TRUSTED BY ORGANIZATIONS WORLDWIDE
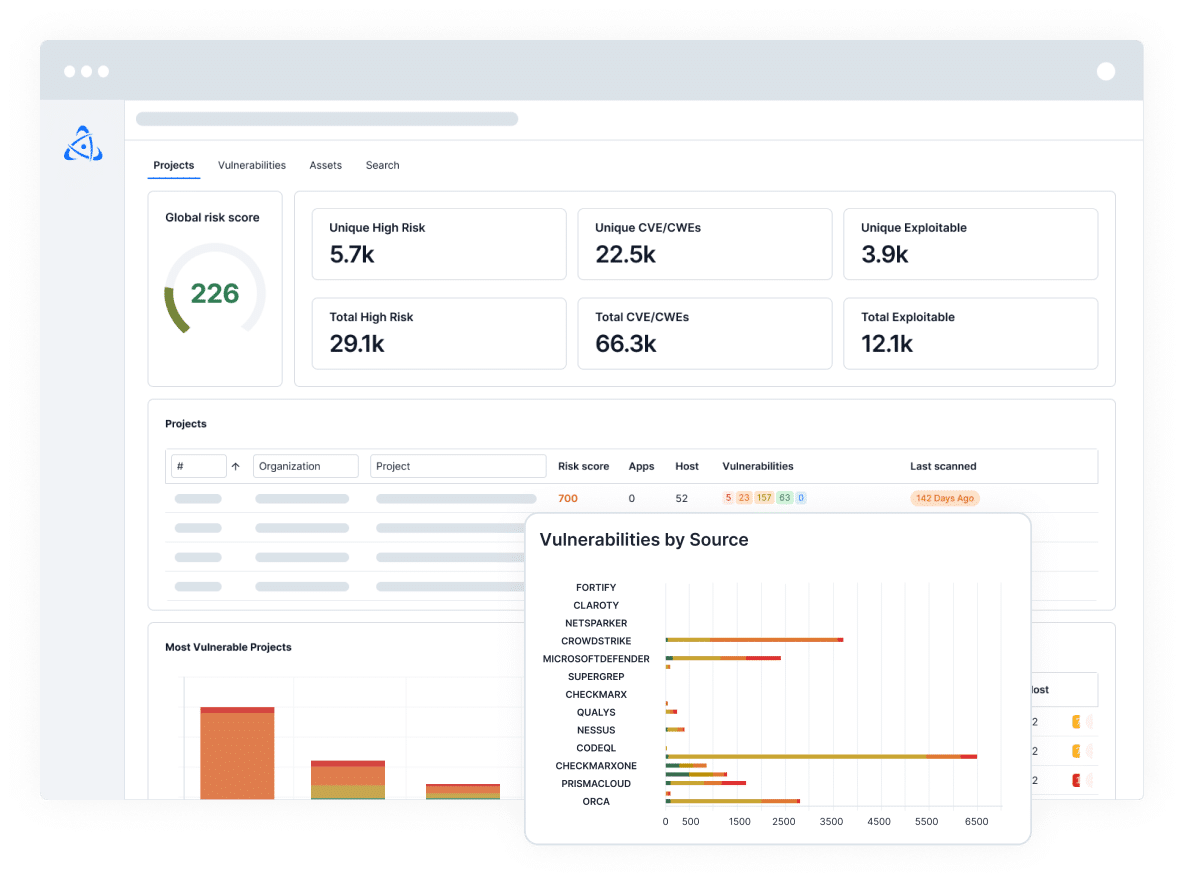
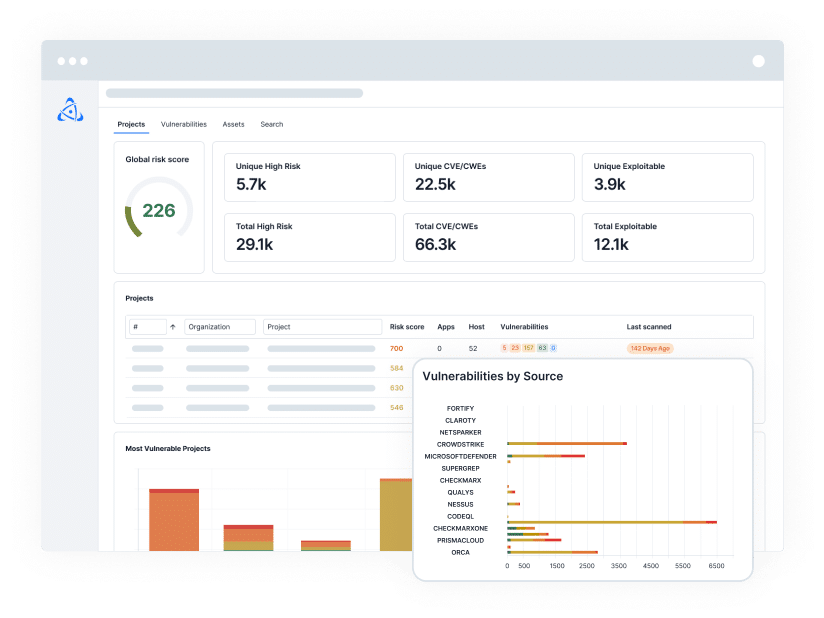
Accelerate and Scale Your Vulnerability Management Program
Scale Remediation with Precision
Automate risk-based workflows: Prioritize, ticket, track, and continuously update stakeholders about critical exposures.
