How to Make Security Configuration and Compliance Easier
The pain of security configurations and how a new Nucleus feature helps harden systems faster than ever.

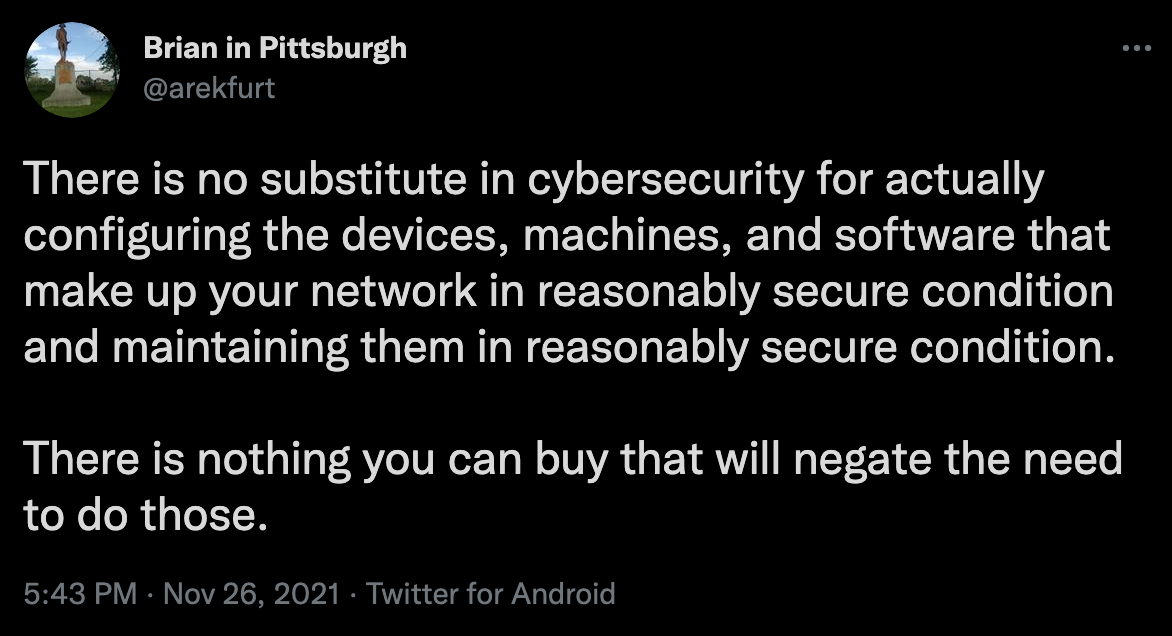
I saw a tweet over a holiday weekend about secure configurations. If I had to guess, an incident responder had their vacation interrupted and tweeted out of frustration that secure configuration, what Nucleus calls compliance, is not optional, and there is no product you can buy to get you out of this requirement. I agree with him completely, and I also understand why so few people do it. It’s really hard. Let’s talk about how Nucleus makes this job easier.
Everyone is looking for a silver bullet, and there is always someone who is willing to try to sell you that silver bullet. 10 years ago it was intrusion protection systems, or IPS. This year it’s extended detection and response, or XDR. And don’t get me wrong, they will do some useful things – but they are not a substitute for doing the basics. It’s the combination of patching and hardening and fancy tools that give you good security. Buying this year’s new security hotness and neglecting the basics is like putting a $100 lock on your front door while neglecting to close the latch on the window right next to the door.
Secure Configurations are Hard
I hadn’t worked in an organization that was happy with their secure configurations, no matter what name they called it. Nucleus is the exception, because we are a young enough company able to incorporate that into our initial design rather than bolting it on afterward. Everyone else had names for it, and I don’t necessarily mean compliance or policy compliance. The names were generally less HR friendly than that.
Prior to joining Nucleus, the last place I worked that did system hardening well was way back in 2009. And even there, I had my critics. I was the one doing the hardening and did a pretty good job. I achieved 99% compliance, and the 1% I didn’t accomplish was due to limitations in the software we were using at the time. There was no way we were going to get above 99% without making a significant change to our technology stack. During the times when we briefly dipped below 99%, I wished I could get us back to 99% faster.
Just slightly over 1000 miles away, a security analyst named Steve Carter was building what became Nucleus because he was experiencing similar problems.
