Creative misuse and abuse of risk-based vulnerability management
Risk-based vulnerability management is a big buzzword in the security industry today. But what is it, really?
I was working with a large customer this month where risk based vulnerability management turned out to be an unexpected solution to a problem. It’s probably the most creative use of vulnerability intelligence I have seen yet. We are using it to assign tickets, of all things. Here’s how risk based vulnerability management provides unexpected help to this classic problem.
Which team should get this vulnerability?
The biggest challenge I see in large enterprises is figuring out how to assign vulnerabilities. It seems like it should be straightforward, but it rarely ends up being as easy as it seems.
In their case, the criteria were a bit complicated, but then someone realized they had just spent 5 minutes describing updates that have patches available. He interrupted himself and asked if Nucleus can trigger an automation rule based on patch availability.
Indeed, we are. And that criteria is in the last place you would think to look for it. The field is called Mandiant Mitigations, and the criteria you use is “Patch.”
There is an easy reason the criteria live in our threat intelligence functionality. Some network scanners flag their findings as patchable or not. But not all of them do. Our partner Mandiant provides mitigation data which we deliver to all Nucleus customers in the dashboard. This allows us to provide a similar user experience regardless of the source of your data.
And their logic for assigning vulnerabilities that way is simple but brilliant. If a patch is available, the infrastructure team can use an automated deployment tool to distribute a patch at a large scale and very quickly. You don’t want to assign work to a team before the patch is available, because they’ll just close the ticket and say there’s nothing they can do. This solves the problem by not assigning the work or starting the clock until the team can do something about it.
This also eliminates configuration changes, such as disabling obsolete cryptography like SSL and TLSv1. You can handle those separately.
Here’s what it looks like. First, key off the status and the Mandiant Mitigations.
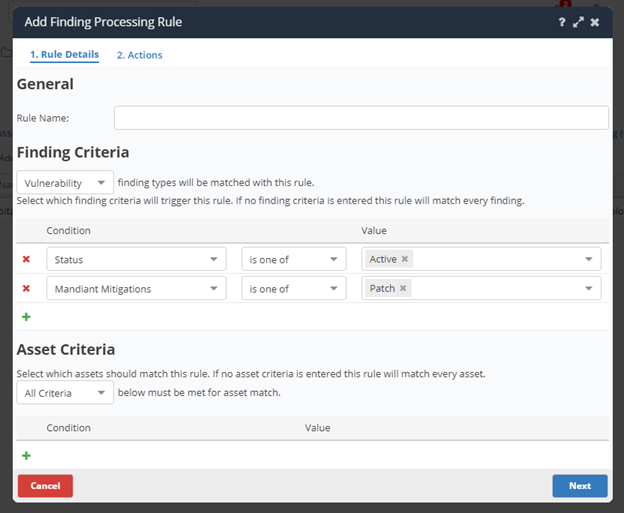
And then, under actions, assign the finding to a team, and flip the status to in progress.
If you need to fine-tune the rule, you can add additional criteria. This rule will likely work well, but you will get exceptions. Use keywords in the vulnerability name to manage those exceptions. Toggling the status helps to eliminate conflicts between similar rules.
Once you have this rule or set of rules made, you can work on defining rules for what remains.
Using the mitigations data more conventionally
You can also make use of the mitigations data in a more traditional risk based vulnerability management fashion. Let’s talk about 0days. Everyone worries about 0days.
You can use automation rules and similar criteria to manage those at scale. Mandiant also provides information about whether firewall rules or IPS rules exist as mitigations. Use automation rules to locate those findings, and then you can collaborate with the teams that administer your firewalls, IDS, or IPS to apply those mitigations. And yes, I did say IDS. If you don’t have an IPS but you do have an IDS, the existence of IPS signatures is a good indicator that IDS signatures exist as well, so your SOC can at least detect if anyone is trying to exploit the vulnerability on you.
Note that Mandiant doesn’t specify firewall types. If you have an older, traditional firewall, blocking the affected port is an option. But if you have a more modern firewall, you can load a more behavior-based signature that blocks malicious traffic while still permitting valid traffic.
Notice I didn’t say anything about antivirus signatures. I have reservations about relying too heavily on conventional antivirus when handling a high publicity 0day. If something goes wrong, you don’t want word getting out that you thought your antivirus was protecting you. Far be it from me to become the subject of a meme that says 1997 called and it wants its security back.
But if you have a modern EDR tool, if Mandiant says antivirus signatures are available, that is also a good indicator that EDR signatures will be as well. So, you could build a similar workflow involving your EDR tool and Mandiant’s antivirus flag.
Of course, if you have information directly from your firewall, EDR, or IDS/IPS vendor, you can absolutely come in and do this work manually. But letting a set of automation rules using Mandiant data take the first pass can save you some time.
The next time a high publicity 0day comes along, you can search for it in Nucleus by looking for the team it was assigned to. Work with the appropriate teams to load the non-patch mitigations into the firewall, IDS/IPS, and/or EDR tool. Then mark the vulnerability as mitigated, upload the evidence and add any other justification you need.
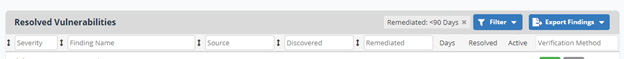
If anything changes, you can navigate to the resolved vulnerabilities, click on the column heading marked verification method, and type in the word Manual. This will search for the vulnerability you manually changed the status on and will narrow the list considerably. Then you can locate the vulnerability, click on it, and attach anything else you think you may need, such as to satisfy any audit requirements you may have.
This allows you to honestly say you have done as much as you can until the vendor releases a patch. Unless you really want to go the extra mile and test your mitigations using my red scanner technique.
Review the 0day periodically by once again navigating to the resolved vulnerabilities and searching for a verification method of Manual. Then, when a patch gets released, you can flip the vulnerability back to Active and let it progress through the regular workflow.
In theory, you could do this with an automation rule, but these happen infrequently enough that manual review is probably feasible, and these types of questions should be aided by a computer, not decided by one.
If you’ve made the investment in these types of technologies, this is how Nucleus allows you to factor them into your risk based vulnerability management approach. And when your organization must go through security assessments, being able to demonstrate that you have a process for handling 0days and locating the existence of potential compensating controls automatically, it could prove to be a competitive advantage for you. It’s also something that will impress auditors.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.
































