CISA Known Exploited Vulnerabilities Breakdown
September 08, 2022 – 12 New Vulns
With CISA’s BOD 22-01, CISA maintains a catalog of CVEs which are known to be exploited in the wild. Within the catalog, CISA mandates that the most urgent vulnerabilities be patched within 2 weeks, and the least urgent within 6 months. The recent releases included 12 new additions from September 8th.
In this Breakdown, our vulnerability research team found that 5 of the 12 additions impact home and/or small office devices, and should be of minimal concern to most businesses. We have found four notable additions included in this release: Google Chromium Insufficient Data Validation, Oracle WebLogic RCE, Apple TCC Database Bypass, and QNAP Photo Station Externally Controlled Reference.
To get a better understanding of each component of our Breakdown, including what we determine to be a notable release, please see our Frequently Asked Questions section below. Also be sure to follow Nucleus Security on Twitter and LinkedIn where we will posting each time a new Breakdown is released.
| wdt_ID | CVE ID | Software | Vendor | Exploitation Result | Due Date | EPSS Probability | EPSS Percentile | GreyNoise |
|---|---|---|---|---|---|---|---|---|
| 1 | CVE-2022-3075 | Chromium | Logic Bypass | 9/29/2022 | 0 | 0 | 0 attempts | |
| 2 | CVE-2022-28958 | DIR-816L | D-Link | Remote Code Execution | 9/29/2022 | 0.01978 | 0.78454 | 0 attempts |
| 3 | CVE-2022-26258 | DIR-820L | D-Link | Privilege Escalation | 9/29/2022 | 0.05634 | 0.89779 | 0 attempts |
| 4 | CVE-2020-9934 | iOS, iPadOS, and macOS | Apple | Configuration Bypass | 9/29/2022 | 0.02164 | 0.79205 | 0 attempts |
| 5 | CVE-2018-7445 | RouterOS | MikroTik | Remote Code Execution | 9/29/2022 | 0.12131 | 0.94987 | 0 attempts |
| 6 | CVE-2018-6530 | Multiple Routers | D-Link | Command Injection | 9/29/2022 | 0.01213 | 0.65579 | 0 attempts |
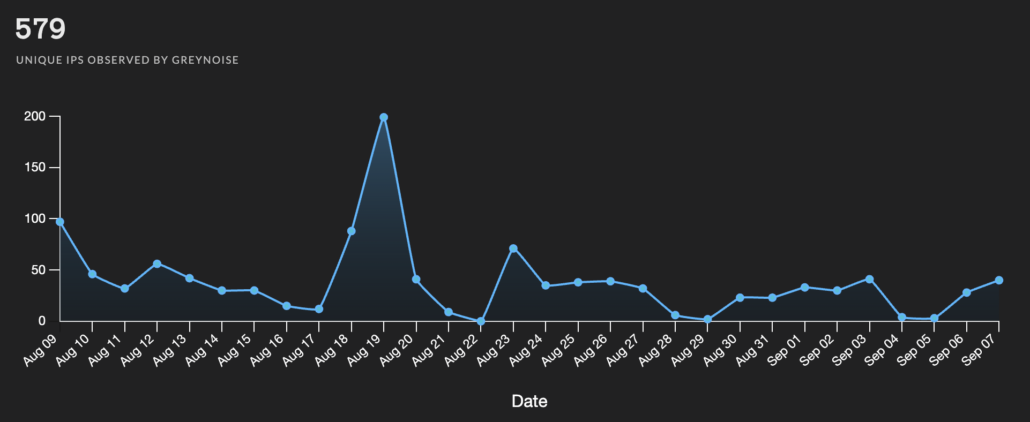
| 7 | CVE-2018-2628 | WebLogic Server | Oracle | Remote Code Execution | 9/29/2022 | 0.94899 | 0.99958 | 579 attempts |
| 8 | CVE-2018-13374 | FortiOS and FortiADC | Fortinet | Improper Credential Access | 9/29/2022 | 0.07308 | 0.9217 | 0 attempts |
| 9 | CVE-2017-5521 | Multiple Devices | NETGEAR | Authentication Bypass | 9/29/2022 | 0.89853 | 0.99832 | 0 attempts |
| 10 | CVE-2011-4723 | DIR-300 Router | D-Link | Cleartext Password Access | 9/29/2022 | 0.00885 | 0.26191 | 0 attempts |
| 11 | CVE-2011-1823 | Android OS | Android | Privilege Escalation | 9/29/2022 | 0.02172 | 0.79389 | 0 attempts |
| 25 | CVE-2022-27593 | Photo Station | QNAP | System File Modify | 9/29/2022 | 0 | 0 | 0 attempts |
| CVE ID | Software | Vendor | Exploitation Result | Due Date | EPSS Probability | EPSS Percentile | GreyNoise |
Notable Vulnerability Additions
CVE-2022-3075 | Google Chromium Insufficient Data Validation
A zero-day was discovered, making #6 this year for Google Chrome, in which there is insufficient data validation in Mojo. Mojo is a massive set of libraries used in the Chromium codebase, which is what Chrome is largely based on.