Eliminating Unanswered Questions in System Hardening
The problem we both had, especially as high-performers by most standards, was managing unanswered questions. New systems would hit the wire without the right people knowing about them, and they would sit on the wire for a few hours or even a few days before the right person found out about them and finished securing them. When you get to the point where you have 99% compliance, the question always remains whether you implemented the right 99%. That was always the question I needed to answer – and in my case, the answer was pretty easy. My standard required me to run antivirus software, and it wanted me to disable legacy 8.3 filenames. The problem was, disabling the 8.3 filenames broke the antivirus software.
That was always a short discussion. But even then, Nucleus would have helped, because I could have uploaded the reasoning behind the decision to that security control, along with whatever other paperwork we had. That way, anytime someone felt frisky and decided they were going to try to get that last 1%, they would have all the information they needed.
And the thing is, when you have two contradictory security controls like that, it’s not always so cut and dry. In my case, no question disabling 8.3 filenames was a low (priority?) The only point you can argue is how low. Anybody would argue that running antivirus isn’t a low – most would probably say it’s a critical requirement. I know a guy who would say antivirus isn’t critical, but even he would say it’s a higher priority than 8.3 filenames. It is entirely possible the two conflicting controls could be much closer in severity. If nothing else, Nucleus provides an objective third party opinion to help you decide. And every year when you review it, Nucleus will be able to tell you if it has changed its mind.
Now let’s talk about the second-best approach I have seen to system hardening. Back when I was working at one of the scanner vendors, I had a customer who told its IT departments to implement 80% of the relevant standards from the Center for Internet Security (CIS) for their platform. They didn’t even say which 80%. As long as a scan said 80% of the controls passed, they were happy. I thought it was a pretty smart approach. It’s not perfect, of course, but they got 80% more compliance than most hardliners get. Like I tell my kids sometimes, getting part of what you want is always better than getting none of what you want.
The problem with that 80% approach may have been that it was too flexible. There were some people in the IT department who just didn’t believe it. They were fine with implementing 80%, but they wanted at least a little bit of guidance on which 80%, if only to provide them some top cover if anything ever went wrong. If there was ever an incident, and someone pointed out that a certain security control wasn’t implemented, they didn’t want it coming down on them.
If they had Nucleus, they could eliminate the second guessing. If you sort the controls by severity and implement the top 80%, it’s going to be very hard for anyone to fault you. Or they could adopt a VM-like model and tell teams to implement the highs and criticals.
How Nucleus Helps Harden Systems Faster
Besides bringing all of your security controls into one place and providing a friendlier, more consistent interface and a place to upload evidence and reasoning, Nucleus also allows you to work much faster. It was easy enough for me to justify my 99% compliance even though there was always that one guy who wanted that last 1%. The speed at which I came into compliance was certainly one place where we could have done better.
What I ran into is a problem that is familiar to anybody in security. New systems would come on line, everyone thought that everyone else knew, but somebody who was responsible for some critical step, usually security related, didn’t know. We had as many of our security controls loaded into Windows group policy as we could, so that was nice. When you plugged the system into the network, it was immediately 95% compliant. But that last 4% lingered until someone told me. There were always a few things that couldn’t be done through group policy. Ideally, it was one of the other sysadmins who told me – sometimes it was a very unhappy security analyst who told me.
But imagine this scenario: a new system hits the wire, and not everyone who was supposed to know actually knows about it. The system gets scanned, and the scanner syncs with Nucleus. Nucleus updates the system inventory automatically. And then Nucleus cuts a ticket for everything wrong with the system and sends that to the person who needs to know about it. That person sees the ticket, does the work, initiates another scan, and when the scan comes back clean, Nucleus closes the ticket. The security analyst doesn’t have to get involved at all, unless the agreed upon due date gets too close.
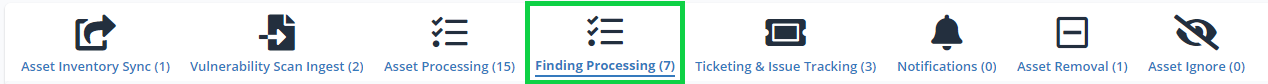
The ability to open tickets on compliance findings was one of the features we added to Nucleus in November. The sharp-eyed among you may notice in our automation section, Vulnerability Processing changed its name. It’s now Finding Processing, and you can create rules for vulnerability findings, compliance findings, or both. You may have a different SLA on compliance.
The ability to create tickets on compliance findings adds significant new capability to Nucleus, making what has always been a difficult task for security teams much easier than it was even a month ago.
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.