Assign the Right Owners
Operationalize metadata to automate and adapt complex ownership hierarchies to assign tickets faster with precision.
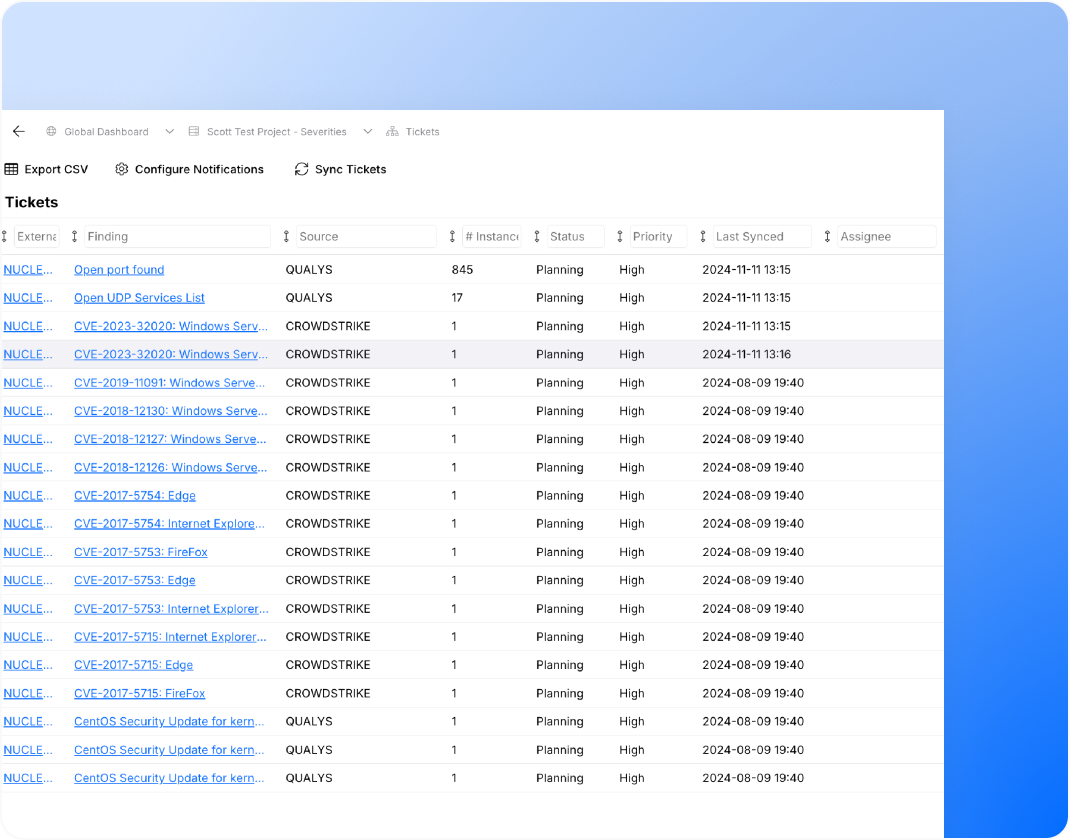
Integrate Your Ticketing
Track the status of tickets with bi-directional integration and update as soon as new data is ingested or a status changes.