It is important to note regarding CVE-2022-3075 specifically, this vulnerability was disclosed to Google August 30, shortly after a large haul of security fixes in an update shortly before. This CVE was put it in its own patch cycle and pushed out as an emergency fix, putting Chrome on version 105.0.5195.102. Nucleus Security recommends to apply this patch as it is clear the evidence of exploitation was plain enough for it to be added to the KEV. For those with Microsoft Edge (which is Chromium-based) in their environments, a Microsoft advisory link is added below as well as the advisory from Google.
Security Advisory:
https://chromereleases.googleblog.com/2022/09/stable-channel-update-for-desktop.html, https://msrc.microsoft.com/update-guide/vulnerability/CVE-2022-3075
CVE-2018-2628 | Oracle WebLogic RCE
It should come as no surprise to see CVE-2018-2628 added to the KEV as well as coming in the top 0.00042% of all EPSS vulnerabilities in probability of exploitation. At the time of disclosure on April 21 by KnownSec 404, there were around 36,000 vulnerable WebLogic servers facing the internet. WebLogic servers have historically been a prime candidate for hackers, especially cryptominers.
This vulnerability continued to ache the heads of security professionals as it took no less than a day post-patch to be maneuvered around and exploited again. As early as April 27 (the patch was released April 26) there was further scanning activity detected with new forms of the exploit which bypassed the implemented blocklist put in place with the issued security patch. An in-depth technical analysis by Apostolos Giannakidis released in May of 2018 shows why a blocklist is an ineffective form of remediation, especially for CVE-2018-2628 specifically.
As of current time, this vulnerability is the only of today’s KEV additions to be detected in recent scanning activity across the internet, according to Greynoise Trends.
Security Advisory:
https://www.oracle.com/security-alerts/cpuapr2018.html
CVE-2020-9934 | Apple TCC Database Bypass
CVE-2020-9934 is one of a list of discovered weaknesses in the core functionality of Transparency, Consent, and Control (TCC) and how it communicates with its related databases. Security researcher Matt Shockley discovered the flaw dubbed CVE-2020-9934, in which a method of poisoning the environment variable which reads the TCC.db file can allow for a read-only user to establish all TCC entitlements, without ever prompting the end user. It should be noted that this exploit was accomplished with no lines of code needed. Simply, the flaw existed in that a mirror directory, when made the home environment variable, caused for the TCC.db file to reach out to this malicious directory with no fuss.
This CVE, much like CVE-2018-2628 noted above, was one of many related to TCC weaknesses that were patched by Apple. However, research from MSVR (Microsoft Security Vulnerability Research) from January 10 of this year shows the potential for a bypass to exist. Highlighting what is found in their research as the “powerdir” vulnerability, “While the solution indeed prevents an attack by environment variable poisoning, it does not protect against the core issue. Thus, we set out to investigate: can an app programmatically change the user’s home directory and plant a fake TCC.db file?” See the full report here, where the tug-of-war to find new ways to exploit TCC with each patch released is discussed in more detail.
