CISA BOD 26-02 and the Next Phase of Vulnerability Management

CISA recently published BOD 26-02, the latest Binding Operational Directive shaping how federal agencies manage cyber risk. While attention often gravitates toward highly visible directives like KEV, this one matters for a different reason: it raises the standard for how lifecycle risk must be tracked and sustained over time.
BOD 26-02 is described as guidance on unsupported edge devices, which is accurate but incomplete. The real shift is that unsupported systems are no longer treated as occasional cleanup items; they are part of the standing responsibility of operating a modern environment where exposure and accountability are constant.
Regulatory expectations rarely contract. They build, mature, and become embedded in day-to-day operations. This directive sets a new baseline, requiring agencies to demonstrate that they can continuously identify, track, and manage lifecycle risk across their infrastructure. Even as the industry focuses on AI and automation, the operational bar is rising just as quickly, with agencies expected to show sustained control and defensible decision-making year after year.
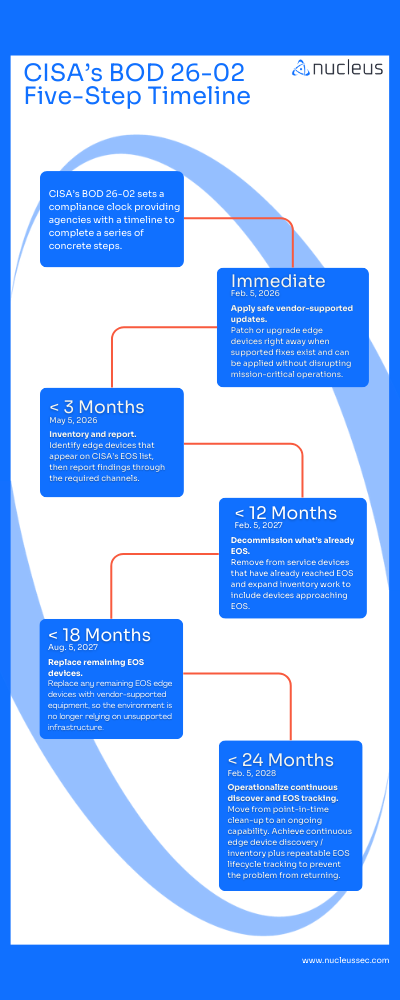
The structure of BOD 26-02 makes that clear. It moves from patching to inventory, to decommissioning and replacement, and ultimately to continuous discovery and lifecycle tracking. This movement signals that the goal is not a project with a finish line. It’s an operational capability that must endure.
What BOD 26-02 Says
The directive outlines a sequence of actions: apply supported patches where available, inventory and report unsupported assets, remove systems that are already out of support, replace what remains, and establish continuous discovery and tracking going forward.
Taken together, these steps reflect a shift in the operating model. Agencies are being asked to move beyond reacting to individual findings and toward maintaining a clear, current understanding of the lifecycle state of their environment, along with the ability to explain and justify the decisions that follow. Continuous discovery is not a minor detail at the end of the document; it is the mechanism that ensures lifecycle governance becomes durable rather than periodic.
CISA is effectively stating that unsupported systems cannot be reviewed once a year and filed away. Leaders must be able to show where those systems exist, how they intersect with exposure and active exploitation, and what tradeoffs are being made when immediate replacement is not feasible. This expands vulnerability management beyond scanning and patching into coordinated ownership, documentation, and cross-functional alignment, marking a meaningful evolution for both government programs and the discipline more broadly.
Announcing End of Life Operating System Tracking in the Nucleus Platform
This week, we launched automated End of Life and End of Support operating system tracking directly within the Nucleus platform, making lifecycle state a continuously calculated signal across your asset inventory and embedding it into the Nucleus Insights feed.
Vulnerability management has long focused on CVEs and patch timelines under the assumption that faster remediation steadily reduces risk. Unsupported infrastructure breaks that assumption. When software reaches end of support, there may be no patch path, and the issue shifts from speed to planning, coordination, and long-term modernization decisions across teams.
That is why lifecycle intelligence must sit alongside vulnerability intelligence as a core input into decision making. With this release, we are expanding the Nucleus Insights feed to include end-of-life and end-of-support asset data across all assets in the Standard Tier, with no upsell required, because vulnerability data and asset context are most effective when they operate together.
From the beginning, Nucleus was built to close the gap between findings and action. Lifecycle risk is one of the clearest examples of that gap, and bringing lifecycle state into the same decision layer as exploitation and vulnerability context allows teams to move from isolated fixes to coordinated, defensible decisions at scale.
A Roadmap Driven by the Problem, Not the Mandate
Long before BOD 26-02 was published, we had already operationalized KEV integration because exploitation context changes how organizations prioritize and communicate risk. At the same time, we built the platform on the belief that vulnerability intelligence is only as strong as the asset context around it, since knowing what is actively exploited must be grounded in a clear, current understanding of where those systems live and how they are used.
We were also investing in end-of-support tracking and broader lifecycle visibility because customers kept running into the same constraint: vulnerability data surfaced issues, yet unsupported systems created planning gridlock that required coordination across infrastructure, procurement, operations, and leadership. BOD 26-02 did not introduce a new problem for mature programs; it formalized one they were already working through, and our roadmap reflected that reality well before it became a mandate.
Moving Past Patch Speed
Security leaders are entering a period where patch speed alone will not define program maturity. Increasingly, they will be expected to demonstrate how decisions are made, how lifecycle risk is tracked over time, and how competing priorities are balanced across teams in a way that stands up to scrutiny.
Continuous lifecycle governance, clear prioritization, coordinated execution, and defensible tradeoffs are becoming baseline expectations. Edge end-of-support risk is one visible example, but similar pressures are emerging across cloud services, third-party software, and operational technology.
BOD 26-02 is one step in that direction. The broader trend is toward security programs that operate as integrated decision systems, capable of maintaining visibility, alignment, and accountability over time. Organizations that embrace that model early will not only meet regulatory requirements with less friction; they will build stronger foundations for whatever comes next.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.