OWNERSHIP ASSIGNMENT
Assign Tickets to Owners, Automatically
Automatically assign tickets to the right teams and users. Operationalize ownership metadata in the Nucleus Dynamic Automation Framework to continuously adapt ownership assignment as the business evolves.
TICKETING INTEGRATION
Stay Up-To-Date On Ticket Status
Adjust the importance of risk factors based on your business needs instead of relying on a black-box solution. Nucleus will automatically recalculate all your risk scores and update your top risks.
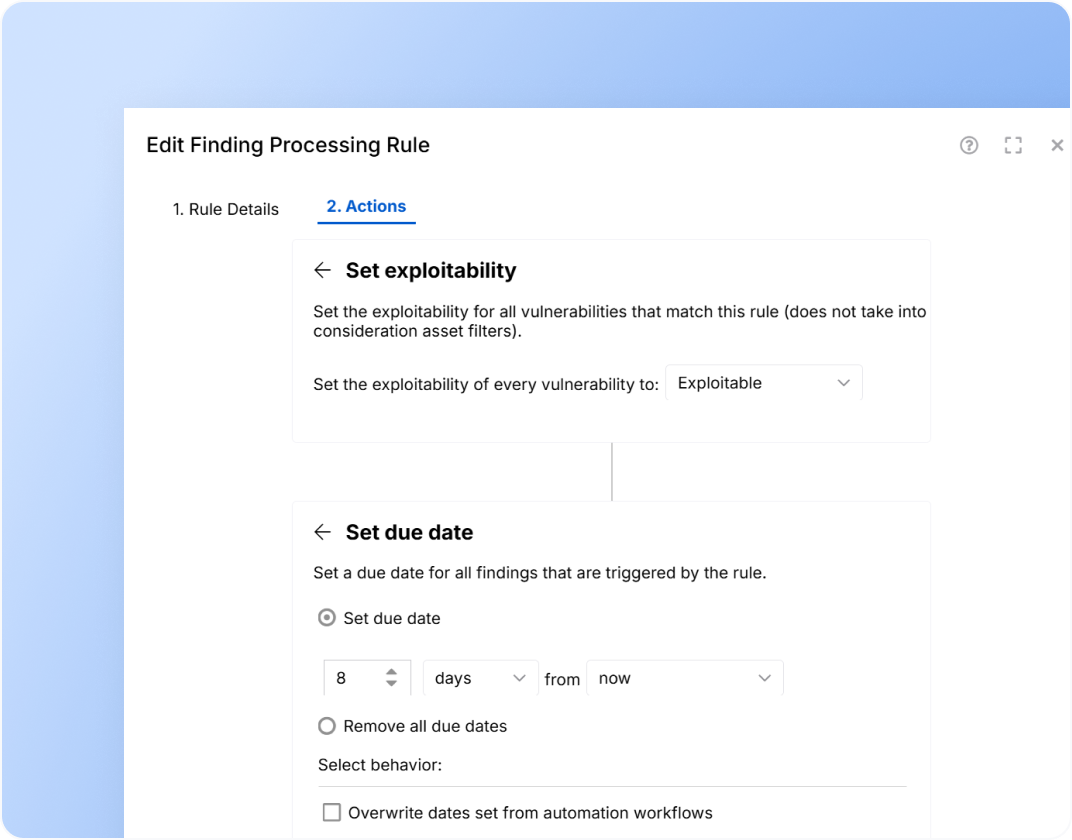
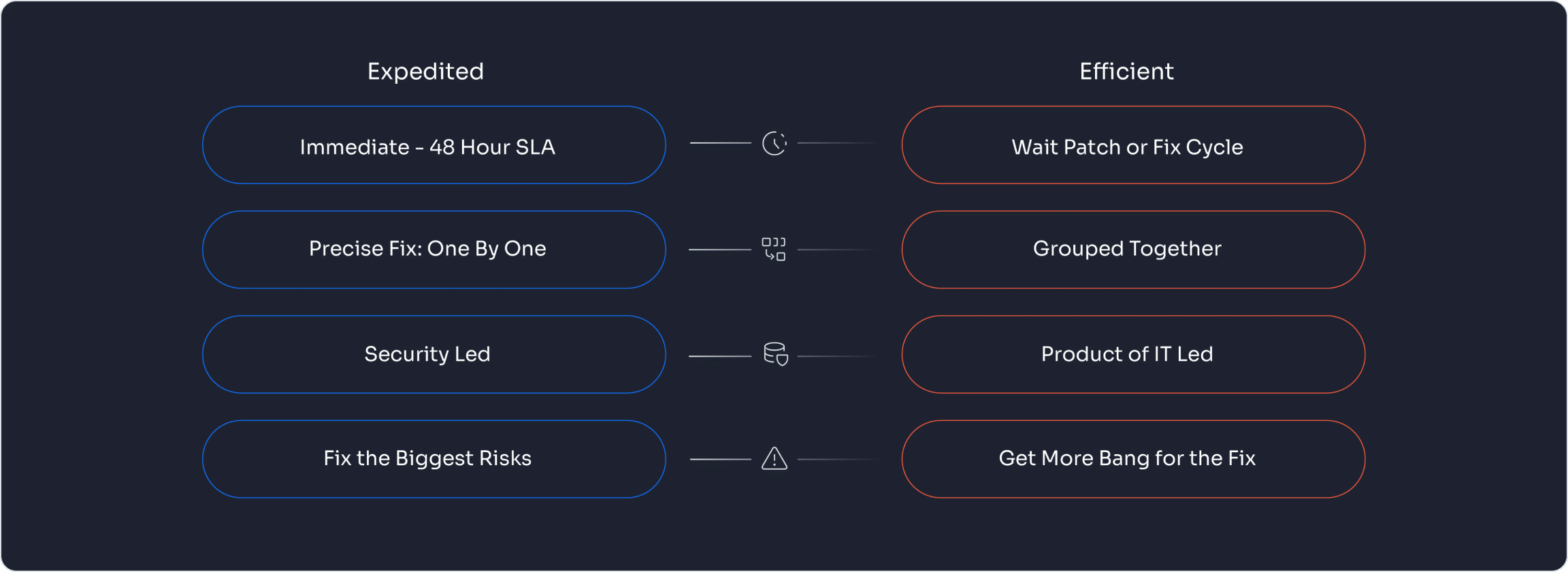
EXPEDITED AND EFFICIENT REMEDIATION
Two Strategies to Remediate Vulnerabilities Faster and Smarter
Nucleus enables you to prioritize high-risk vulnerabilities with precision — and group lower-risk issues by fix or sprint for efficient remediation.
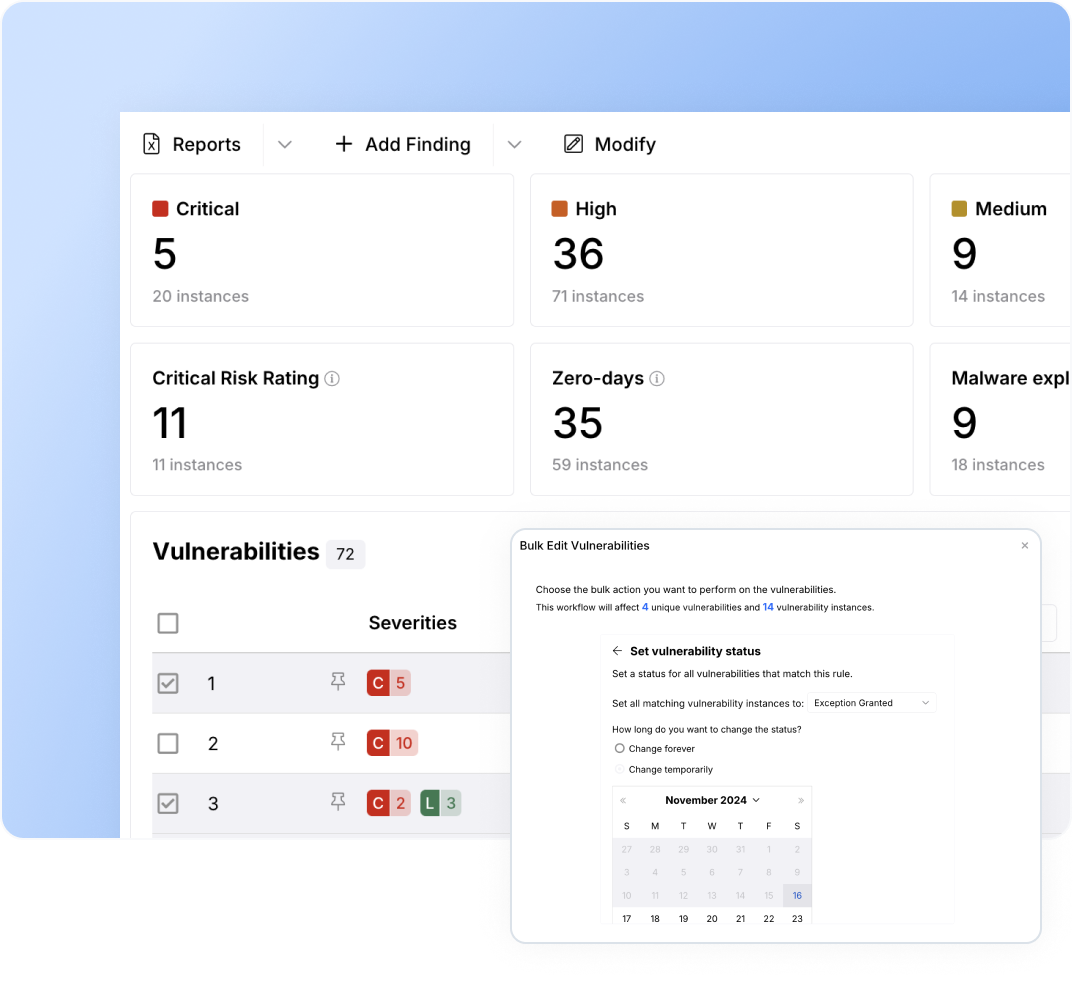
EXCEPTION HANDLING
Accept Risks and Manage Exceptions