Security Advisory:
https://support.apple.com/en-us/HT211288, https://support.apple.com/en-us/HT211289
CVE-2022-27593 | QNAP Photo Station Externally Controlled Reference
This vulnerability in Photo Station appears to be very recently disclosed, and a quick turn-around to be added to the KEV. According to a piece on attackerKB, it is important to note that CVE-2022-27593 is reportedly being exploited in the wild by the Deadbolt ransomware crew. This is backed up by reporting done by bleepingcomputer on September 5. According to the security advisory, QNAP suggest replacing Photo Station with QuMagie, which is a safer photo storage management tool for QNAP NAS devices. The report goes on to suggest Deadbolt has notoriously targeted NAS devices numerous times this year with zero-day exploits resulting in ransomware incidents.
From QNAP themselves, “We strongly urge that their QNAP NAS should not be directly connected to the internet. We recommend users to make use of the myQNAPcloud Link feature provided by QNAP, or enable the VPN service.” See more from their notice regarding the update here.
Security Advisory:
https://www.qnap.com/en/security-advisory/qsa-22-24
Frequently Asked Questions
- What makes for a notable addition?
- A notable addition can arise from many different characteristics. If a particular vulnerability is notable to the security community or a subset of the security community or if the EPSS score reveals notable information about the vulnerability, this can constitute further analysis. It may also be the case that a particular vulnerability shines a light on everyday users and we will highlight important information and key takeaways to ensure users and readers have easy access to actionable information.
- When is the Breakdown released?
- We aim to have our analysis of each KEV update posted within 24 hours of the time in which the Catalog is updated. See CISA’s full catalog here
- I am not bound by BOD 22-01 or federal regulations, why should the KEV concern me?
- CISA encourages all organizations to utilize the Catalog as an attribute in your vulnerability prioritization framework. Organizations looking to lessen the scope on known dangerous vulnerabilities and make a goal to remediate them can understand where they currently stand against what CISA has confirmed as exploited vulnerabilities in the wild. See CISA’s section on “How should organizations use the KEV catalog?” here.
- What is EPSS?
- EPSS is the Exploit Prediction Scoring System. It is an open, data-driven effort for estimating the likelihood (probability) that a software vulnerability will be exploited in the wild. See the EPSS home page on FIRST for more information here.
- What is the difference between EPSS probability and EPSS percent?
- EPSS probability is the risk calculated by the model when determining the perceived threat of the vulnerability itself. Percentage is a relative comparison of the rest of the CVEs within the given sample. While the probability only changes upon refreshing the results from the model, the percentage can change purely based on the CVE sample given. In the case of the Breakdown, we use the percentage given by the pool of all CVEs with given EPSS data. Scores may vary post-release of the post given new information about the vulnerabilities and their perceived threat. For more information on applying and understanding EPSS data, see this article on the FIRST website, as well as their FAQ page.
- What is GreyNoise?
- GreyNoise is a platform that collects, analyzes, and labels data on IPs that scan the internet and saturate security tools with noise. Through their sensor network, GreyNoise observes vulnerability exploitation attempts for vulnerabilities that are exploited in the wild over the Internet. These are arguably vulnerabilities that should be at the very top of your priority list to remediate.
- Why are GreyNoise exploitation attempts only observed on ~20% of KEV vulnerabilities?
- Exploitation of many vulnerabilities in the CISA KEV will not be observed for many reasons that GreyNoise does a good job of explaining in this post. For example:
- The vulnerability may not be remotely exploitable
- Vulnerability exploitation may require authentication (and result in privilege escalation)
- The impacted software may not be exposed to the internet
- Mass scanning/exploitation is not occurring yet
- Exploitation of many vulnerabilities in the CISA KEV will not be observed for many reasons that GreyNoise does a good job of explaining in this post. For example: