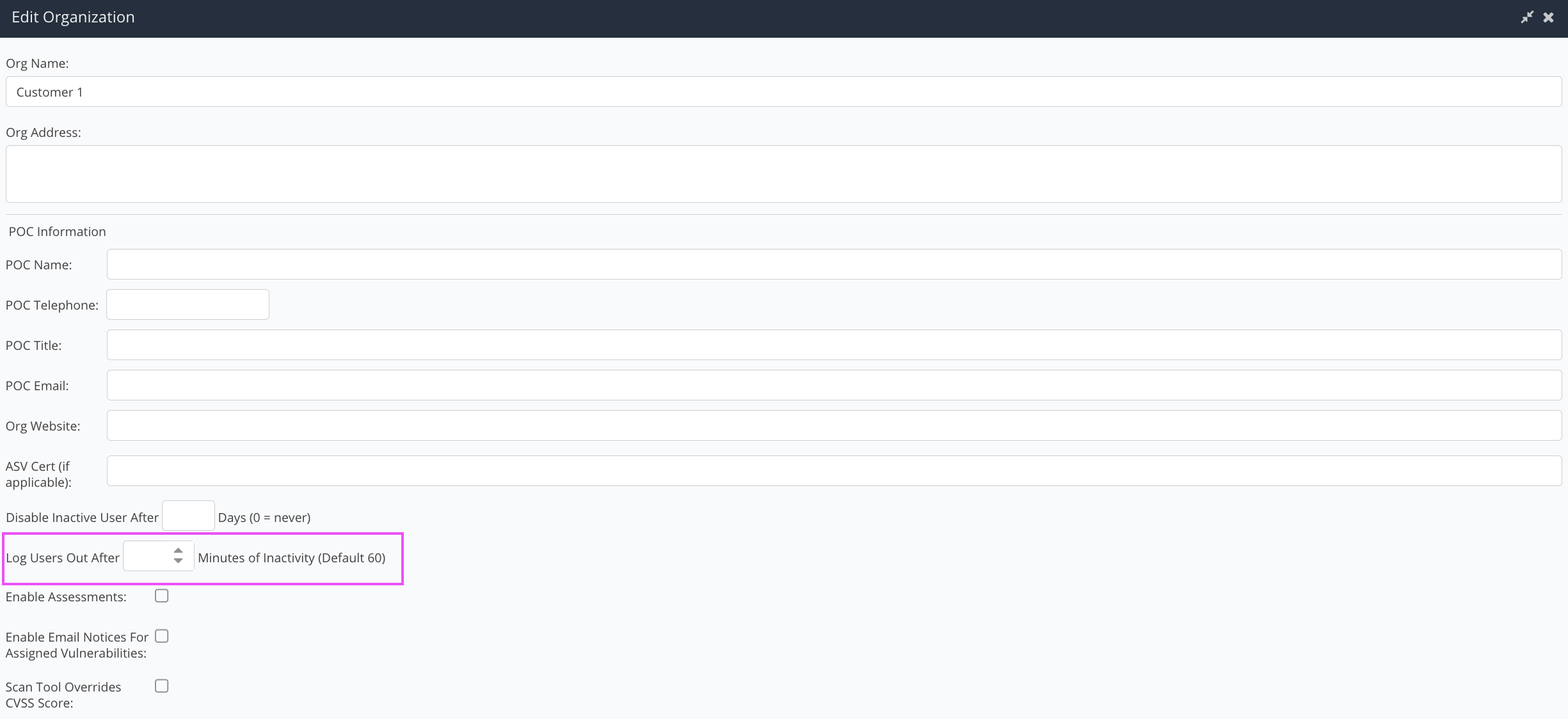
To better protect and secure our Nucleus customers, users are now automatically logged out after 60 minutes of inactivity. We have also added an option to customize this time based on your organizational preferences. Aside from the obvious security enhancements this new addition provides you, it also gives your admins another way to further customize Nucleus based on your unique needs. Set at the org level, this inactivity timeout setting adheres to all projects and users bound to your org within our platform.
You can access the Nucleus change log to view the complete, unedited version of release updates posted each week. Select the subscribe to the RSS feed option on this page if you would like to receive weekly change log updates. This new Nucleus Product Update is intended to fully summarize and outline those weekly changes for you, with more details, each month.
Click here to expand our full Release Notes
The product updates include all the following features and improvements:
Product Improvements (Performance, Experience, & Functionality)
- Added better error handling to compliance ingests to support cases with inconsistent framework metadata which caused framework mapping to be blank in certain scenarios.
- Updated Sonatype to better support scans with no vulnerabilities being marked as duplicates in Nucleus.
- Removed an intrusive pop up on the trends page.
- Drastically reduced processing time to add comments on all instances of a vulnerability with a changed severity during bulk actions of a thousand or more unique vulnerabilities with millions of instances.
- Improved the speed and efficiency of the background task for re-activating assets during scan ingest.
- Better handling of evidence uploads and deletion of evidence from single instances when same evidence was previously uploaded to multiple instances simultaneously.
- Added option to use finding discovered date (instead of the assessment merge date) when merging an assessment into a Nucleus project.
- Updated filter logic in the Active Vulnerabilities page that combined filter options which cause the vulnerabilities to be blank in certain situations.
- Improved loading time for vulnerability details page.
- Improved time of Asset Processing rule workflow that runs after an asset sync.
- Updated the endpoint for getting all ticketing rules by adding paging limits to address timeouts.
- Increased speed of API calls that use threat intel.
- Improved parsing of the Nucleus custom file schema (JSON) so that if a host is repeated, there is no impact to processing times.
Reporting Improvements
- Added ability to filter trends report based on filters which are applied in the UI.
- Updated logic for now including pinned vulnerabilities into the Vulnerability Details excel report.
- Added ability to download chart data in csv format for every x-axis value on the trends report page.
Integration Improvements
AttackForge (AF)
- 5 additional pieces of asset metadata from AF added to additional metadata Nucleus.
- Remediation notes from AF added as comments in Nucleus.
- Remediation dates and statuses from AF are now ingested into Nucleus as resolved vulnerabilities with all associated remediation data.
- Added multiple fields to finding references, such as likelihood of exploitation and custom tags.
- Improved logic to auto-resolve vulnerabilities between subsequent scan ingests from AF.
- Added evidence files from AF as evidence in Nucleus findings.
Crowdstrike
- Eliminated issue when downloading data in environments with millions of vulnerabilities.
Invicti/Netsparker
- Updated ingest to better support deduplication of multiple assets scanned on the same date and time across multiple scans.
- Connector suddenly added whitespaces to scan files causing issues with scan processing. Improved the parser to handle this scenario.
Microsoft Defender
- Added last seen date field from Defender to Nucleus.
- Improved Defender threat intel processing.
- Updated connector to better handle changing IPs in dynamic environments.
- Changed display for assets with multiple machine tags in Defender to an array allowing for machineTag values to be accessed in Nucleus dynamic fields.
Nipper
- Applied better duplication knowledge.
Prisma Cloud
- Massively improved ingest speed.
Qualys
- Added functionality to handle a sudden change in Qualys’ report API so that jobs do not run forever.
- Enhanced connector to generate and download reports on a separate thread to the ingestion so that other scan ingestion jobs can download whilst Qualys scans are ingesting.
S3 Connector
- Adjusted S3 file sizes so they are as close to 16MB as possible to increase speed and efficiency.
- A bug where slow logic caused the S3 delta export to slow down scan ingests.
Security Hub Connector
- Improved ECR ingest speeds
- Implemented better rate limit handling to account for retries.
Snyk
- Eliminated issue where ingests were scheduling multiple imports in certain scenarios.
- Added additional metadata (SNYK Org ID and Org Name) which can now be used within automations in Nucleus.
Tanium
- Improved ingest speed when large numbers of assets are ignored.
Security Improvements
- Added an org level setting to log users out after a specified amount of inactivity in the console.
- By default, Nucleus app users are now automatically logged out after 60 minutes of inactivity. This setting can be adjusted at the organization level.
Bug Fixes
- A bug where Microsoft Teams displayed the instance count inaccurately.
- A bug in Amazon Security Hub prompting the creation of different scan date values per host/scan.
- A bug where uploading a video in the vulnerability information tab resulted in an error.
- A bug where removing assets from the asset management page resulted in an error in certain scenarios.
- A bug where the unique high-risk vulnerability metrics were timing out in certain scenarios.
- A bug where updating the status on multiple instances resulted in a timeout.
- A bug to prevent Dependabot timeouts when ingesting all scans.
- A bug where the vulnerability details were not loading in certain scenarios.
- A bug where creating a compliance summary report did not work in certain scenarios.
- A bug where some Prisma Cloud findings were showing as active instead of resolved in the event when a new ingest had 0 vulnerabilities and 0 compliance findings
- A bug where an error occurred on the Project Dashboard page on older browsers.
- A bug that caused periodic failures near the end of ticket processing, preventing all tickets from being fully updated. This periodic failure occurred when hundreds of ticketing rules existed in Nucleus and tens of thousands of downstream Jira or ServiceNow tickets were updated.
- A bug where comments added at the same time as the evidence file was uploaded, being deleted when the file was deleted from the instance.
- A bug in the “PUT Update Team” API endpoint where users were not added to a team in some cases.
- A bug where generating the vulnerability details report on the vulnerabilities view from the Asset Details page resulted in an error.
- A bug in the Update Teams API to return a more accurate status code and message when providing invalid parameters.
- A bug where compliance summary report types were not displayed in the reports list table on the reports page.
- A bug where mitigated statuses were not updated correctly for some connectors when updating multiple finding instances at once in the UI.
- A bug where creating a ticket in the instances tab of Nucleus resulted in some finding instances fields populated with the text ‘undefined’ instead of not populating at all.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.