Set time limits and document approvals to ensure every risk exception is managed responsibly. With Nucleus, exceptions remain active and fully tracked as new scan data is ingested and updated.
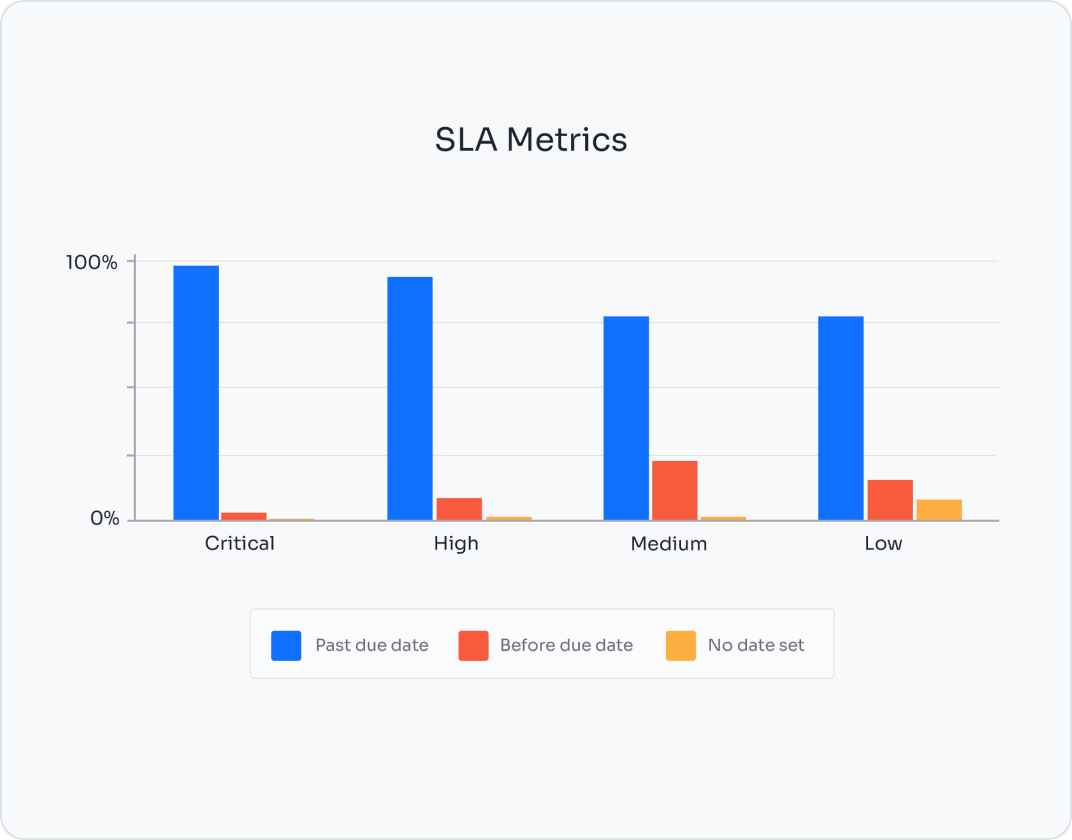
SLA TRACKING
Track Resolutions Against SLAs to Measure and Communicate Performance
Define your SLAs and monitor ticket status and resolutions over time to measure and communicate performance. Trigger automated reports to align with key milestones or audit requirements, ensuring effective management of your vulnerability program.
Frequently Asked Questions
How do I strategically prioritize vulnerability remediation?
Effective prioritization is about reducing measurable business risk, not simply fixing the highest CVSS scores.
A strategic model balances four factors:
- Exploit Reality. Is the vulnerability actively exploited? Is exploit code available? Is it listed in authoritative threat sources?
- Business Impact. Does the affected asset support revenue, regulated data, or mission-critical operations?
- Exposure. Is the system internet-facing? Internally segmented? Privileged?
- Remediation Feasibility. Is a patch available? Can compensating controls reduce risk?
Organizations that mature beyond severity-only models move toward risk-based prioritization, aligning remediation to threat likelihood and business consequence. Clear risk tiers with defined SLAs ensure consistency and accountability.
What is the best way to map vulnerabilities to business risk?
To translate technical findings into business risk, organizations must connect vulnerabilities to operational impact.
A structured approach includes:
- Asset Criticality Classification. Identify which systems are customer-facing, revenue-generating, or subject to regulatory oversight.
- Ownership and Accountability. Assign both business and technical owners to each asset.
- Contextual Risk Scoring. Incorporate factors like severity, exploit probability, active exploitation signals, asset criticality, and exposure level into your risk scoring. This creates a risk score that reflects organizational priorities rather than generic industry benchmarks.
- Executive Reporting Alignment. Report vulnerability exposure in business terms. This can include financial risk, regulatory exposure, and the potential for operational disruption. When vulnerability management is framed in enterprise risk language, it becomes a strategic function rather than a technical exercise.
Are there more efficient alternatives to manual vulnerability triage?
Yes. Manual triage does not scale in modern environments.
High-performing programs reduce manual effort through:
Automated and Customizable Risk Scoring
Dynamic prioritization that adapts to threat intelligence and asset context.
Workflow Automation
Automatic ticket creation, assignment, SLA setting, and escalation based on defined risk thresholds.
Structured Exception Management
Formal risk acceptance workflows with documented approvals and expiration dates.
Continuous Risk Re-evaluation
Automated reassessment when threat conditions change.
The goal is to shift from reviewing every finding manually to managing risk through policy-driven automation and intelligence signals.
How do I track remediation for FedRAMP, NIST, and other regulatory requirements?
Regulatory frameworks require evidence of discipline, timeliness, and governance.
To meet compliance expectations:
- Align SLAs to Framework Requirements. Define remediation timelines by severity consistent with regulatory guidance.
- Monitor Aging and Exposure. Track open findings by severity, overdue items, mean time to remediate (MTTR), and exception counts.
- Maintain an Audit Trail. Document factors like discovery date, assignment, remediation, risk acceptance, and approval history.
- Demonstrate Continuous Monitoring. Show consistent scanning cadence and ongoing risk reduction over time.
Compliance success depends on demonstrating a repeatable, measurable remediation process, supported by clear reporting and governance controls.
BLOGS
Discover the Latest From Nucleus
See Nucleus in Action
Discover how unified, risk-based automation can transform your vulnerability management.